

Where Cyber Threats Are Headed and Why Businesses Must Act Now
In 2026, it’s obvious the threat landscape isn’t just “getting worse” — it’s changing shape. Fresh research from our Security Lab shows that our cybersecurity predictions weren’t dramatic enough: risk is compounding faster than most defenses are maturing.
AI is no longer a futuristic concept; it’s a present-day force multiplier for attackers, helping them automate tasks that once needed time, skill, and a lot of luck. While many organizations are still figuring out how to use AI safely, cybercriminals are already industrializing it, turning evolving cyber threats into scalable operations.
In this article, we unpack the Security Lab’s 2026 cybersecurity predictions and translate them into practical next steps. We’ll show how AI misuse, Ransomware 3.0, fragile identity controls, SaaS and browser exposure, and even quantum risks are reshaping the cyber threat landscape.
More importantly, we’ll connect each prediction to concrete actions, so your defenses keep pace with the evolving threat landscape instead of lagging a year behind.
The Security Lab’s 2026 Predictions
Uncontrolled Adoption of AI Tools
Governance Falling Behind
As AI tools continue to mature, adoption across organizations is accelerating, often more quickly than governance or security frameworks can adapt. This acceleration is led by both management-led initiatives as well as grassroots experimentation by employees, and new AI solutions are being deployed daily in some cases. The pace of innovation has outstripped the ability of legal, IT, and security teams to evaluate each implementation, leaving critical visibility gaps.
Expanding The Attack Surface
Uncontrolled adoption effectively expands the organizational attack surface. Many AI tools, particularly those powered by large language models (LLMs), lack the separation between code and data inherent in more traditional applications. This introduces new vectors for prompt injection, data leakage, and unintended disclosure of sensitive corporate data. The rise of agentic AI compounds this risk, as autonomous actions can occur without human oversight or established approval chains.
Evidence Of Residual Exposure
Recent vulnerabilities such as Echoleak in M365 Copilot (Aim Labs) really show the seriousness of these risks. Unlike buffer overflows or code injections, LLM-based exploits don’t have straightforward mitigations. Even following best practices from the OWASP LLM01:2025 Prompt Injection guidance, organizations face residual exposure due to the unpredictability of AI model behavior. Reports such as “Detecting and Countering Misuse of AI” (August 2025, Anthropic) further confirm that even state-of-the-art models remain susceptible to manipulation and abuse.
Weaponization of Agentic AI
Agentic AI Threat Escalation
It should come as no surprise then that agentic AI systems (autonomous models capable of executing multi-step goals) are already being weaponized. The line between automation and orchestration has blurred. Attackers can now script, adapt, and launch multi-vector campaigns with minimal expertise, lowering the barrier of entry. These models can support every stage of the attack lifecycle, from reconnaissance to exploitation to impact, following the MITRE ATT&CK framework end-to-end.
Criminal Use Cases Emerging
One doesn’t have to look very far in online search to find cases where agentic AI has started to make an impact on threat-actor operations. These cases contain techniques like crafting phishing lures, bypassing CAPTCHA gates, or impersonating humans through voice and video deepfakes. These findings confirm what many defenders already suspect: AI is amplifying both the accessibility and velocity of cybercrime.
Safeguards Falling Behind
Despite safety claims from major vendors, misuse persists. Anthropic’s own August 2025 threat report acknowledged ongoing model abuse for reconnaissance and payload generation, validating the concern that agentic AI systems will continue to outpace safeguards. With LLMs capable of “vibe coding” entire attack chains autonomously, the barrier to entry for sophisticated exploitation has all but vanished.
Ransomware 3.0: LLM-Driven and Integrity-Focused
Automation And Data Corruption
As discussed in our 2025 ransomware survey findings, ransomware operations are entering a new evolutionary phase. This phase is defined by automation, autonomy, and data corruption. In 2026, we expect to see the emergence of LLM-driven orchestration, where large language models coordinate reconnaissance, payload generation, and adaptive evasion. Simultaneously, attackers are shifting from encryption or exfiltration to data integrity manipulation: altering, corrupting, or subtly falsifying records to create doubt in the trustworthiness of data itself.
Compromising Trust Instead Of Access
Historically, ransomware has evolved in response to defender resilience. Think encryption-only attacks (Ransomware 1.0) to double extortion (Ransomware 2.0). With widespread adoption of immutable backups and cyber insurance, direct encryption attacks are yielding diminishing returns. The next logical step for cybercriminals is to compromise trust rather than access. Manipulated data in financial systems, medical records, or industrial controls creates prolonged chaos, regulatory exposure, and reputational damage.
