

Email Threat Review May 2021
Summary
In this installment of our monthly email threat review, we present an overview of the email-based threats observed in May 2021 and compare them to the previous month’s threats.
The report provides insights into:
- Unwanted emails by category
- File types used in attacks
- Industry Email Threat Index
- Impersonated company brands and organizations
- Highlighted threat email campaigns
- Ransomleaks
Unwanted emails by category
The following table shows the distribution of unwanted emails by category.
| Email category | % |
| Rejected | 81.56 |
| Spam | 13.81 |
| Threat | 3.73 |
| AdvThreat | 0.87 |
| Content | 0.03 |
The following time histogram shows the email volume per category per day.

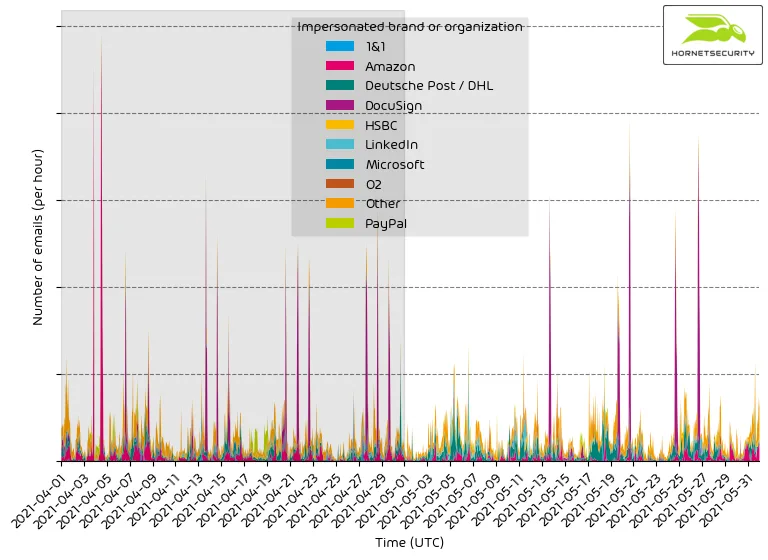
The spike in rejected emails between 2021-05-23 and 2021-05-26 is caused by a wave of sextortion scam emails targeting German language users.
This campaign and the resulting spike in rejected emails is similar to the one observed in March1 in which the attackers made around 5,000 €. This time there were no incoming transactions to the attacker’s Bitcoin wallets used in the attack.
Methodology
The listed email categories correspond to the email categories listed in the Email Live Tracking of Hornetsecurity’s Control Panel. So our users are already familiar with them. For others, the categories are:
| Category | Description |
| Spam | These emails are unwanted and are often promotional or fraudulent. The emails are sent simultaneously to a large number of recipients. |
| Content | These emails have an invalid attachment. The administrators define in the Content Control module which attachments are invalid. |
| Threat | These emails contain harmful content, such as malicious attachments or links, or they are sent to commit crimes like phishing. |
| AdvThreat | Advanced Threat Protection has detected a threat in these emails. The emails are used for illegal purposes and involve sophisticated technical means that can only be fended off using advanced dynamic procedures. |
| Rejected | Our email server rejects these emails directly during the SMTP dialog because of external characteristics, such as the sender’s identity, and the emails are not analyzed further. |
File types used in attacks
The following table shows the distribution of file types used in attacks.
| File type (used in malicious emails) | % |
| Archive | 33.1 |
| Other | 19.9 |
| HTML | 17.8 |
| Excel | 7.6 |
| 7.5 | |
| Executable | 5.8 |
| Disk image files | 4.7 |
| Word | 2.8 |
| Powerpoint | 0.6 |
| Script file | 0.2 |
| 0.1 | |
| LNK file | 0.0 |
The following time histogram shows the email volume per file type used in attack per 7 days.

