

Email Threat Review June 2022
Summary
In this monthly email threat review installment, we present an overview of the email-based threats observed in June 2022 and compare them to the previous month’s threats.
The report provides insights into:
- Unwanted emails by category
- File types used in attacks
- Industry Email Threat Index
- Attack techniques
- Impersonated company brands and organizations
Unwanted emails by category
The following table shows the distribution of unwanted emails per category.
| Email category | % |
| Rejected | 78.69 |
| Spam | 15.90 |
| Threat | 4.13 |
| AdvThreat | 1.23 |
| Content | 0.05 |
The following histogram shows the email volume per category per day.

Methodology
The listed email categories correspond to the email categories listed in the Email Live Tracking of Hornetsecurity’s Control Panel. So our users are already familiar with them. For others, the categories are:
| Category | Description |
| Spam | These emails are unwanted and are often promotional or fraudulent. The emails are sent simultaneously to a large number of recipients. |
| Content | These emails have an invalid attachment. The administrators define in the Content Control module which attachments are invalid. |
| Threat | These emails contain harmful content, such as malicious attachments or links, or they are sent to commit crimes like phishing. |
| AdvThreat | Advanced Threat Protection has detected a threat in these emails. The emails are used for illegal purposes and involve sophisticated technical means that can only be fended off using advanced dynamic procedures. |
| Rejected | Our email server rejects these emails directly during the SMTP dialog because of external characteristics, such as the sender’s identity, and the emails are not analyzed further. |
File types used in attacks
There are a few reasons why HTML, PDF, ZIP, and Excel files are often used in email attacks. One reason is that these files can be used to embed malicious code that can be executed when the file is opened. The victims can easily execute executable files, e.g., .exe files, without needing additional software, e.g., Microsoft Office. Another reason is that these files can be used to trick users into divulging sensitive information, such as passwords or credit card numbers. This is especially relevant for HTML files. Often phishers send HTML files, and when opened, they appear to be the login menu to banking sites. Finally, these files can be used to install, deploy and start malware on a victim’s computer.
The following table shows the distribution of file types used in attacks.
| File type (used in malicious emails) | % |
| Archive | 35.6 |
| HTML | 18.5 |
| Excel | 14.4 |
| 12.6 | |
| Disk image files | 5.5 |
| Executable | 5.0 |
| Word | 3.5 |
| Other | 4.9 |
The following histogram shows the email volume per file type used in attacks per 7 days.