Proof Of Concept Progression
Academic research has already demonstrated proof-of-concept ransomware campaigns autonomously orchestrated by AI. A 2025 NYU Tandon School of Engineering study showed that LLMs could execute complete attack chains autonomously. This included reconnaissance, exfiltration, encryption, and adaptation, and it was all done without human intervention. Adding data corruption to that process is a natural and dangerous progression.
Attacker-in-the-Middle will make phishing resistant MFA mandatory
How AiTM Attacks Work
The move to MFA for stronger authentication over the last decade has been a good one, but attackers have evolved alongside our defenses. Attackers use phishing kits, including the open source Evilginx to set up fake sign-in pages, mimicking Microsoft’s, Google’s or Okta’s pages and then trick users via phishing emails or Teams messages into clicking a link to it. Users sign in to the fake page, and their username, password, and MFA prompts are passed to the legitimate sign in page behind the scenes, while the attacker steals the resulting token, and can then access everything the user can, known as Attacker-in-the-Middle (AiTM).
Why Resistant MFA Matters
The ability to manage the MFA prompt is now a “standard feature” in these phishing kits. The only good defense is phishing resistant MFA technologies such as FIDO2 hardware keys, Windows Hello for Business, Certificate based Authentication (CBA) and Passkeys, as these are tied to the legitimate sign in page, and won’t work on the fake one, even if the user has been tricked. However, not only do you need to deploy phishing resistant MFA, you must also mandate it as the only sign in method, because most phishing kits now will also force a downgrade from a stronger MFA method to a less secure one.
Passkey adoption will be slowed by confusing user experiences
Cost And Adoption Pace
While hardware FIDO keys are a great option for phishing resistant MFA, it’s an added cost for every user to budget for. Passkeys, where the security chip in your modern smartphone is used instead, are an alternative, and we predicted that their adoption this year would accelerate, which it has, but not to the extent we expected.
Fragmented User Experience
The main reason for this is a fragmented user experience, it looks differently on an iPhone, an Android phone or a Windows / MacOS laptop. Furthermore, there are two flavors, with consumer ones being “syncable”, meaning they’re stored in your Apple or Google consumer account so you can use them on different devices. Storing corporate credentials in end users’ personal cloud accounts isn’t acceptable for most businesses, so they generally enforce non-syncable passkeys.
Device Lock-In Challenges
Those are locked to the smartphone where they were created, and in the case of Microsoft 365, the only app that’s accepted is Microsoft Authenticator. Add to this the confusing experience where you’re signing in to a service on your laptop and then have to scan a QR code with your phone and then complete the sign in flow on your phone.
Passkeys are the future of phishing resistant MFA, but the tech giants need to get together and harmonize the overall experience for both consumer and business users.
Identity verification and reset processes will continue to compromise organizations
Several of the very large breaches we’ve seen recently were due to (often outsourced) help desk staff being tricked into resetting accounts for administrative user accounts.
Remember, your authentication strength isn’t measured by which technology you use when everything is working normally, but by how hard it is to subvert your enrolment and recovery processes.
How do you validate that new hires are actually the people you expect (and not a North Korean infiltrator) in today’s remote working world?
What’s your process for recovering accounts for users who have lost their phone, FIDO key, forgotten their password and whose laptop just died?
Do you have a more secure process for high privilege accounts? (Including the requirement for an in-person validation at a company office).
Identity is the new firewall, but you must look holistically at mitigating risks in your entire identity workflow, starting from when the job offer is made to the last day of work.
SaaS apps are the new attack surface
Certain enterprise compromises over the last few years are interesting because they completely bypass the traditional “compromise a normal user – pivot in the internal network – compromise administrator accounts”.
As businesses become more and more reliant on SaaS services, new types of attacks that only compromise cloud data and identities are becoming more prevalent. Normal defenses such as EDR are mostly blind to these attacks, because while they’re taking place in the browser, there’s no malicious files or activity that endpoint protection can detect.
As a matter of fact, so much of modern business computing now happens in a browser, which is opaque to EDR, that using an enterprise browser and/or specialized software for protection in the browser is our strong recommendation. Mitre even has an ATT&CK MATRIX for different SaaS attacks.
