What is Data Loss Prevention (DLP)?
Data Loss Prevention (DLP) refers to the set of tools and solutions that protect against the loss, leak, misuse, or unauthorized access of sensitive data. It’s a critical aspect of complying with stringent regulations in today’s data-driven world. Failure to implement effective DLP measures can lead to severe consequences, including steep fines and regulatory violations. DLP is a framework that enforces remediation with protective measures that prevent users from accidentally or intentionally sharing data that places a business at risk. Data Loss Prevention is often categorized as a compliance concern for businesses since most compliance frameworks require organizations to proactively protect sensitive data. Maintaining strict adherence to compliance regulations is beneficial to customers, end-users, and businesses as it helps protect everyone involved. However, compliance can present challenges as organizations move into cloud Software-as-a-Service (SaaS) environments. Often, businesses have a solution that helps with DLP and other compliance concerns in on-premises environments. However, as they move to cloud SaaS and other cloud offerings, the traditional tools and solutions are no longer relevant to modern cloud architectures. As a result, organizations often must rethink their tooling and strategies for DLP as they migrate business-critical data to the cloud.Data leaks can be catastrophic
A significant driver for giving due attention to compliance and DLP initiatives is the destructive nature of data breaches. The sheer financial repercussions alone can be substantial. The IBM Cost of a Data Breach 2023 Report helps to emphasize the fiscal implications of a data breach event. Note the following findings for 2023 derived from the experiences of more than 550 global organizations:- $4.45 million – the average cost of data breaches in 2023, representing a 15% increase over a three-year period
