

Phishing, Affiliate Marketing, and Investment Fraud: Analysis of a Large-Scale Lead Generation Campaign
Affiliate marketing and customer acquisition programs are based on a simple principle: paying third parties to generate traffic or qualified leads. While these models are widely used in legitimate contexts, they can also lead to abuses when performance is measured solely by the volume of leads generated.
In such environments, some intermediaries may be incentivized to favor aggressive or deceptive practices in order to increase their revenue. This can include the use of ambiguous marketing messages, impersonation of well-known brands, or the launch of campaigns distributed without the clear consent of recipients.
In addition, the large number of parties involved — affiliates, lead management platforms, resellers — makes it harder to trace the collected data and blurs accountability. This fragmentation can facilitate the reuse of personal data in contexts different from those originally presented to the user, particularly in connection with investment offers or services relying on high-pressure sales tactics.
These dynamics create favorable conditions for the emergence of deceptive campaigns at the boundary between aggressive marketing and fraud, making them sometimes difficult to detect and classify.
At the end of February 2026, a large-scale phishing campaign targeting French internet users was identified. The operation promotes an investment opportunity presented as being linked to Amazon, based on deceptive elements and not corresponding to any known official offer. The objective of this campaign appears to go beyond the simple collection of personal information. The observed elements suggest that it may be part of a lead generation mechanism tied to deceptive investment offers.
An industrial-scale campaign
The messages use hooks related to cryptocurrency and Amazon to attract the attention of victims and create a sense of urgency.
Among the observed subject lines:
- “Top Rank ⓟCrypto – Il reste peu de temps pour vous inscrire !”
- “Amazon is turning to crypto – a crypto revolution is underway!”
The collected data makes it possible to estimate the scale of the operation: more than 1.2 million emails observed in total in less than 3 weeks (18 days exactly).

The campaign operators implement several techniques designed to maintain distribution despite email security protections.
The observed tactics include:
- Rotation of domains used in phishing links.
- Rotation of senders in order to bypass reputation mechanisms.
- Randomization of display names and subject lines through the addition of random text elements.
- Blocking of certain IPs, for example those used by a VPN.
The infrastructure used also relies on Cloud resources and on a set of domains registered specifically for the campaign.
In addition to the points mentioned above, several elements support classifying this campaign as deceptive:
- Brand impersonation (Amazon / BFM) without any official link;
- Unrealistic promises of returns;
- Collection of personal data without transparency regarding its use;
- Absence of legal mechanisms (legal notice, explicit consent, unsubscribe option);
- Redirection to platforms known to feed fraudulent investment schemes;
- A high complaint rate (>5%).
A fake “Amazon Crypto” investment opportunity
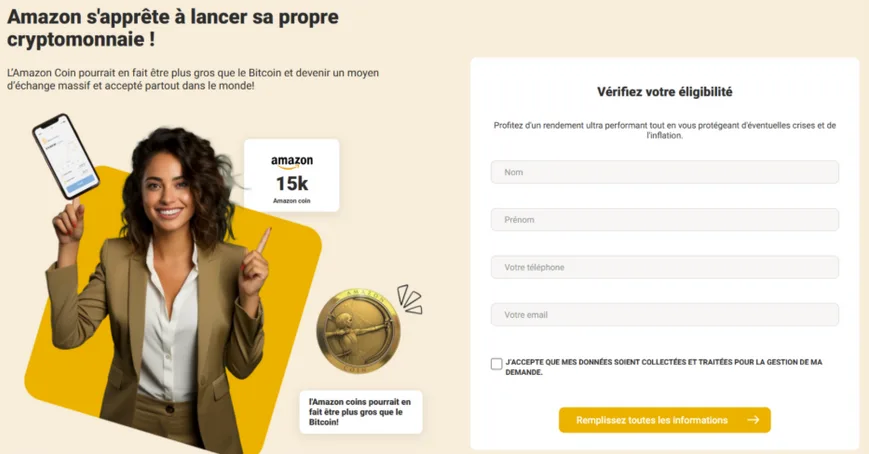
Users who click the link in the email are redirected to a landing page presenting an investment opportunity supposedly linked to Amazon and to a new cryptocurrency.