Browser extensions will compromise more businesses in the coming year
Modern browsers are complex applications, almost like entire operating systems in themselves, and full of protection that keep us mostly safe from dangers on the internet, both in our personal life and at work. But most of us also use browser extensions, often for productivity or convenience, but sometimes these come with hidden risks. In some cases, they’re vulnerable in some way, degrading the protection of the browser itself; in other cases, they’re intentionally malicious.
This could be by having a similar name to a popular add-in, or by criminals buying a previous benign extension and then weaponizing it.
Make sure your business has a way of tracking extensions that are installed in your user’s browsers, easy ways of blocking ones that are found to be malicious (Intune or AD GPOs can do this) and educating your users about the risks.
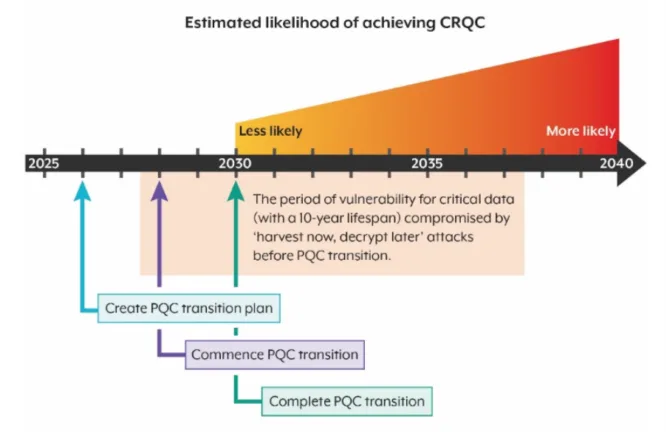
Predictions Regarding Quantum Computing
Understanding Q-Day
Most threats we look at in this article are current, while the advent of a Cryptographically Relevant Quantum Computer (CRQC) is still some years away. This day, known as Q-Day, is when these types of computers have sufficient scale (number of Qubits – the equivalent to bits in a classical computer), and low enough cost that they can use Shor’s algorithm to break asymmetric encryption such as RSA and Diffie-Hellman. Or Grover’s algorithm to halve the strength of symmetric cryptography (AES-128 becomes AES-64).
Industry Investment Trends
Many different tech companies, including the usual suspects (Google, IBM, Microsoft) are pouring millions into different flavors of quantum computers, seeing which technological approach is going to provide enough stable qubits.
The problem is noise, if you have lots of qubits, but use most of them for error correction; the overall number of logical qubits available to run your calculations are minimized. Quantum computers will not replace our current computers; instead, they’ll be used for very specific types of calculations, including breaking our current encryption algorithms.
Why Planning Must Start
While CRCQs are still 5 to 15 years away, you can’t wait until they arrive. Your organization should start planning now, if you store any Personally Identifiable Information (PII), Personal Health Information (PHI) and intend to (or you’re compelled to by regulation) to keep it for longer than five years, you need to start using quantum resistant algorithms for the encryption now.
Harvest Now, Decrypt Later
This is because several agencies around the world are using Harvest Now, Decrypt Later (HDNL) to store data that they can’t decrypt now but will be able to with CRCQs. Furthermore, it’s a huge project; you need to find every system, device, and part of your network that uses encryption, which algorithm is used, and what type of data is stored or transmitted. Sometimes it’ll be easy to add quantum resistant algorithms, in other cases you’ll need to replace the system entirely, or re-architect your processes.
Standardized Quantum Algorithms
NIST has standardized three quantum resistant algorithms:
- FIPS 203 defines a cryptographic scheme called Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM), which is derived from the CRYSTALS-KYBER submission.
- FIPS 204 is the Module-Lattice-Based Digital Signature Algorithm (ML-DSA), based on the CRYSTAL-Dilithium submission.
- FIPS 205 specifies the Stateless Hash-Based Digital Signature Algorithm (SLH-DSA), which is derived from the SPHINCS+ submission.
They rely on Transport Layer Security (TLS) version 1.3 so start by rolling that out everywhere you can in your environment.
Operating System Support
As for Operating Systems, preview versions of Windows 11 and Windows Server have updated versions of SymCrypt, the same library that’s used across Azure and Microsoft 365. ML-KEM and ML-DSA are already available in SymCrypt, both on Windows and Linux. SymCrypt-OpenSSL also offers the same support for OpenSSL. Apple is also including PQC in their CryptoKit for developers, and iMessage in iOS and TLS 1.3 in iOS26 are already incorporating PQC.