- 51% of organizations plan on investing in cybersecurity – causes include data breaches – particularly in incident response, planning, testing, employee training, and advanced threat detection tools
- $1.76 million – the average a company saves by investing in cybersecurity and AI automation
- 1 in 3 breaches were detected by an organization’s security teams or tools
- $470,000 – the average cost of ransomware that didn’t involve law enforcement
- Since 2020, healthcare data breaches have increased by 53.3%
- 82% of all data breaches involved data stored in the cloud
In Cloud SaaS, DLP is Your Responsibility
Organizations may misunderstand the responsibilities of cloud service providers when they move their data to cloud SaaS environments like Microsoft 365. Many may assume protecting their data is now solely the cloud service provider’s responsibility. While hyperscale cloud service providers like Microsoft provide robust cloud architectures that do well to help protect your data from loss, the burden of responsibility for business-critical data rests with the cloud SaaS customer. Cloud service providers such as Microsoft operate on a “Shared Responsibility Model” that places responsibility for the data itself with the customer. In the “Shared Responsibility in the cloud,” note specifically the section of “Responsibility always retained by the customer.” Among the responsibilities that fall within the organization is the responsibility for information and data.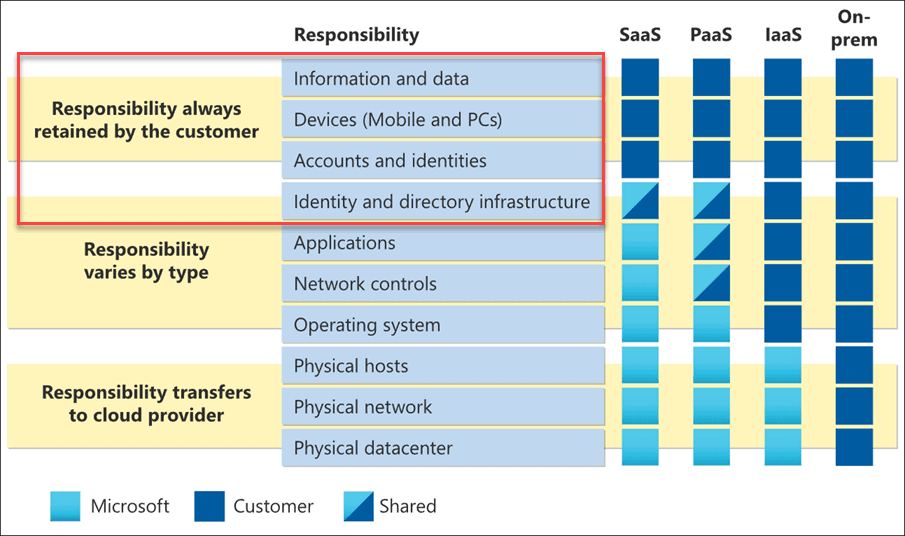 The shared responsibility model defined by Microsoft for cloud environments
The shared responsibility model defined by Microsoft for cloud environments
