365 Total Protection honored with Computing Security Award 2020
Hornetsecurity has reason to celebrate, as its 365 Total Protection service was named as the winner in the “Editor’s Choice” category.
Hornetsecurity’s 365 Total Protection Suite offers email security management specifically designed for Microsoft 365 accounts. M365 customers benefit from fully comprehensive protection as well as simplified IT security management.
The editors of UK magazine Computing Security recognized 365 TP as a highly efficient solution that complements Microsoft’s cloud service with critical security mechanisms.
Microsoft 365 as target of cyberattacks
Microsoft 365 is used by over one million companies worldwide. In the US alone, more than 650,000 companies rely on the software in their day-to-day operations. Vast amounts of sensitive data are exchanged in the Microsoft 365 cloud every day. Cybercriminals are also aware of this. The company reported a 250 percent increase in targeted attacks as early as the beginning of 2020.
If you also consider that 95 percent of all cyberattacks on companies start with an email, then it becomes clear: the right protection for email communication is extremely important, and 365 Total Protection is the ideal solution.
365 Total Protection is Editor’s Choice of the Year
The award is based on a detailed test of the product, which can be downloaded free of charge.
The editors‘ summary states:
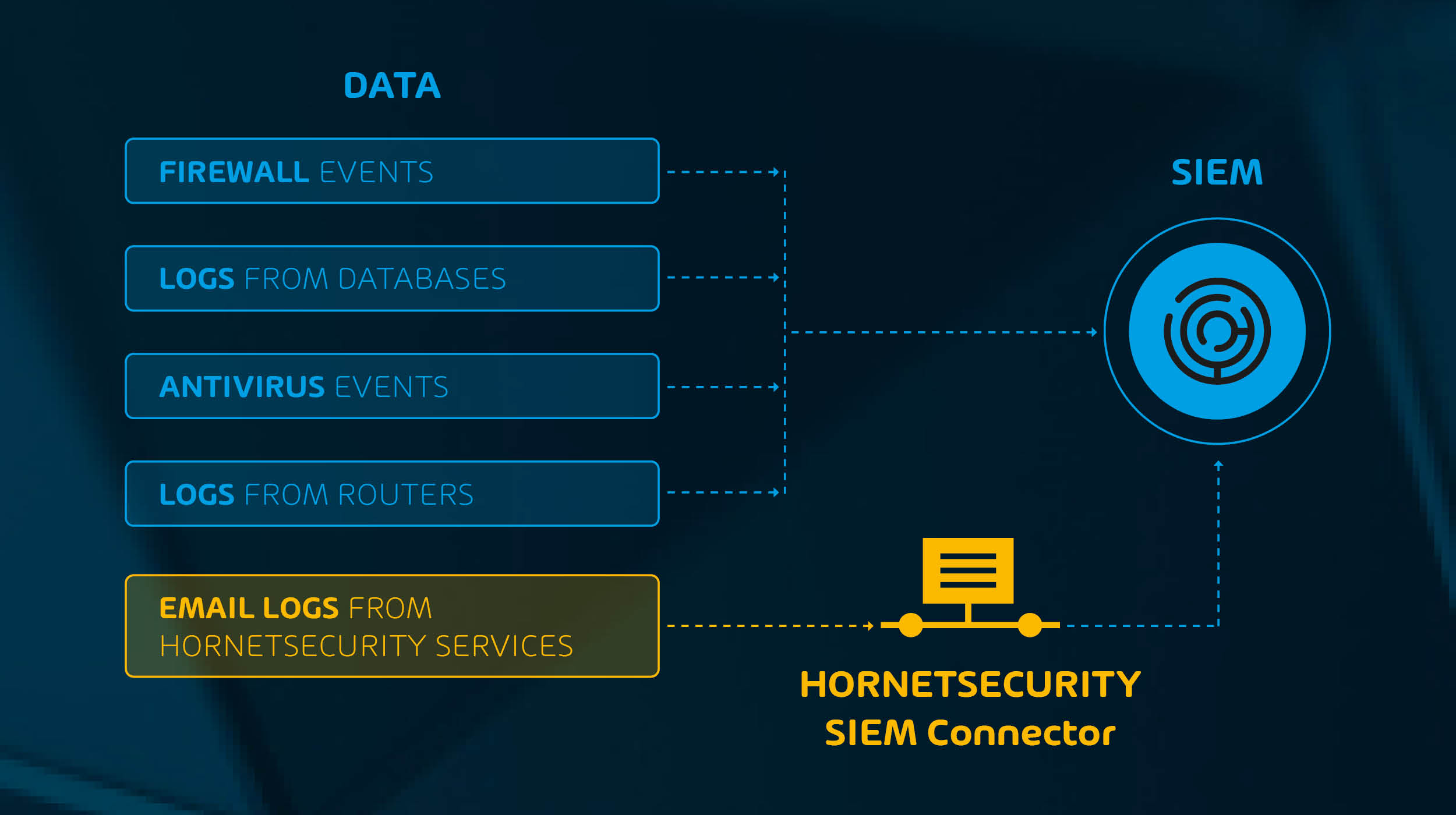
365 Total Protection combines all the necessary security features that a fully comprehensive email security management requires. These include Email Live Tracking, Threat Defense and Global S/MIME & PGP Encryption. In the Enterprise version, additional features such as Malware Ex-Post Alert, ATP Sandboxing and email archiving are added. The company uses intelligent filter mechanisms in its protection solutions, which enable efficient detection and filtering of any cyber threats via e-mail.
Computing Security Magazine therefore concludes its assessment as follows: “Hornetsecurity’s 365 Total Protection lives up to its name, as it delivers a smart email security solution that integrates seamlessly with Microsoft 365. It fills the security holes Microsoft leaves behind, and with prices for the Business version starting at only $2 per user per month, is affordable for organizations of all sizes.”
Further Information:
- Fully comprehensive Microsoft 365 email security protection
- Blogarticle: Office 365: Account Hijacking, the number 1 security risk?