The website highlights:
- High profitability
- Upcoming mass adoption
- A time-limited opportunity
Amazon has never launched a public cryptocurrency. Amazon Coin did exist, but:
- It was an internal virtual currency (not blockchain-based)
- It was used only to buy apps and content on the Amazon Appstore
- And it was discontinued in 2025
A form asks victims to provide several personal details:
- Last name
- First name
- Email address
- Phone number
After submitting the form, the victim is redirected to a confirmation page stating that an advisor will make contact as soon as possible.

Lead generation for financial scams
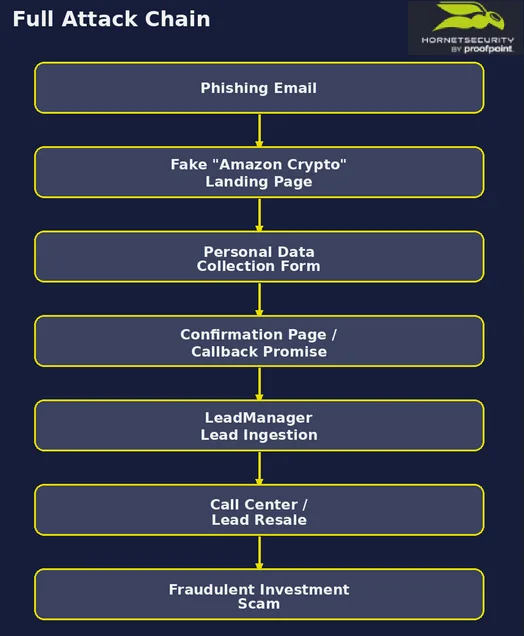
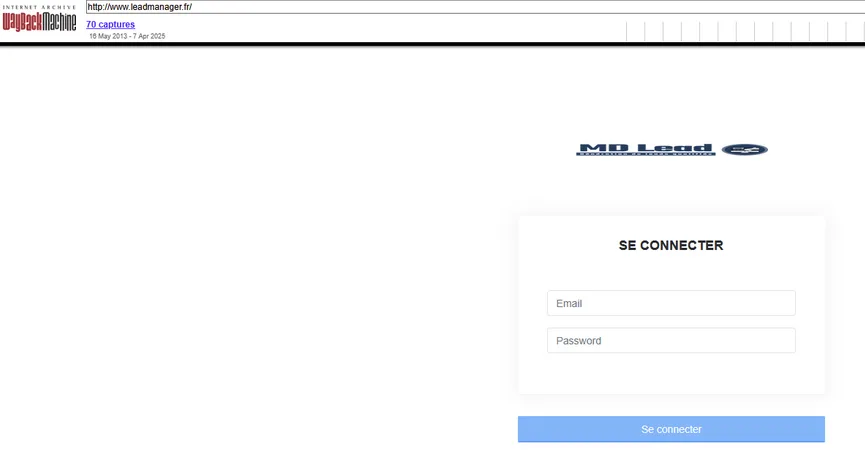
Traffic analysis shows that the collected information is routed through a platform called LeadManager, used to structure the collected data as sales leads.
The operation follows a clearly defined pipeline:
Traffic source → Landing page → Form → LeadManager → Call center / Lead resale
The collected data can then be:
- Resold to third parties specializing in fraud.
- Used directly by call centers tasked with contacting victims.
These operators then attempt to convince victims to invest in fake trading or cryptocurrency platforms.
How the Call Center Follow-Up Supports the Scam
We took part in the exercise by filling out the contact form.
It took less than 24 hours for us to be contacted by Gabriel Tissier, 0162142189, supposedly a wealth manager for Gemini Bank. He was not operating alone, as other people could be heard in the background.
He offered us a savings product managed by a robo-advisor across more than 500 cryptocurrencies.
The announced returns showed significant inconsistencies. At first, we were told of a guaranteed 7.2% net annual return, then later a different claim of gains between 1% and 2% net per day.
The caller illustrated these performances with an example according to which an investment of €40,000 would have quadrupled in two years. However, these various statements are mutually incompatible and are not based on credible financial assumptions.
He also collected some information, including the potential amount to invest, our bank and current investments, the type of bank card we use, and our age.
The minimum amount to invest is €150. This low threshold is intended to reassure the target, and the deposit is made through PayPal (we also observed the use of the platform evirtualpay.com).