Cloud SaaS Backups are Essential
Often, Data Loss Prevention (DLP) focuses on the data leak aspect of losing data. However, DLP also indirectly relates to data protection. Most organizations today have a solid on-premises backup solution they use to protect mission-critical workloads running in on-premises enterprise data centers. However, as mentioned earlier, there is a notion that data backups are no longer needed once data is migrated to cloud SaaS environments. This idea can prove to be a grave mistake for organizations that suffer data loss from human error or a malicious attack at the hands of ransomware. The shared responsibility model used by hyperscale cloud service providers such as Microsoft places all aspects of protecting your information and data, including backups. Backing up ALL your data, including Office 365 workloads, is the cornerstone of any data protection strategy and business continuity plan.What is Microsoft 365 Data Loss Prevention (DLP)
Microsoft has not left organizations on their own regarding Data Loss Prevention (DLP) in the Microsoft 365 cloud SaaS environment. Microsoft has baked DLP into the Microsoft 365 SaaS environment using DLP policies. Microsoft 365 DLP is part of the Microsoft 365 Compliance tools that protect your sensitive data, no matter where it is stored and accessed. Microsoft 365 DLP policies allow businesses to monitor end-user activities and how users access sensitive data, whether at rest, in transit, or in use. You can log into the Microsoft 365 Compliance Center here: Microsoft 365 Compliance Center
Microsoft 365 Compliance Center
- Warn a user they may be trying to share a sensitive item inappropriately
- Block the sharing and, via a policy tip, allow the user to override the block and capture the user’s justification