Industry Email Threat Index
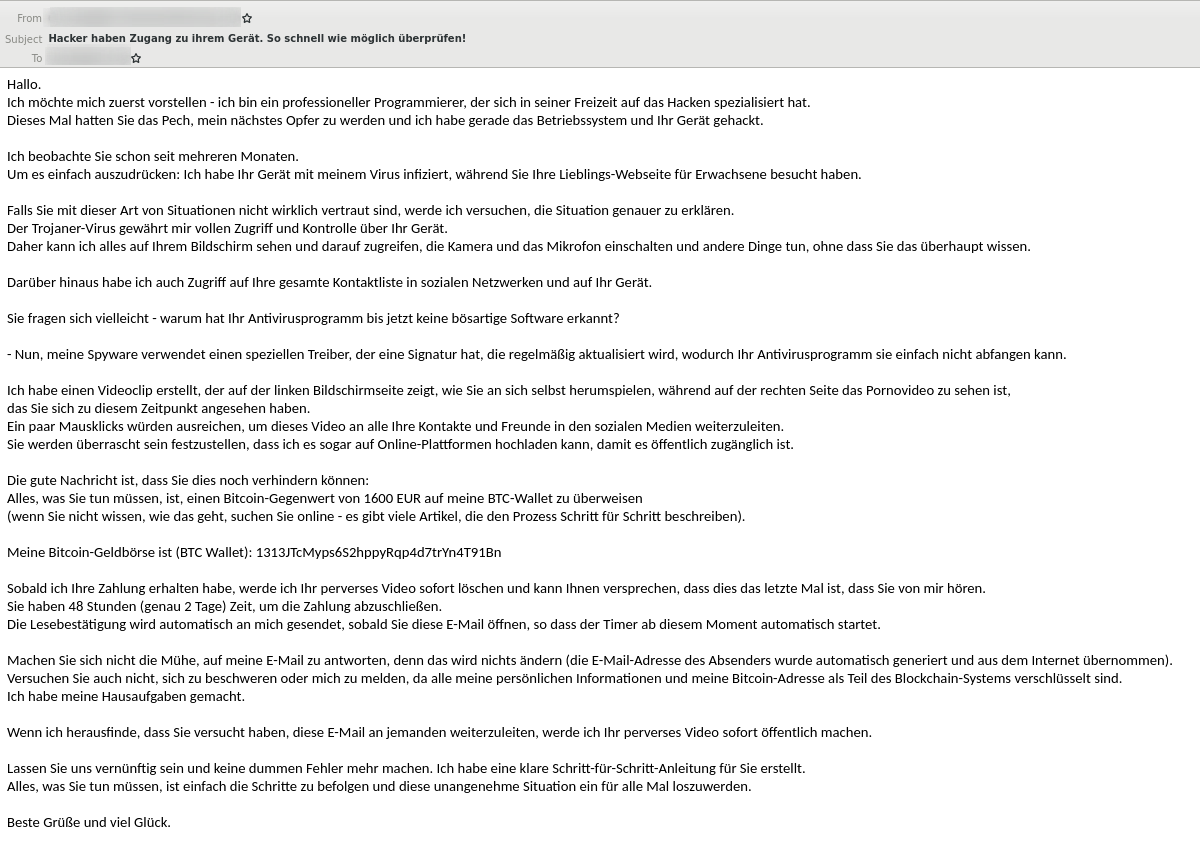
The following table shows our Industry Email Threat Index calculated based on the number of threat emails compared to clean emails received (in median) by each industry.
| Industries | Share of threat in threat and clean emails |
| Research industry | 6.9 |
| Transport industry | 5.3 |
| Manufacturing industry | 5.0 |
| Education industry | 4.1 |
| Healthcare industry | 4.0 |
| Media industry | 3.9 |
| Automotive industry | 3.9 |
| Entertainment industry | 3.8 |
| Utilities | 3.8 |
| Hospitality industry | 3.8 |
The following bar chart visualizes the email-based threat posed to each industry.
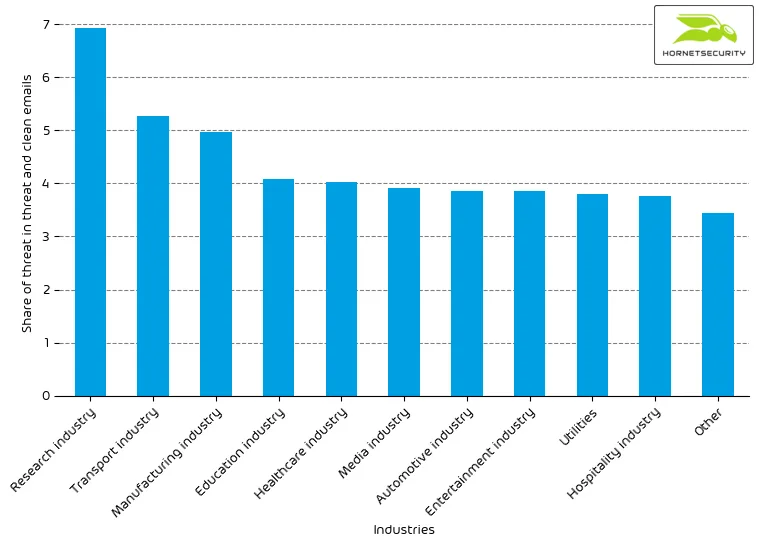
For comparison last month’s email threat index bar chart:
Methodology
Different (sized) organizations receive a different absolute number of emails. Thus, we calculated the percent share of threat emails from each organization’s threat and clean emails to compare organizations. We then calculate the median of these percent values overall organizations within the same industry to form the industry’s final threat score.