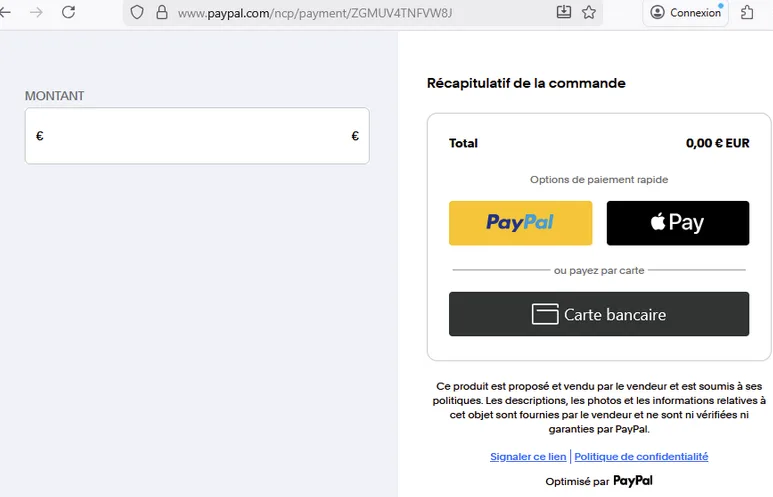
We received an email containing a link to make the first deposit.
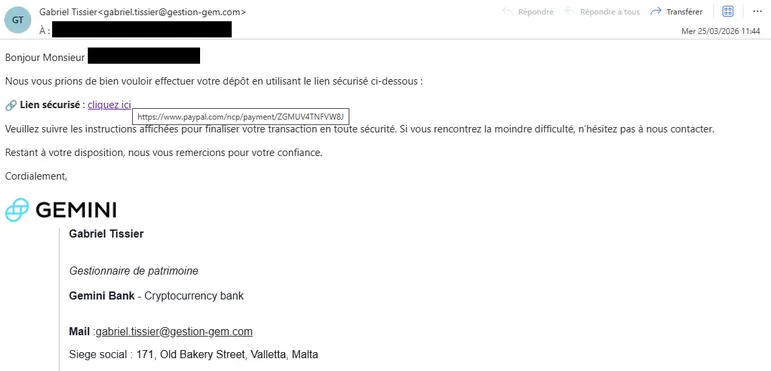
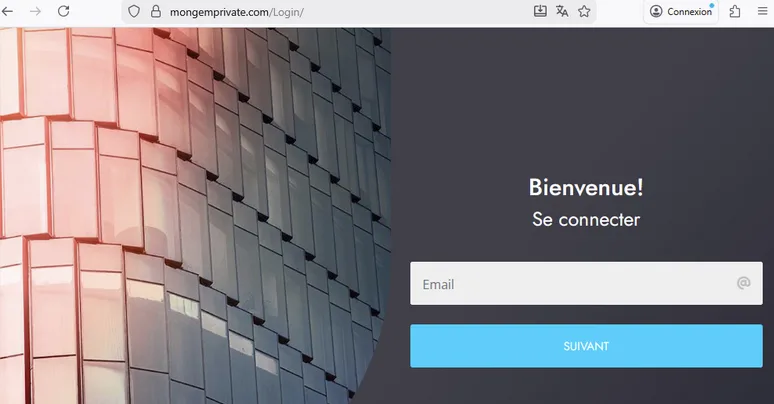
As no deposit was made, we did not gain direct access to the platform. However, the logo in the email signature provided several indications: it is identical to the one used by gemini.com, which is a legitimate crypto buying/selling platform and is recognized by the AMF.
Here, however, it is hosted on crm.mongemprivate.com, whose WHOIS data (similar to gestiongem.com) is registered anonymously.
Several points call for caution:
- Claiming to be a wealth manager, but without any questions related to KYC (mandatory identity verification), knowledge, or risk profile.
- Guaranteed returns.
- Anonymous domain registrations.
The elements gathered during the phone exchange make it possible to link this operation to a well-known type of investment fraud commonly referred to as a “boiler room” scam applied to digital assets (crypto).
In this model, operators, often organized in call center floors, contact previously qualified prospects (leads) in order to convince them to invest in fictitious or deceptive financial products. The sales pitch usually relies on promises of high returns, a sense of urgency, and gradual trust-building through low entry amounts.