Building Crypto Agility: If you write your own applications in-house aim for crypto agility so that you can swap out cipher suites, or entire algorithms as updates are delivered.
Risks for Organizations in 2026
People, Process, And Technology
Cybersecurity isn’t a technology problem, it’s a people and process problem. As so often happens when you’re deep into the latest technology and seeing rapid developments in GenAI, or Machine Learning, or Agentic AI, the solutions you see are tech based (“when you only have a hammer, every problem looks like a nail”). But organizations rarely get breached based on technology failures alone; it’s more likely a combination of people, process and technology failures. The Swiss cheese model illustrates this clearly:
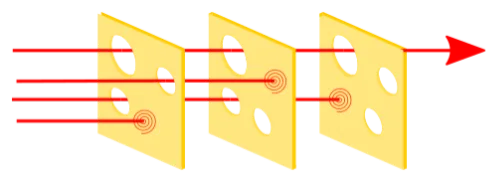
Building Cyber Resiliency: In other words, if you build cyber resiliency into your organization, through layers of protection and processes, you’ll be more likely to avoid a devastating breach.
Every Business Is A Target
No matter the size of your business, you will be a target of cybersecurity attacks in 2026. As you can see in our data, being a small organization / a not-for-profit / “not having anything worth attacking” isn’t a defense against criminals. If your business has sensitive data and cash reserves, you are a target. Build a cyber resiliency program based on the Zero Trust principles:
- Assume breach – obviously you build strong, layered protections, but they will eventually fail. At some point the holes will line up, and a breach will happen. Do you have detections in place to spot that quickly? Do you have isolated networks and only the required permissions assigned to minimize the blast radius? Do you have the people and the processes in place to react to the alerts and evict the attackers quickly before they can do major damage?
- Least privilege – this is possibly the hardest thing to get right, give people only the permissions they need to do their job, and regularly review them so they don’t accumulate over time.
- Verify each connection – have a strong policy engine in place (Conditional Access in Entra ID) that verifies each login and access to applications, files and other resource to ensure that access isn’t allowed by default, but rather only permitted when the right conditions are met.
Security Hygiene First
Before spending money on advanced security tools that solve specific problems, start by taking care of security hygiene basics based on the above principles:
- Implement MFA for everyone. Given the huge increase in Attacker-in-The-Middle (AiTM) kits having MFA bypass built in, you need to move to phishing resistant MFA. This includes hardware OAuth keys, Windows Hello for Business, Certificate based Authentication and Passkeys, which doesn’t allow authentication to fake login pages, even if the user themselves has been tricked.
- Have a strong endpoint protection solution on all devices where that’s possible, and integrate that with identity, cloud applications and an email hygiene solution for comprehensive eXtended Detection and Response (XDR).
- Train your users to spot phishing attempts, whether in email, Teams, Zoom or WhatsApp but more importantly – build a security culture. Assuming that IT or the security team is taking care of all cybersecurity so everyone else in the business don’t have to worry about it is like saying “only the workplace health and safety staff needs to worry about accidents”. No – everyone needs to speak up when they spot something dangerous, whether that’s balancing precariously on a rickety chair to replace a light bulb, or someone about to click on a link that they shouldn’t.
- Patch your software, but unless you want to double the size of your IT department, do it in a smart way. Apply Continuous Threat Exposure Management (CTEM) principles to protect your business-critical systems that have exploitable vulnerabilities first rather than trying to patch everything, everywhere, which is impossible.
- Look at your supply chain. Several large breaches in recent months have been due to outsourced helpdesk organizations being socially engineered (hacking people instead of computer systems). Understand all your outsourced processes, remembering that you can outsource a function, but not the risk associated with it. And investigate all the supply chains that make your business operate, and build in resilience for when they are disrupted, either through cybersecurity attacks or for other reasons.
Building A Cyber resilient organization
Because cybersecurity is a people and process problem, the solution isn’t more technology, it’s about changing the culture of your business.
Lessons From the Aviation Industry
We can learn a lot from the aviation industry, where every incident and accident is thoroughly investigated, not to assign blame, but to identify all the different people, process and technology factors that contributed to it. And then take those lessons and incorporate more / different training, changing processes and technologies to make sure it doesn’t happen again.