- Block the sharing without the override option
- For data at rest, sensitive items can be locked and moved to a secure quarantine location
- With Teams chat, the sensitive information will not be displayed
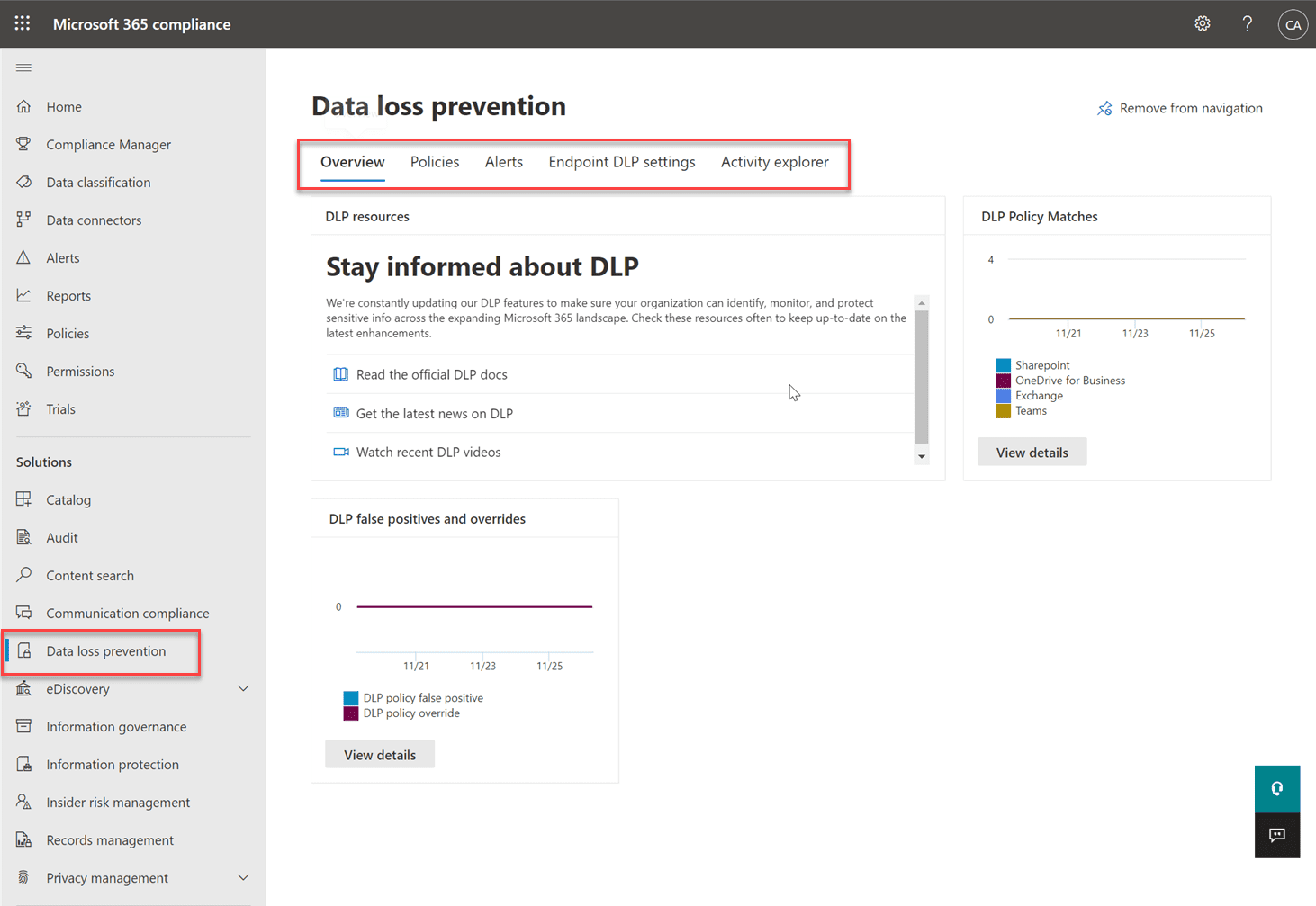 Navigating to Data Loss Prevention in Microsoft 365 Compliance Center
Navigating to Data Loss Prevention in Microsoft 365 Compliance Center
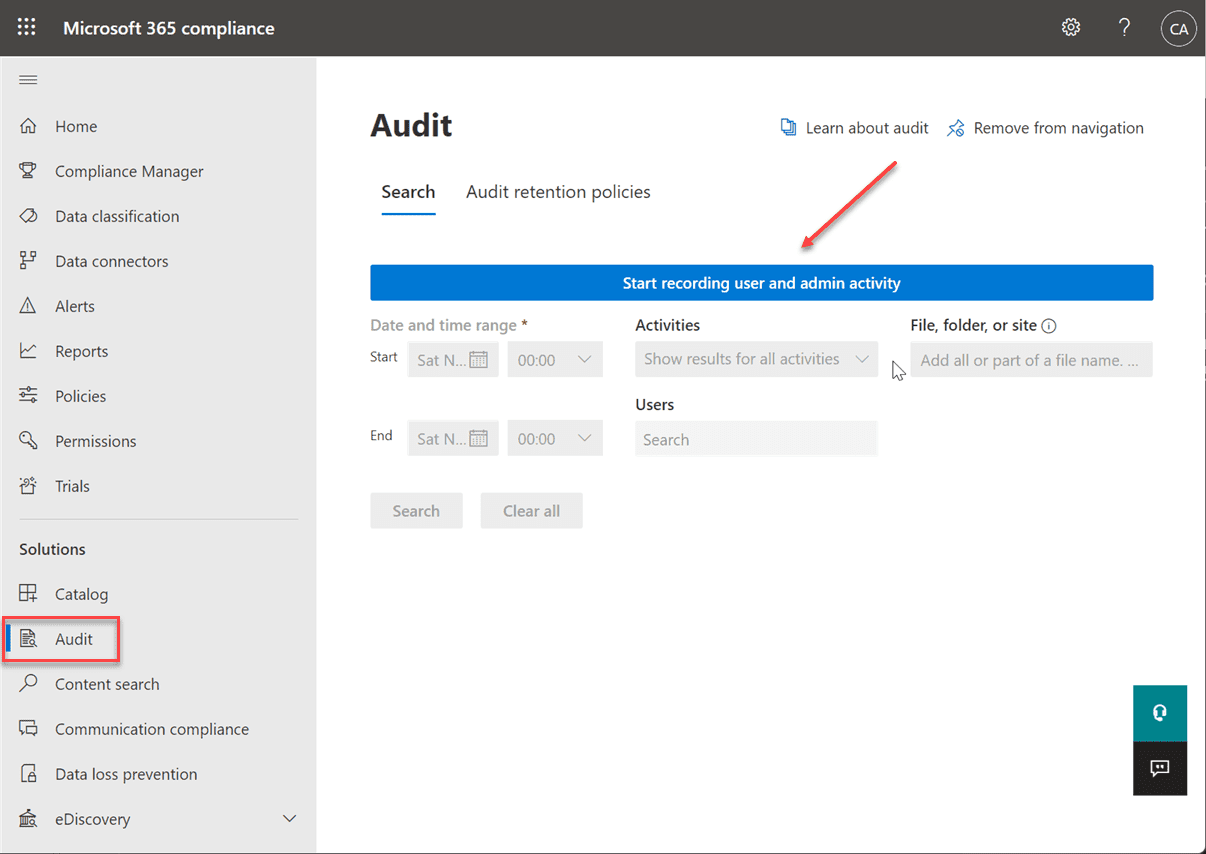 Configuring Microsoft 365 Auditing to record user and admin activity
Configuring Microsoft 365 Auditing to record user and admin activity
Microsoft 365 DLP vs. Microsoft Information Protection (MIP)
Many are confused with the various offerings from Microsoft related to compliance and data loss prevention. Microsoft Information Protection (MIP) helps discover, classify, and protect sensitive information. It is a suite of technologies rather than a single product. The capabilities of MIP include the Data Loss Prevention (DLP) capabilities found in Microsoft 365.- Sensitive information types (SITs)
- Trainable Classifiers
- Data Classification
- Sensitivity Labels
- Azure Information Protection (AIP) unified labeling client, now Microsoft Information Protection
- Azure Information Protection (AIP) unified labeling Scanner, now Microsoft Information Protection
- Azure Purview
- Double Key Encryption (DKE)
- Office 365 Message Encryption (OME)
- Service encryption with Customer Key
- SharePoint Information Rights Management (IRM)
- Rights Management connector
- Microsoft Cloud App Security (MCAS)
- Microsoft Information Protection (MIP) SDK
- Data Loss Prevention (DLP)
Data Loss Prevention (DLP) is Not a Substitute for Cybersecurity