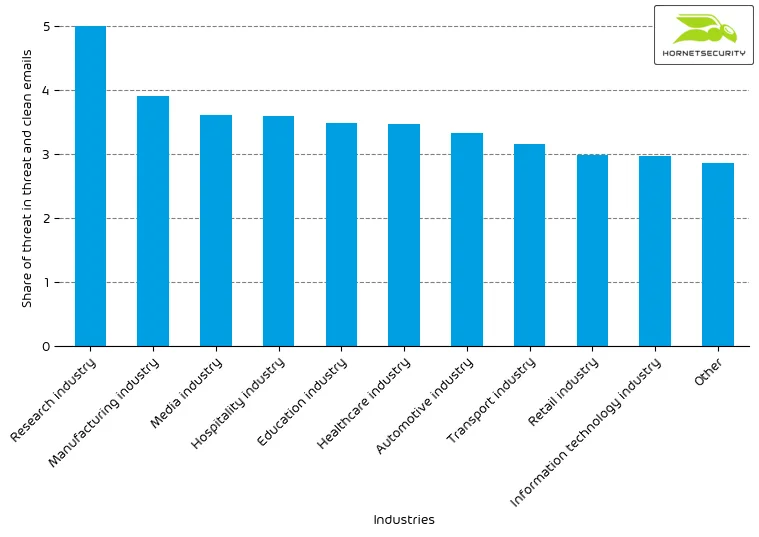
Impersonated company brands and organizations
The following table shows which company brands our systems detected most in impersonation attacks.
| Impersonated brand or organization | % |
| DocuSign | 19.9 |
| Amazon | 17.6 |
| Deutsche Post / DHL | 16.8 |
| Other | 15.4 |
| 4.0 | |
| Microsoft | 2.8 |
| PayPal | 2.7 |
| 1&1 | 2.5 |
| HSBC | 2.1 |
| O2 | 2.0 |
The following time histogram shows the email volume for company brands detected in impersonation attacks per hour.
It’s a constant stream of phishing and other attacks impersonating big brands to entice recipients to open the emails.
Highlighted threat email campaigns
In this section, we want to highlight some malspam campaigns of prominent, well-known threat actors.
The following time histogram shows the email volume for highlighted threat email campaigns per hour.
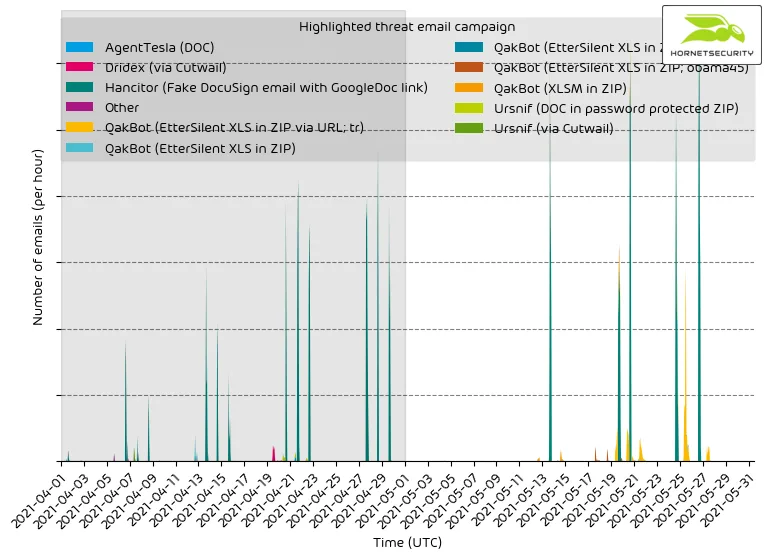
We can see that the malspam waves of the selected campaigns have well-defined start and endpoints, unlike less sophisticated mass-spam email campaigns, which will send email in a constant stream.