Signs of Long-Term Scam Infrastructure Reuse
Analysis of the landing page used in the campaign also reveals several signs pointing to the reuse of older technical components. The confirmation page notably contains a copyright dated 2014, while some external resources rely on old JavaScript libraries, such as jQuery 1.9.1, hosted on infrastructure dating back to 2013.
An unprotected directory also provides information about the number of campaigns, their geographic scope, and their themes.

Analysis of the file naming convention shows several patterns:
| Acronym | Meaning |
|---|---|
| CRP | Crypto / Campaign theme |
| AM/GG/etc. | Amazon/Google / Impersonated brand |
| ES/IT/UK | Country code of the targeted markets |
These elements suggest operational continuity over several years, as well as the reuse of older kits within the same ecosystem.
The reuse of existing templates and infrastructure is a common practice in financial fraud campaigns, as it allows operators to quickly relaunch new operations while keeping development costs low.
Technical elements suggesting links with MD Lead
Several technical elements in this campaign suggest similarities with operations previously associated with MD Lead.
Several technical indicators match a campaign observed in April 2025, including:
- The use of the LeadManager platform, whose domain leadmanager.fr was historically associated with MD Lead;
- The use of the same redirection node;
- Infrastructure relying on Cloud resources, notably with Amazon;
- Similar URL patterns;
- The use of identical web page templates;
- An identical victim profile.

The investigation into certain functions in the HTML source code of the final site may also indicate the developer’s first name.
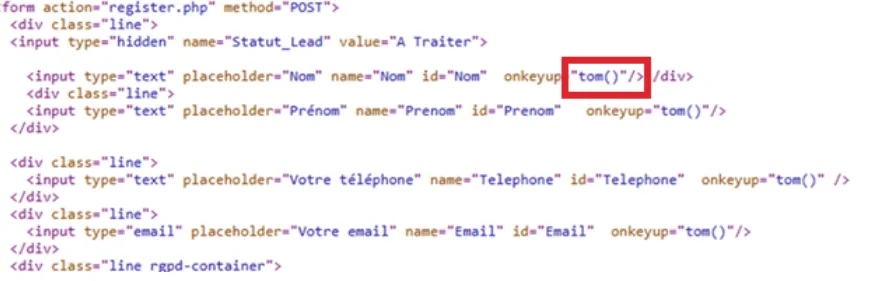
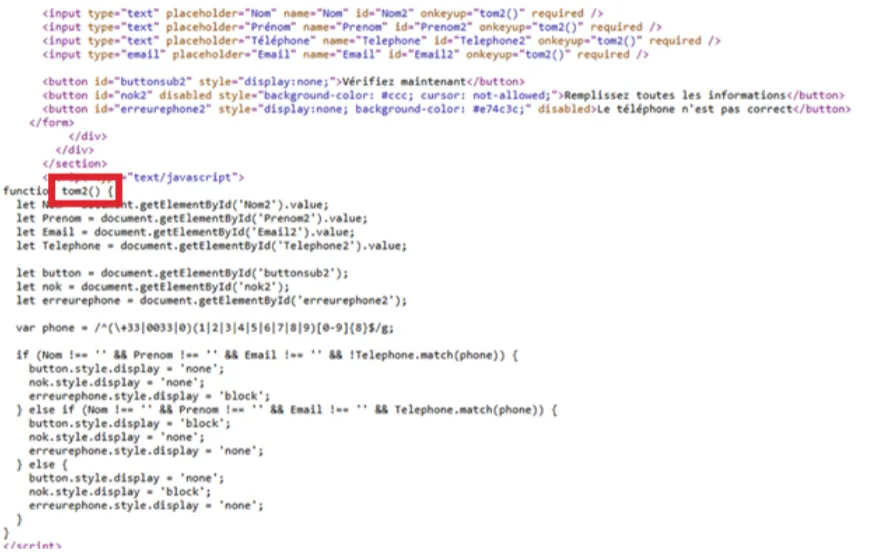
The source code contains a reference to the first name “Tom,” although it is not possible to formally attribute this element to a specific person.