It is essential to understand that while DLP is required to satisfy regulatory compliance demands and prevent data leak catastrophes, it is not an all-inclusive cybersecurity solution. While DLP should be part of your overall cybersecurity stance, it does not protect your environment from hackers. Data Loss Prevention helps organizations enforce governance restrictions with business-critical and sensitive data. However, it does not protect your environment from a ransomware attack, stolen credentials, phishing emails, malicious third-party applications, and other threats in the cloud. On the other hand, strong cybersecurity measures do not protect your organization from data leak events when users transmit or share data accidentally or intentionally. DLP helps organizations protect from insider threats, while other cybersecurity measures and technologies help protect them from outside threats posed by attackers and other malicious activities. Microsoft has other products that help organizations protect from malicious threats such as email compromise and credential phishing. Microsoft Defender for Office 365 provides deep inspection and can sandbox executables to understand if it is legitimate based on intent and behavior. Advanced artificial intelligence (AI) and machine learning (ML) in ATP help to protect your business-critical and sensitive data from attackers. Learn more about that solution here: 365 Total Protection from Hornetsecurity offers comprehensive protection for Microsoft cloud services – specially developed for Microsoft 365 and seamlessly integrated to provide comprehensive protection for Microsoft cloud services. Easy to set up and extremely intuitive to use, 365 Total Protection simplifies your IT Security management from the very start.Data Loss Prevention (DLP) is Not a Substitute for Backup
