

Why the Pharmaceutical Industry Is a Prime Target for Cyber Attacks
The reality of cyber threats to the pharmaceutical industry is undeniable. The combination of high value intellectual property (IP), a fiercely competitive industry globally with many countries happy to steal that IP rather than develop it themselves, and (in many cases), legacy, vulnerable technology stacks, both in IT and OT/ICS systems.
In this article we’ll look at various cyber threats to the pharmaceutical industry, cover some publicly known breaches and their consequences, and offer a great solution to many of these challenges.
Why is the pharmaceutical industry a prime target?
The pharmaceutical industry is generally regarded as high stakes risk and reward. Research and development of new drugs can take years and a lot of money, they must go through extensive testing before humans can take advantage of them and thus a breach at just the wrong time in that cycle can be catastrophic.
The successful launch of a much-needed new drug on the other hand can bring large fortunes for years to come. The classic example here is Ozempic and Wegovy from Novo Nordisk in Denmark which has a large market share in the US.
Top 5 Healthcare data Breaches since 2022
Below, you’ll find a table listing the largest confirmed healthcare data breaches in the US since 2022, highlighting the number of individuals affected. Keep in mind, these totals could change as investigations progress and additional compromised data becomes apparent.
| Rank | Year | HIPAA-Regulated Entity | State | Entity Type | Individuals Affected | Type of Breach |
|---|---|---|---|---|---|---|
| 1 | 2025 | Aflac Incorporated (“Aflac”) | GA | Health Plan | 78,800,000 | Hacking/IT Incident |
| 2 | 2024 | Change Healthcare, Inc. | MN | Business Associate | 192,700,000 | Hacking/IT Incident |
| 3 | 2024 | Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 | Unauthorized Access/Disclosure |
| 4 | 2023 | Welltok, Inc. | CO | Business Associate | 14,782,887 | Hacking/IT Incident |
| 5 | 2023 | HCA Healthcare | TN | Business Associate | 11,270,000 | Hacking/IT Incident |
Key Cyber Threats to the Pharmaceutical Industry
Sensitive Health Data Exposure & IP Theft
Unlike an online retailer for example, that keeps financial information and shipping data on their customers where a breach is bad already, many pharmaceutical companies keep the most sensitive health data on their customers / trial participants.
This is reflected in the number of regulatory compliance frameworks in various geographies that they must comply with, adding further overheard.
Thus, the pharmaceutical industry is often cited as the number-one target for global IP theft.
Rising Supply Chain Attacks
Another area of cyber threats to the pharmaceutical industry that has been rising for all organizations globally over the last few years is supply chain attacks.
One of the most prominent attacks in recent memory was the attack on NHS in the UK in June 2024 where seven London hospitals were shut down, leading to the postponement of over 6000 hospital appointments and procedures.
But while these NHS hospitals were the ultimate victim, the ransomware attack actually hit Synnovis, a supplier of pathology testing and diagnostics.
Your suppliers are at risk too
In other words, if you are protecting a pharmaceutical company, you don’t just need to get your own house in order and protected, you must make sure your suppliers (and their suppliers) are taking cybersecurity seriously as well, plus make contingency plans to manage the fallout when a supplier is compromised.
Human Error and Cloud Misconfiguration
The uncomfortable truth that we’ve seen play out over the last decade as ransomware and data theft has become an accepted part of the risk landscape for all organizations is that cybersecurity is not a technology problem, it’s a human problem.
The vectors are different than a conman selling the Eiffel tower twice but the psychological mechanisms behind social engineering and successful phishing scams are the same as they’ve always have been.
Cloud Complexity
Modern, cloud-based IT systems are complex and everchanging as cloud providers push to add new features (including AI) at breakneck speed, making insecure configuration mistakes easy.
Academic Ties
The pharmaceutical industry faces another cyber threat due to its ties to the academic world, where universities often conduct clinical trials. This environment fosters an open exchange of information but has a history of inadequate cybersecurity preparedness.
The solution? Training & Cultural Change
Given this context, it’s essential to implement short, regular cybersecurity awareness training. This training must be paired with a significant cultural shift within the organization to enhance overall security.