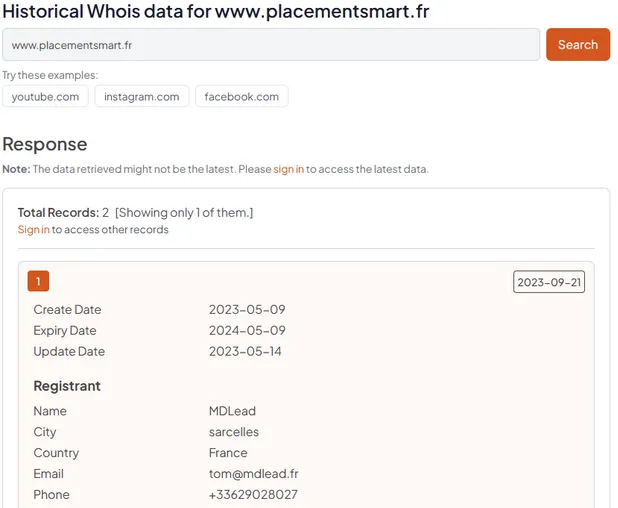
MD Lead was also the holder of the website placementsmart.fr, dedicated to lead generation for solar panels and investment in parking spaces. This website, now shut down, is listed on the AMF blacklist.

Although this company is now declared closed, the observed technical elements suggest that the associated infrastructure and tools continue to be used as part of new campaigns.
A company within an ecosystem
Although it is not possible to formally establish the capital or operational relationships between the entities, the observed elements suggest that MD Lead is part of a broader ecosystem of actors specializing in advertising and marketing.
The Hong Kong trail
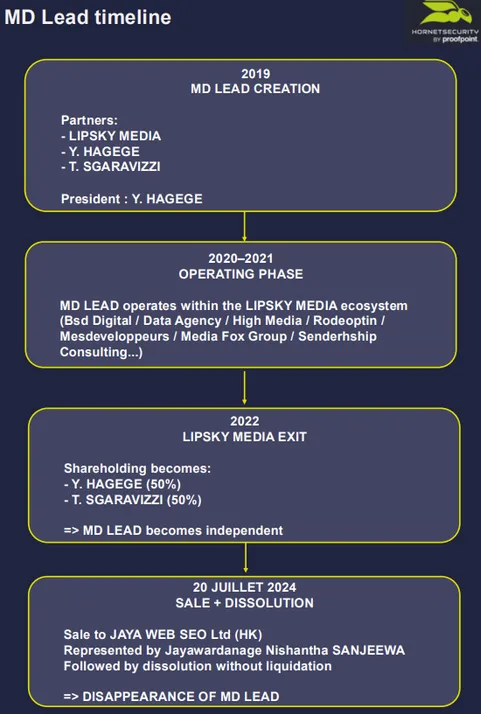
In July 2024, all of MD LEAD’s share capital was transferred to JAYA WEB SEO Ltd, based in Hong Kong, resulting in a complete change of control in favor of a foreign shareholder. On the same day, the company was dissolved through a universal transfer of assets (TUP). This legal mechanism results in the disappearance of MD LEAD without liquidation, with the automatic transfer of all its assets and liabilities to its new sole shareholder. In the course of a single coordinated operation, MD LEAD was both sold and absorbed, which ended its legal existence while transferring its economic substance to the Hong Kong structure.
Jayawardanage Nishantha SANJEEWA, through several companies registered in the United Kingdom and Hong Kong, acquired a significant number of companies. Apart from an SEO cluster initially owned by the same person, these companies do not appear to have any links between them, but the acquisitions follow a recurring pattern.