Fostering A Safety Culture
It starts with fostering a safety culture where everyone feels safe to speak up when they see something that’s not right. This only happens when people aren’t blamed individually when an incident happens – it’s about improving the processes so that people aren’t as likely to make those mistakes.
In turn, this means that cybersecurity is everyone’s responsibility, not just the IT or security department – because various parts of the business make technology decisions that bring risks that everyone, not just IT needs to manage. We in cybersecurity must also do better when it comes to communicating with other stakeholders, translating “geek speak” into business risk language.
Keeping Pace With Threats: As you build resiliency in every part of your business, keep up with the changes in the threat landscape as attackers are ever innovative in finding cracks in our systems to exploit.
A Holistic Security Strategy
We’ve mentioned it earlier but it bears repeating – start with the basics. Foundational cybersecurity hygiene processes and technology will serve your organization’s defenses much better than the latest cybersecurity point solution. You need multiple layers of protections (remember the Swiss cheese model):
- Next-Gen Spam/Malware detection with ATP for behavioral analysis to protect against the continued barrage of email-based threats we see in this industry.
- End-User Security Awareness Training to train end-users to spot social engineering attacks and spear-phishing attacks.
- Backup and recovery capabilities for BOTH on-premises data and data that lives in cloud services such as M365 for recovery purposes should a ransomware attack get through.
- Compliance and governance features that help protect against accidental data leakage and ensure that compliance controls are met.
- Least privilege and sharing control for your sensitive corporate data stored in SharePoint and OneDrive for Business.
- AI powered cyber assistant for Email and Teams protection, helping every user stay safe.
Your Partner in Cybersecurity
Cybersecurity is just one of the many challenges facing businesses today but not prioritizing it enough can lead to catastrophic outcomes (just ask Jaguar Land Rover).
Just as many businesses outsource parts of their operations to specialists in that area – take advantage of the deep knowledge and skills we at Hornetsecurity have developed since 2007. Partner with us to keep your business safe.
Stay Ahead of the evolving threat landscape with 365 Total Protection
AI-driven attacks, agentic automation, and identity compromise are becoming the new norm. Hornetsecurity’s 365 Total Protection gives your Microsoft 365 environment the layered defense it needs, from Advanced Threat Protection to AI Recipient Validation, compliance, data governance, and automated backup.

Protect your people, data, and cloud systems with a solution to address today’s and tomorrow’s threats. Request your personalized demo now.
Conclusion: The Earlier You Prepare, the Smaller the Impact
AI-driven attacks, agentic automation, and identity compromise are no longer edge cases — they are the daily reality of the threat landscape. Hornetsecurity’s 365 Total Protection gives your Microsoft 365 environment the layered defense it needs, combining Advanced Threat Protection, AI Recipient Validation, compliance and data governance controls, and automated backup to stay ahead of increasingly sophisticated threats
Protect your people, data, and cloud systems with a single solution designed to adapt with the changing cyber threat landscape, not chase it. Schedule a demo today and see how 365 Total Protection closes the gaps attackers rely on.
FAQ
Because AI tools are moving faster than governance and controls. Employees experiment, managers roll out new use cases, and security teams rarely see the full picture, creating blind spots where data leakage, prompt injection, or unintended model behavior can unfold long before anyone notices. In an evolving threat landscape, that governance gap is exactly what our cybersecurity predictions flag as one of the biggest systemic risks.
Very. Agentic AI can autonomously perform multi-step tasks: reconnaissance, exploitation, payload creation, evasion, and even post-attack adaptation. This lowers the barrier to entry for attackers and increases the volume and sophistication of attacks.
It’s no longer just about encryption. Ransomware 3.0 manipulates data integrity, altering or corrupting records to create long-term damage and erode trust. This is far more difficult, expensive, and time-consuming for organizations to recover from.
Because Attacker-in-the-Middle kits now bypass traditional MFA. Tools like Evilginx can steal tokens even if the password and MFA prompt are legitimate. Only FIDO2 keys, WHfB, CBA, or passkeys stop these attacks completely.
Start mapping where encryption is used, what data must remain secure beyond 5 years, and which systems will need PQC upgrades. Waiting until Q-Day is too late. Attackers are already harvesting encrypted data to decrypt later.
– Phishing-resistant MFA
– AI governance and visibility
– User security culture
– SaaS and browser security
– CTEM-based patching
– Zero Trust identity workflows
– Immutable backups for data integrity