It’s not that ordinary users don’t care about cybersecurity and protecting sensitive data, it’s just not a high enough priority unless leaders demonstrate that it is important through leading by example and fostering a strong cybersecurity culture.
Legacy Systems and the IoT Entry Point
The fact that 73% of healthcare providers depend on outdated systems is scary. The reality is that the move to cloud-based systems is a multi-decade project for many large pharmaceutical companies and just moving VMs to the cloud for example doesn’t make you more secure. For both cloud and on-premises systems, basic cybersecurity hygiene still matters.
Why Cybersecurity Hygiene is essential
Timely patching of systems housing sensitive data, only using supported OS versions and ensuring that EDR is deployed on every endpoint where you can are table stakes at this point.
Furthermore, make sure that you have monitoring in place, you can’t protect against what you can’t see, so a modern Security Information and Event Management (SIEM) system needs to be in place so that you can take action when the inevitable intrusion happen, before it turns into a full-blown breach.
IoT And Non-IT Vulnerabilities
Don’t forget your non-IT systems. Many pharmaceutical companies rely on complex IoT / OT systems, and while they’re often decoupled from the IT systems, they’re still vulnerable to attacks.
A comprehensive inventory of these should include everything from smart doors, conference room equipment, printers, IP telephony systems, surveillance equipment to factory and industrial equipment control systems.
Intellectual Property Theft & Supply Chain Risks
We’ve already mentioned supply chain risks, a notable example is the 2024 breach of Cencora (a large U.S. pharmaceutical distributor): a cyberattack on Cencora led to 11 major drug companies – including Bayer, Novartis, GlaxoSmithKline, AbbVie and others – to announce that their patients’ personal data was exposed through this single incident.
The Unique Nature of IP Theft
The problem with Intellectual Property (IP) is that it doesn’t weigh anything, and once copied, you can never get it back.
Many types of theft that organizations guard against are for physical items – computers, documents and trucks but digital information is different, and in a sophisticated attack, the first time you realize that you’ve been robbed might be when a competing pharmaceutical company releases an identical drug to yours a month before you.
Protecting IP Throughout Its Lifecycle
You need clear processes for handling IP information throughout its lifecycle, and deep monitoring to understand the flow of data between all parties, including insiders, as they can be bribed or threatened.
While many IP thefts aren’t disclosed publicly for obvious reasons we know that back in the early days of Covid both Russian and North Korean attackers tried (and maybe succeeded) to steal the research as the first versions of Covid vaccines were tested.
Business Continuity: Rethinking Backup And Recovery
One important part of cyber resiliency in an organization is the approach to data storage, backup and recovery. Traditional backup and even disaster recovery (DR) systems were designed to minimize IT outages.
That approach and mindset is completely inadequate for cybersecurity attacks, which the devastating attack on Change Healthcare in 2024 demonstrated.
Lessons From Change Healthcare
Leading to an overall cost of $ 1.6 billion USD, the attack was facilitated by stolen credentials, lack of MFA enforcement for a system, lack of monitoring (the attackers had access for nine days, moving around the network at will) – but most damming was that the disaster recovery system located offsite was connected to the main system.
So, when the attackers sprang the attack, both sites were encrypted by ransomware, leading to months of impact for ordinary people.
Modernizing Disaster Recovery
Modern DR must take into account both the risks of “normal” IT systems outages, and ransomware and other cyber-attacks. Don’t use backup tapes that can be stolen unless you’ve encrypted that data with strong key management.
Better yet, use immutable cloud storage, where even a ransomware attack can’t alter or encrypt the backup data. Don’t forget your Microsoft 365 data – many times it contains a lot of IP and other sensitive data which must be safely backed up, to protect against accidental data deletion, as well as ransomware attacks.
Regulatory Compliance: Growing regulations
Many governments around the world are implementing stricter health data regulations / laws every year, and as an added “bonus”, they’re different across distinct geographies, adding to the workload for global companies. The main ones to be concerned about for pharmaceutical companies are HIPAA in the US, and GDPR and NIS2 in the EU.
Use the work of ensuring compliance with regulations to look closely at data integrity. Regulations are very concerned with protecting patient and clinical test data – aim to not only “tick the box” for the auditor but actually ensure that sensitive data you hold and process is truly protected.