Although Data Loss Prevention sounds like backup, as you can see, it’s not the same thing. Your information governance plan for your business should include DLP, Information Protection, AND Backup. Office 365, Exchange Online, and SharePoint Online / OneDrive for Business uses various data protection technologies to ensure your data is highly available and protected against hardware failure. Still, there’s NO backup in a separate system and no way to “go back in time.” Make sure you complement DLP and Information Protection with solid third-party backup services for Office 365, such as Altaro’s Office 365 Backup.Microsoft 365 DLP Default Policy
In the Microsoft 365 Compliance Center, a default Data Loss Prevention (DLP) policy is listed, aptly named Default Office 365 DLP policy. The policy contains two safeguards by default, helping to protect organizations from data leaks involving credit card numbers. Let’s take a closer look at the default DLP policy, as it helps to get a feel for the configurable policy settings.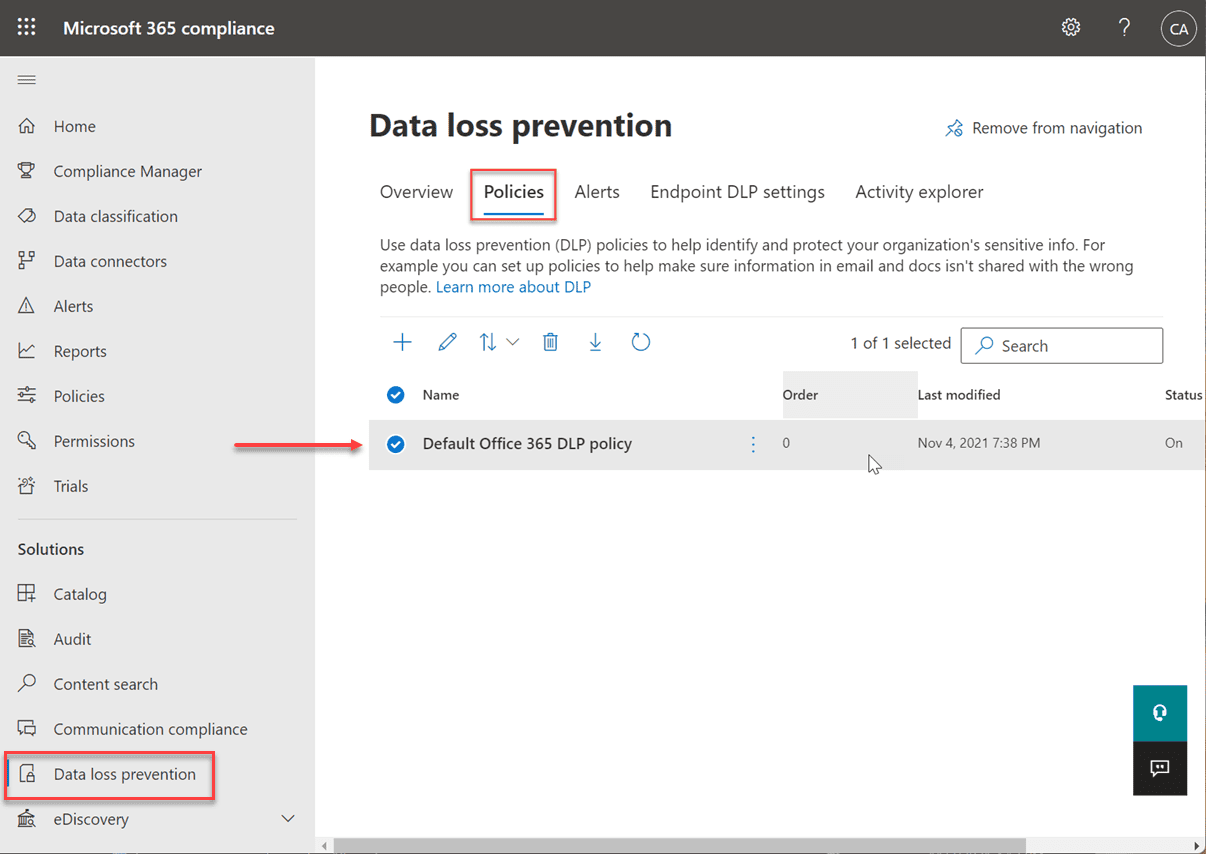 Viewing and editing the default Data Loss Prevention (DLP) policy in Microsoft Compliance Center
Viewing and editing the default Data Loss Prevention (DLP) policy in Microsoft Compliance Center
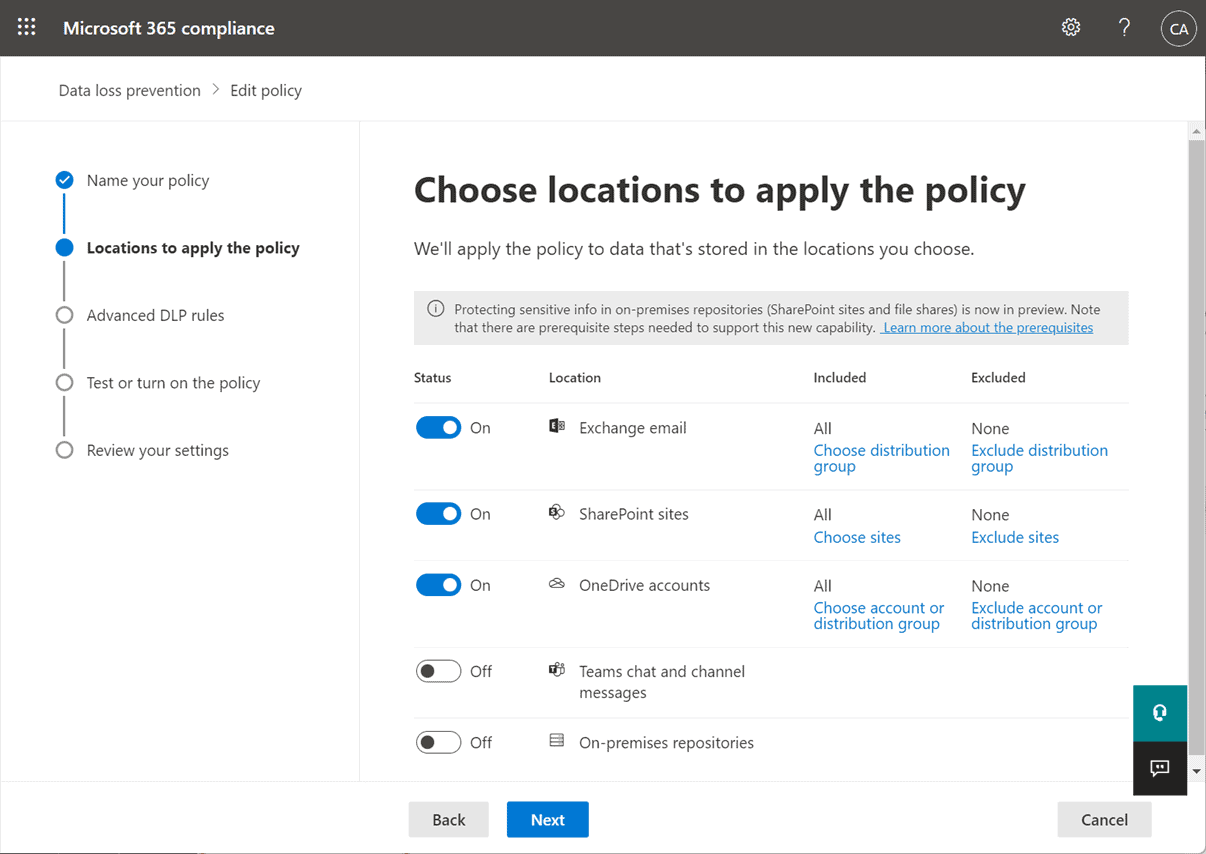 Services assigned to the default Microsoft 365 DLP policy
Services assigned to the default Microsoft 365 DLP policy
- Items containing 1-9 credit card numbers shared externally
- Items with 10 or more credit card numbers shared externally
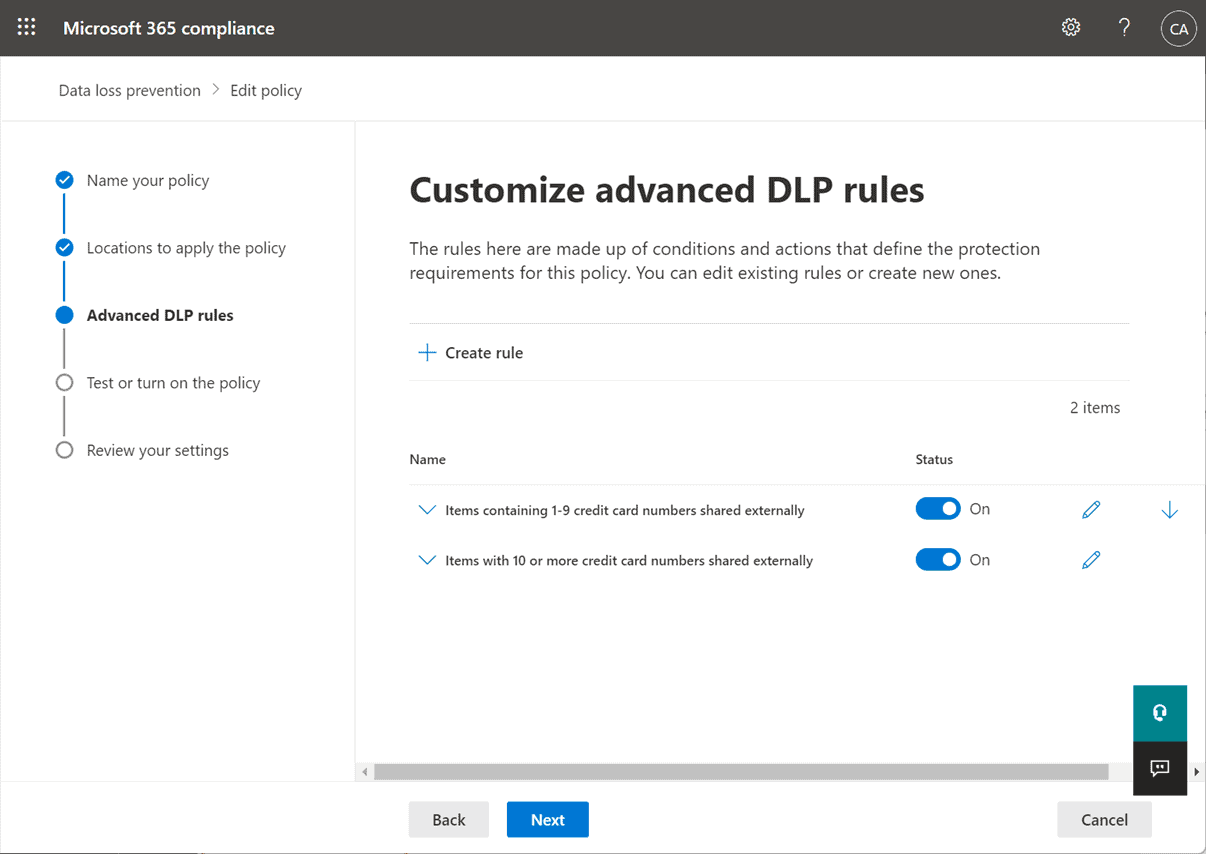 Default advanced rules contained in the Microsoft 365 DLP policy
Default advanced rules contained in the Microsoft 365 DLP policy
 Sensitive info types configured for Credit Card Number
Sensitive info types configured for Credit Card Number
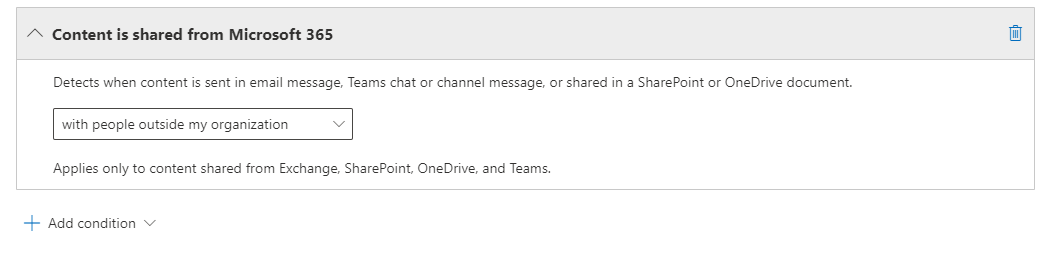 Data shared outside the organization
Data shared outside the organization