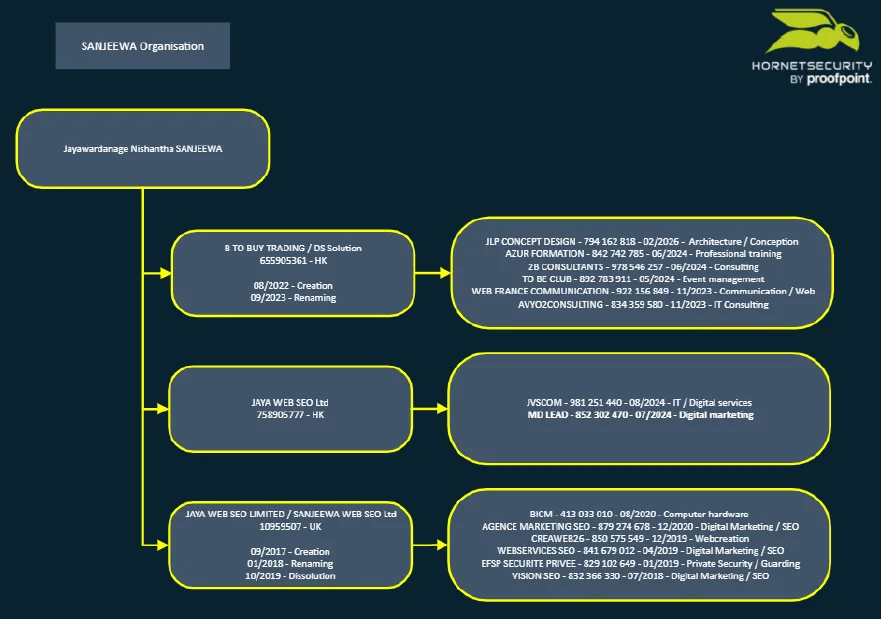
At this stage, it is not possible to determine whether the observed activities were actually taken over, nor to establish with certainty the exact purpose of these operations.
Key takeaways
This campaign fits into an industrial investment fraud model in which phishing mainly serves to feed lead generation pipelines.
The operation relies on a structured chain: mass distribution, data collection, integration through lead platforms, then exploitation by call centers, with signs of infrastructure reuse and operational continuity over time.
Analysis of the source code indicates that the data is routed to the LeadManager platform, itself associated with infrastructure historically linked to MD Lead, suggesting ties with known actors in this ecosystem, although this does not allow for formal attribution at this stage.
This campaign illustrates the need to analyze phishing as an entry point into a broader fraudulent chain, rather than as an end in itself.
Indicators of Compromise (IOCs)
| Type | Value | Description |
|---|---|---|
| Domain | agasters.fr | Domain used for sending |
| URL | https://agasters.fr/crap1659FC | Example URL |
| AS | AS16509 | Amazon.com, Inc. |
| Domain | dynarend.fr | Redirection node |
| Domain | coherence-finie.com | Final domain after redirection |
| URL | https://coherence-finie.com/crypto-amazon2/?subaff_id={ID_campagne}&aff iliateid=SUBAFF&transaction_id=CLICKID /?query={base64} | Final URL pattern |
| Tool | leadmanager | CRM used |
| Domain | leadmanager.fr | Web interface of the leadmanager CRM |
| Domain | asimers.fr | Domain used for sending |
| Domain | ajaneks.fr | Domain used for sending |
| Domain | nibistens.com | Domain used for sending |
| Domain | akorel.fr | Domain used for sending |
| Domain | alanets.fr | Domain used for sending |
| Domain | afibande.fr | Domain used for sending |
| Domain | aniverts.fr | Domain used for sending |
| Domain | aristener.fr | Domain used for sending |
| Domain | acinest.fr | Domain used for sending |
| Domain | akamert.fr | Domain used for sending |
| Domain | agorin.fr | Domain used for sending |
| Domain | nidyaton.com | Domain used for sending |
| Domain | adelric.fr | Domain used for sending |
| Domain | alrelis.fr | Domain used for sending |
| Domain | atinafer.fr | Domain used for sending |
| Domain | awister.fr | Domain used for sending |
| Domain | asrelis.fr | Domain used for sending |
| Domain | apevion.fr | Domain used for sending |
| Domain | ajnorel.fr | Domain used for sending |
| Domain | atuvorel.fr | Domain used for sending |
| Domain | apariser.fr | Domain used for sending |
| Domain | nicareste.com | Domain used for sending |
| Domain | azanber.fr | Domain used for sending |
| Domain | ahvion.fr | Domain used for sending |
| Domain | anarelis.fr | Domain used for sending |
| Domain | adiverts.fr | Domain used for sending |
| Domain | amaniste.fr | Domain used for sending |
| Domain | afrynel.fr | Domain used for sending |
| … | ||
| Phone | 0162142189 | Phone number used by the call center |
| [email protected] | Email used by the call center | |
| Domain | gestion-gem.com | Domain used by the call center |
| Domain | mongemprivate.com | Fraudulent crypto investment domain |