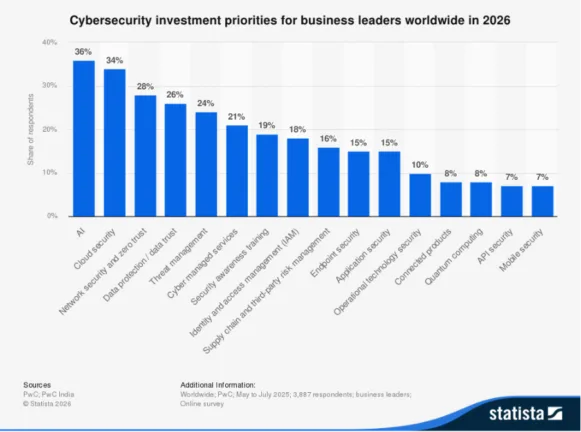
Investment Priorities for 2026
Across all industries, business leaders worldwide will prioritize investments in 2026, with AI and cloud security taking the lead. Our recommendations align with the anticipated risks others foresee.
Modern Protection for Modern Medicine: 365 Total Protection Plan 4
Hornetsecurity’s 365 Total Protection Plan 4 modernizes your security and business continuity because it offers a secure, compliant and governed Microsoft 365 tenant. It has it all in one package, industry leading email security, backup, security awareness training, access and permission control for SharePoint, plus domain fraud protection. You’ll also benefit from our AI Cyber Assistant-powered trio for even stronger security and greater awareness: AI Recipient Validation, Teams Protection, and AI Email Security Analyst.
Secure Your M365 Environment with 365 Total Protection Plan 4
Keep your organization safe and compliant while taking charge of your Microsoft 365 environment. With Hornetsecurity’s 365 Total Protection Plan 4, you actively safeguard your peace of mind while enjoying comprehensive coverage. Here’s what you’ll get:
- Comprehensive email security and backup solutions.
- Proactive security awareness training to mitigate human error.
- Robust access and permission control to protect sensitive information.
- Domain fraud protection to safeguard against online threats.

Leverage our AI Cyber Assistant-powered trio for unparalleled security and heightened awareness: AI Recipient Validation, Teams Protection, and AI Email Security Analyst.
Enhance your pharmaceutical organization’s security today. Interested in improving compliance? Let’s schedule a personalized demo tailored just for you!
Conclusion
As we’ve shown, cyber threats to the pharmaceutical industry are real, sometimes leading to attacks with devastating impact, both financially, reputationally and even affecting healthcare.
Technology by itself won’t “fix” the issue, but combining an outstanding suite of industry leading tools in 365 Total Protection Plan 4 with people and process is a good strategy for cloud security.
FAQ
The pharmaceutical industry is particularly vulnerable to cyber attacks due to its high-value intellectual property (IP), competitive global landscape, and the sensitive health data it manages.
Pharmaceutical companies face various cyber threats, including supply chain attacks, human error, cloud misconfiguration, and the vulnerabilities associated with legacy systems. Notably, the industry is increasingly at risk of ransomware attacks and intellectual property theft, where competitors may replicate valuable research and drug developments.
A prominent example is the ransomware attack on Synnovis, a supplier to NHS hospitals in the UK, which shut down seven hospitals and postponed over 6,000 appointments. This attack underscores the importance of securing not just the pharmaceutical company itself but also its suppliers and their systems.
To protect sensitive data, pharmaceutical companies should invest in robust cybersecurity practices, including timely system patching, deploying endpoint detection and response (EDR), and implementing a modern Security Information and Event Management (SIEM) system. Regular cybersecurity awareness training for employees and maintaining secure configurations for cloud and on-premises systems are also vital.
Pharmaceutical companies must navigate a complex landscape of regulatory compliance, including HIPAA in the US and GDPR in the EU. These regulations mandate the protection of sensitive patient and clinical trial data, adding to the operational workload and necessitating a commitment to data integrity.
Hornetsecurity’s 365 Total Protection Plan 4 offers a comprehensive suite of security solutions tailored for the pharmaceutical industry. It includes robust email security, backup systems, proactive security awareness training, and features such as access control and domain fraud protection. The package aims to modernize security measures and enhance compliance, ultimately providing organizations with peace of mind.