- The person who sent, shared, or modified the content
- Owner of the SharePoint site or OneDrive account
- Owner of the SharePoint or OneDrive content
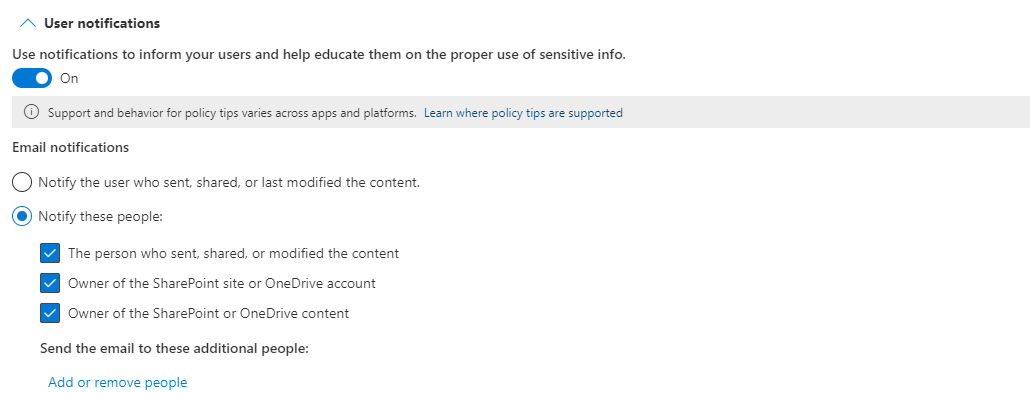 Notification rules for the Microsoft DLP policy
Notification rules for the Microsoft DLP policy
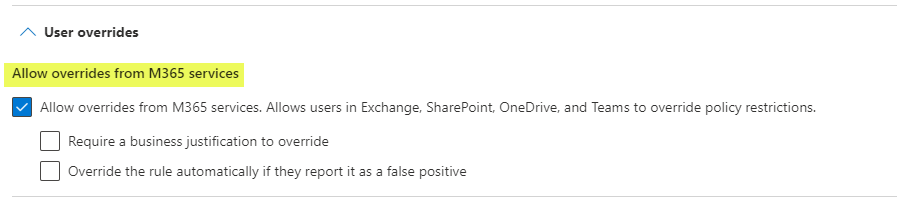 Allowing user overrides from M365 services
Allowing user overrides from M365 services
Built-in Templates
One of the really nice features Microsoft has built into the Microsoft 365 DLP policy configuration wizard is templates. Depending on the type of compliance, industry, and other factors, the templates make it much easier to start with a good baseline of DLP policy settings.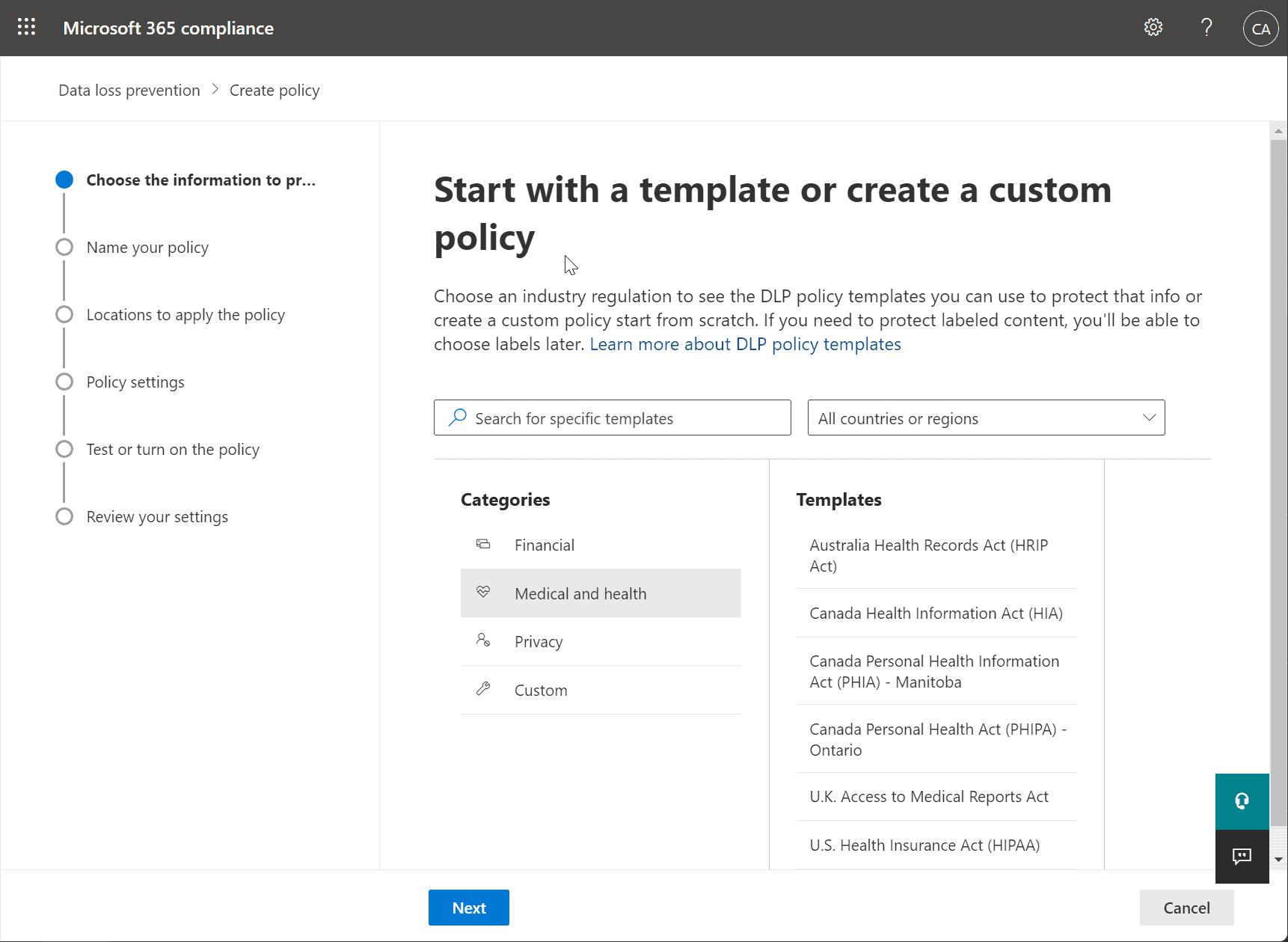 Using Microsoft 365 DLP templates
Using Microsoft 365 DLP templates
Microsoft 365 Endpoint DLP
With Microsoft 365 DLP, organizations must monitor the actions taken on sensitive data and help prevent the unintentional sharing of those items. However, there is another aspect – the endpoint. Microsoft 365 Endpoint data loss prevention (Endpoint DLP) provides the capabilities to extend the activity monitoring and protection capabilities to sensitive items physically stored on the endpoint. These may include Windows 10, 11, and macOS (currently in public preview) devices. To access and use Endpoint DLP functionality, you must have one of these subscriptions or add-ons.- Microsoft 365 E5
- Microsoft 365 A5 (EDU)
- Microsoft 365 E5 compliance
- Microsoft 365 A5 compliance
- Microsoft 365 E5 information protection and governance
- Microsoft 365 A5 information protection and governance
- Upload to cloud service or access by unallowed browsers
- Copy to other apps
- Copy to USB or other removable media
- Copy to a network share
- Printing a document