Please be advised that this does not contain all campaigns. The ranking, as well as volume figures, should therefore not be taken as a global ranking.
From the data, we can see that the Hancitor malspam impersonating DocuSign is a consistent reoccurring high volume malspam campaign.
At the end of the month, the increase in URL-based QakBot “tr” (named after the configuration tag/campaign ID tr found in the distributed QakBot malware’s configuration) malspam can be seen. This campaign (as other QakBot malspam campaigns) uses email conversation threat hijacking.2
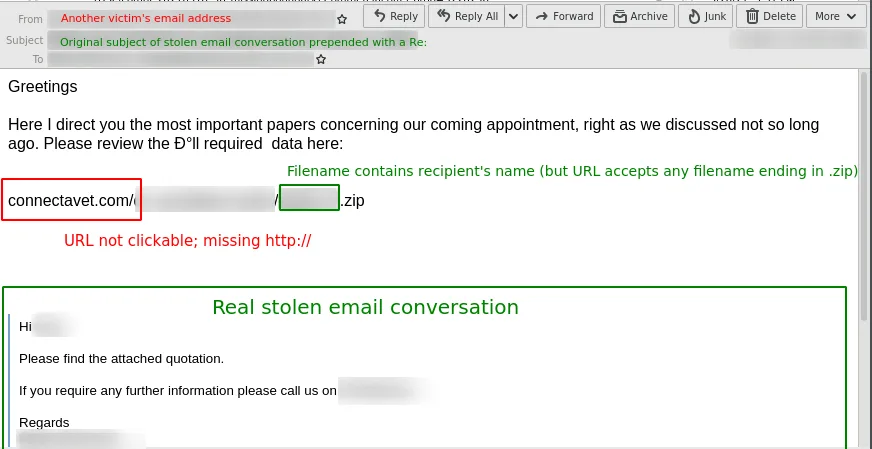
Another interesting aspect of the campaign is that it uses non-clickable plain text URLs missing the http://. Victims must thus copy the URL manually to their browser. This is likely done in hopes that URL filters do not detect the URL in this form. Obviously, the campaign uses various compromised websites to host the malicious ZIP archives, further complicating detection.
Methodology
Hornetsecurity observes hundreds and thousands of different threat email campaigns of varying threat actors ranging from very unsophisticated low-effort attacks to highly complex obfuscated attack schemes. Our highlighting includes only major sophisticated threat email campaigns.
Ransomleaks
Threat actors continue to leak data stolen from ransomware victims to pressure them into paying not only for decrypting the files encrypted by the ransomware but also for not making the data stolen before encryption public. We observed the following number of leaks on ransomware leaksites:
| Leaksite | Number of victim data leaks |
| Conti | 73 |
| Avaddon | 56 |
| Pysa | 33 |
| Darkside | 25 |
| REvil | 21 |
| Lorenz | 19 |
| Babuk | 15 |
| Xing Team | 13 |
| Nephilim | 8 |
| Cuba | 6 |
| Networm | 5 |
| Grief | 5 |
| Cl0p | 4 |
| RansomEXX | 4 |
| MountLocker | 3 |
| Everest | 3 |
| RagnarLocker | 3 |
| Astro Team | 2 |
The following bar chart visualizes the number of victim data leaks per leaksite.
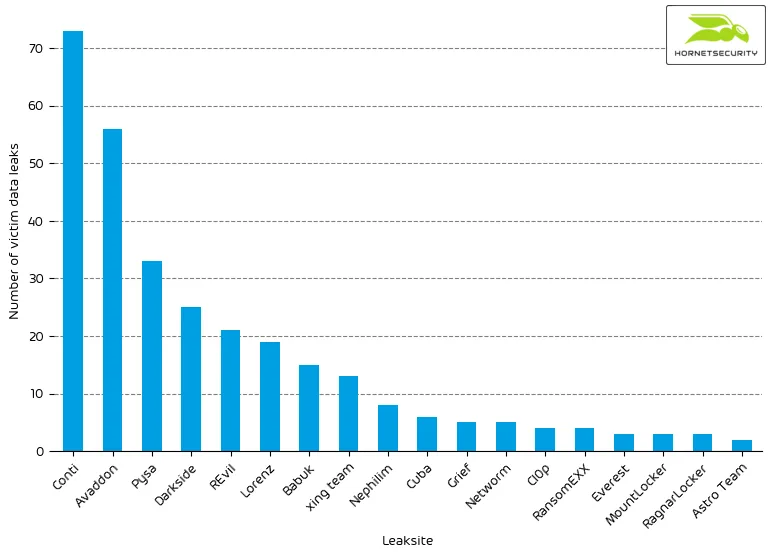
We added data collection for the following ransomware leaksites:
The leaksite of the Cuba ransomware was first seen at the end of 2019. However, the group was not very active. The leaksite currently features six leaks.
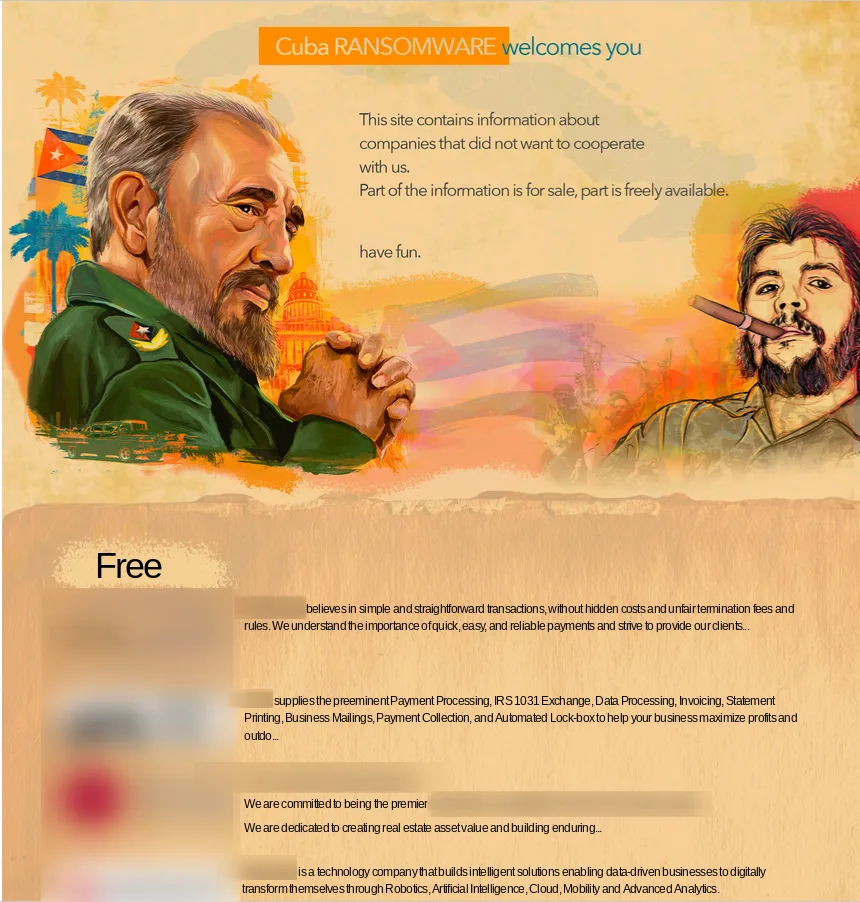
Cuba ransomware has recently been reported to be cooperating with the Hancitor malware, the malspam campaigns of which we reported on in a previous section. We, therefore, added the Cuba ransomware leaksite to our dataset.
The leaksite of the Xing Team was announced via the Astro Team leaksite on 2021-05-06 as a new partner of the Astro Team.
The Xing Team leaksite features an identical layout to the Astro Team leaksite, but contains different data leaks.
What this partnership entails is currently unknown.
Another leaksite that emerged this month is the leaksite of the Prometheus ransomware. On its site, they claim an affiliation with the REvil ransomware. However, it needs to be seen what that affiliation is and whether the REvil ransomware even knows that this new leaksite claims an affiliation with them.
The Prometheus leaksite does not remove entries for companies that have paid the ransom or for data it could sell. The respective entries are simply updated to reflect whether the company paid or the data has been soled.
Another new entry is the Grief leaksite.

Currently, it is unknown what ransomware is associated with the Grief leaksite, whether it is an already known ransomware rebranded as Grief or whether they use their own ransomware.