- Copy to a remote session
- Copy to a Bluetooth device
- Create an item
- Rename an item
- Word files
- PowerPoint files
- Excel files
- PDF files
- .csv files
- .tsv files
- .txt files
- .rtf files
- .c files
- .class files
- .cpp files
- .cs files
- .h files
- .java files
Configuring Microsoft 365 Endpoint DLP settings
To configure Microsoft 365 Endpoint DLP settings, navigate to Data Loss Prevention (DLP) > Endpoint DLP settings. As you can see below, you can configure policy settings controlling:- File path exclusions
- Unallowed apps
- Unallowed Bluetooth apps
- Browser and domain restrictions to sensitive data
- Additional settings for endpoint DLP
- Always audit file activity for devices
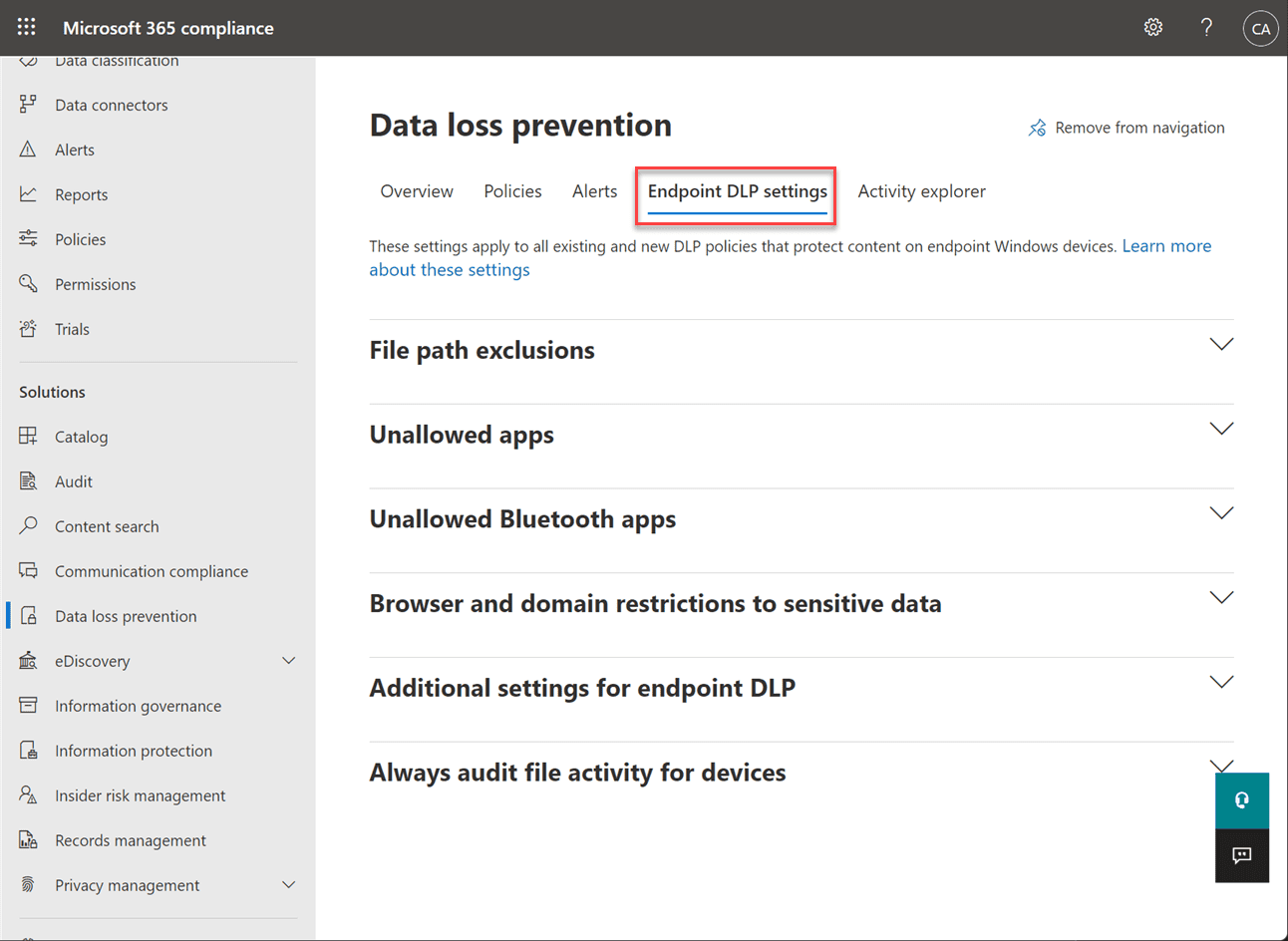 Configuring Endpoint DLP settings
Configuring Endpoint DLP settings
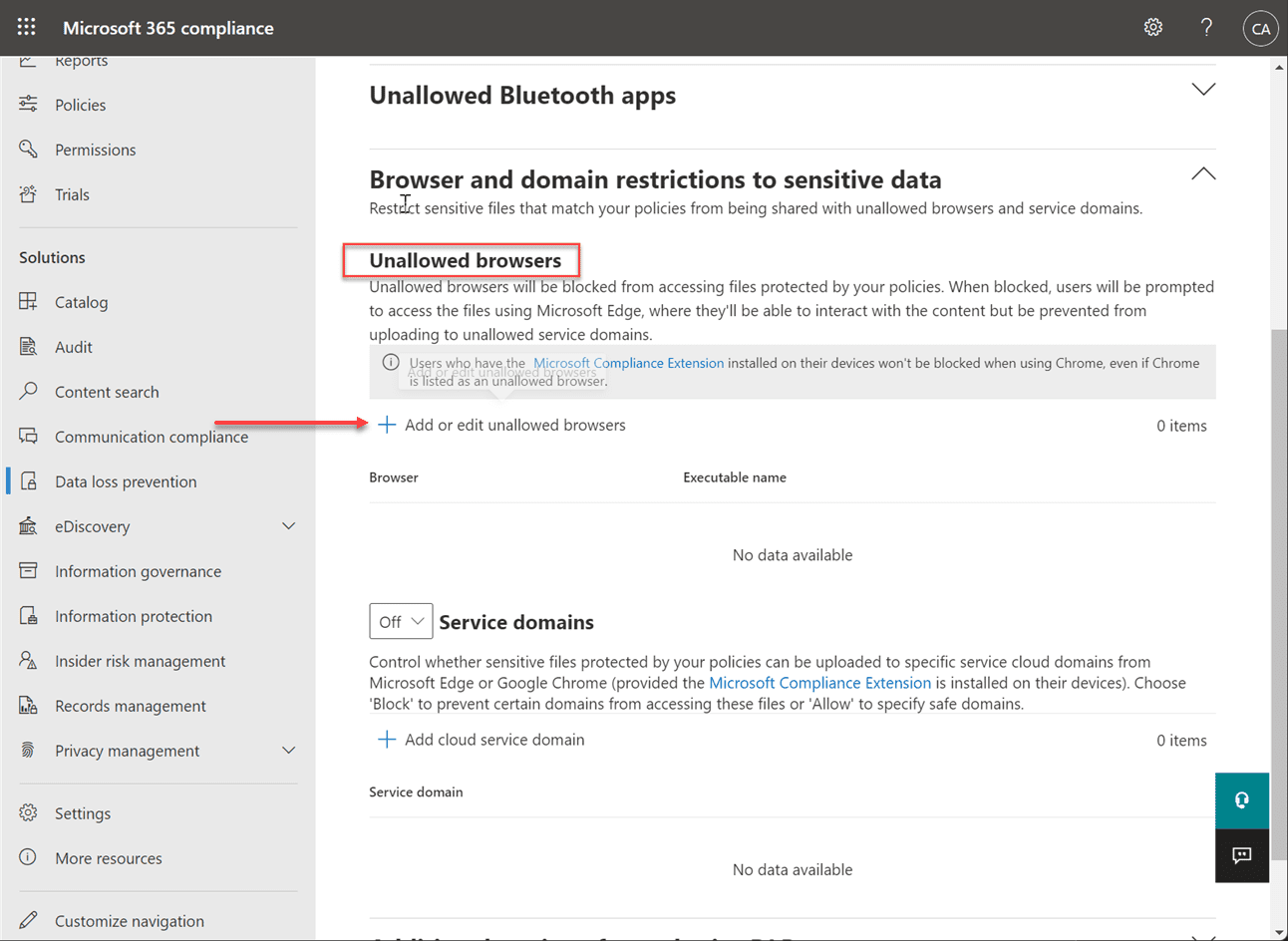 Adding Unallowed Browsers in a Microsoft 365 Endpoint DLP policy
Adding Unallowed Browsers in a Microsoft 365 Endpoint DLP policy
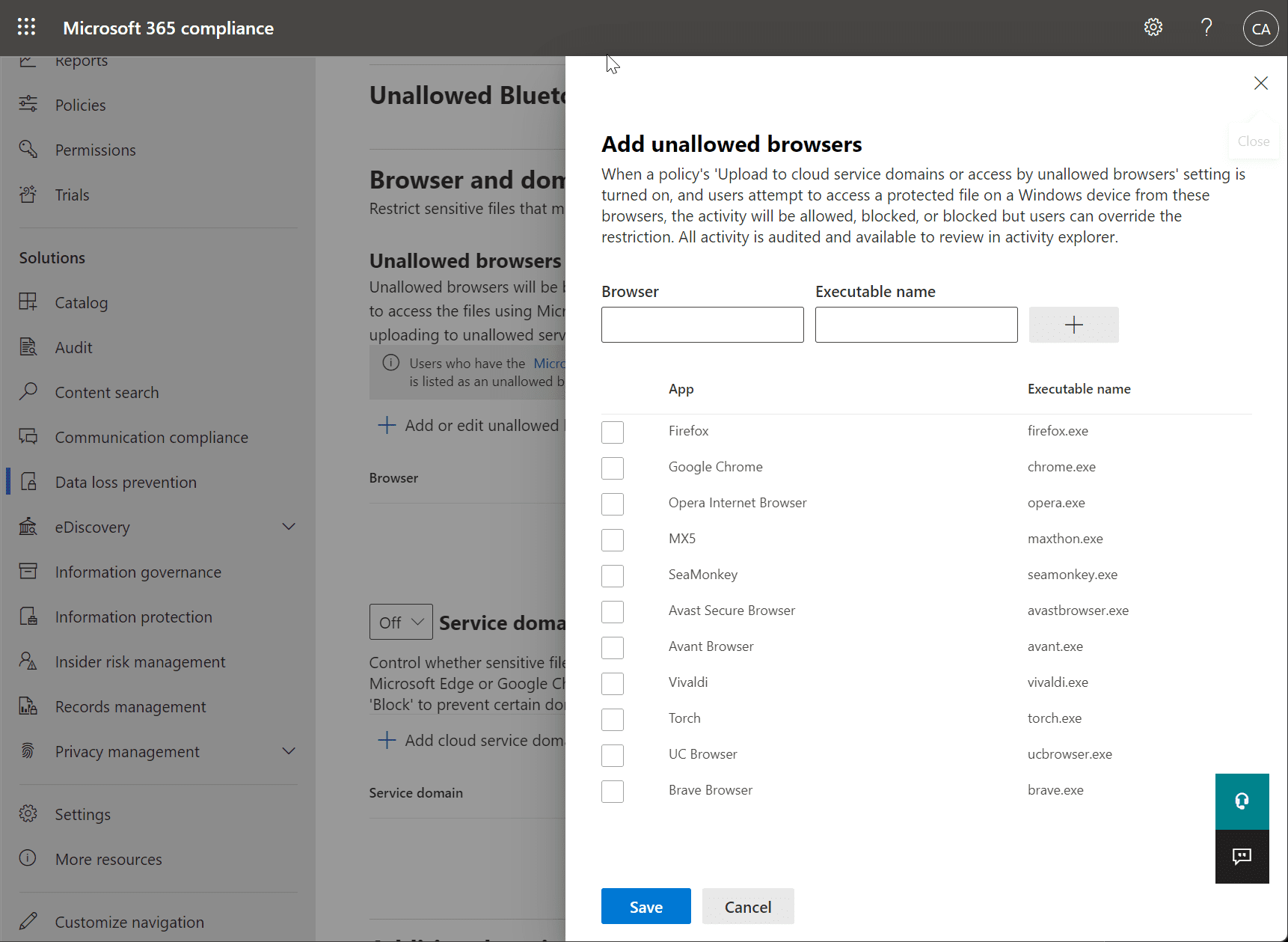 Choosing unallowed browsers for your Endpoint DLP policy
Choosing unallowed browsers for your Endpoint DLP policy
Onboarding devices into Microsoft 365 Endpoint DLP
You must enable device monitoring and onboard your endpoints before you can monitor and protect sensitive items on a device. You can enable device management and onboard devices using the Microsoft 365 Compliance portal. Onboarding is accomplished by downloading and running the script on the endpoint. You can also onboard devices using Group Policy, Microsoft Endpoint Configuration Manager, Mobile Device Management tools, and onboarding virtual desktop infrastructure (VDI) devices.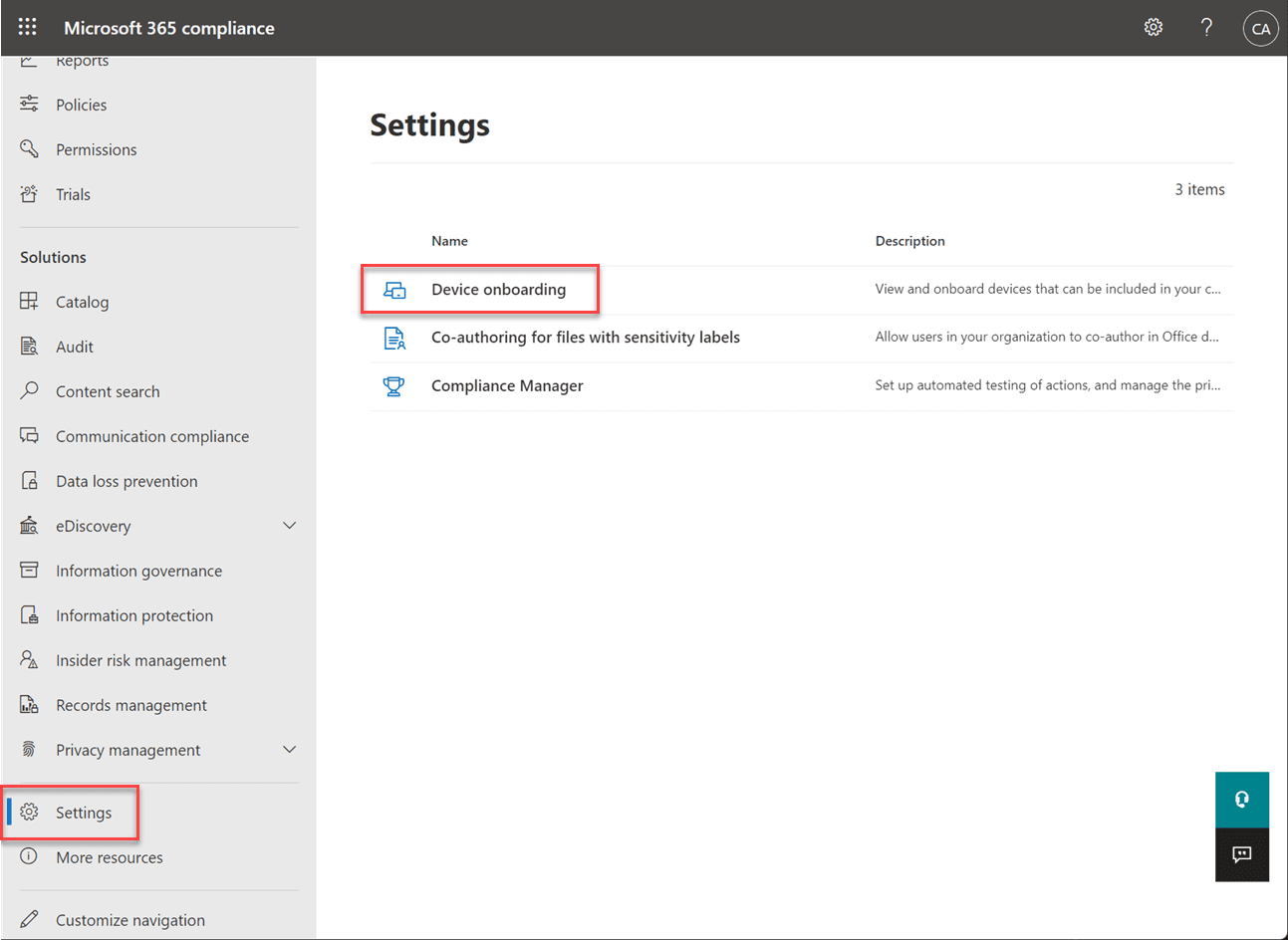 Onboarding devices into Microsoft 365 Endpoint DLP
Onboarding devices into Microsoft 365 Endpoint DLP