Industry Email Threat Index
Attackers preferably target the research industry this month. The research industry is full of sensitive information. By successfully phishing key employees, attackers may get access to critical research details. Additionally, the research industry is often slow to adopt new security technologies due to budget constraints, making it easier for attackers to exploit vulnerabilities.
The following table shows our Industry Email Threat Index calculated based on the number of threat emails compared to each industry’s clean emails (in median).
| Industries | Share of threat in threat and clean emails |
| Research industry | 7.2 |
| Manufacturing industry | 4.2 |
| Transport industry | 4.0 |
| Automotive industry | 3.9 |
| Utilities | 3.9 |
| Information technology industry | 3.8 |
| Media industry | 3.7 |
| Mining industry | 3.7 |
| Retail industry | 3.4 |
| Agriculture industry | 3.4 |
The following bar chart visualizes the email-based threat posed to each industry.
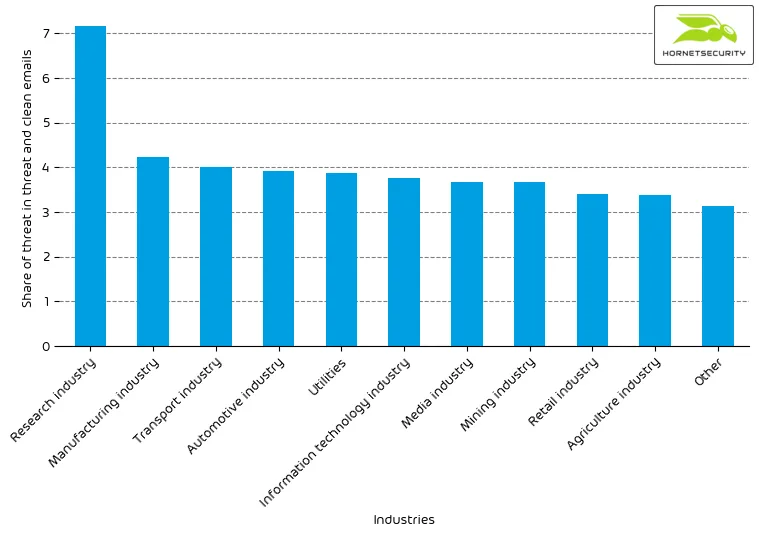
The threat index of the research industry remains elevated above 7.
Methodology
Different (sized) organizations receive a different absolute number of emails. Thus, we calculate the percent share of threat emails from each organization’s threat and clean emails to compare organizations. We then calculate the median of these percent values for all organizations within the same industry to form the industry’s final threat score.
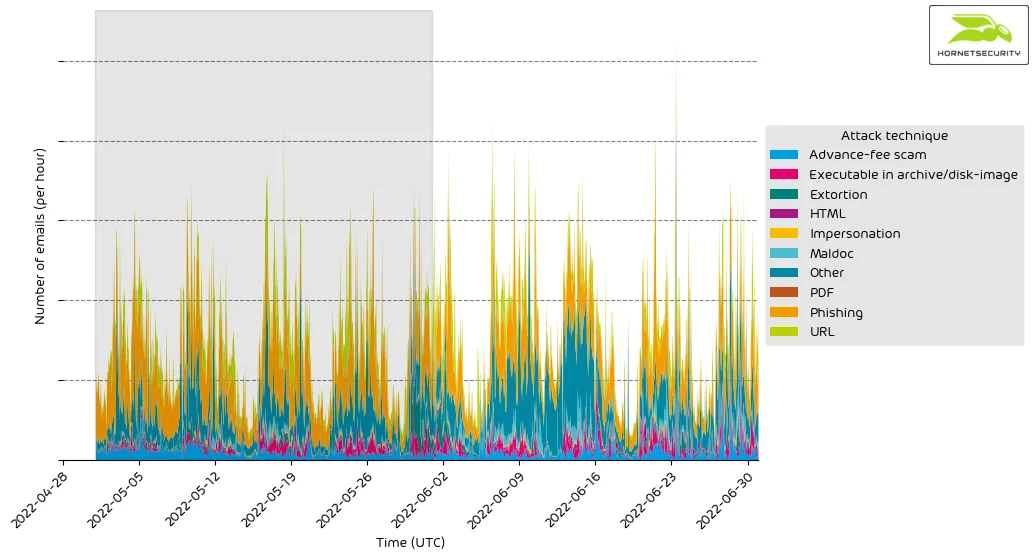
Attack techniques
Phishing dominates email attacks because it is a very effective way to trick people into giving away their personal information or clicking on malicious links. Phishing emails often look like they come from a legitimate source, such as a well-known company or website. They often contain urgent or alarming language that can trick people into taking action without thinking. Modern tools allow phishers to retrieve 2FA codes or session cookies from their victims to circumvent security.
The following table shows the attack techniques used in attacks.
| Attack technique | % |
| Phishing | 30.7 |
| URL | 11.5 |
| Advance-fee scam | 7.4 |
| Executable in archive/disk-image | 5.3 |
| Extortion | 4.1 |
| Maldoc | 3.4 |
| HTML | 2.3 |
| Impersonation | 1.3 |
| 0.3 | |
| Other | 33.8 |
The following histogram shows the email volume per attack technique used per hour.
Impersonated company brands and organizations
Some of the most commonly impersonated brands in email phishing attacks are banks, credit card companies, shipping companies, and online retailers. These types of attacks usually involve the attacker sending an email that appears to be from a legitimate company, and asking the recipient to provide personal or financial information. In many cases, the email will contain a link that leads to a fake website that looks identical to the real website. The attacker then uses the information that is collected to commit fraud or identity theft.
The following table shows which company brands and organizations our systems detected most in impersonation attacks.
| Impersonated brand or organization | % |
| Sparkasse | 17.3 |
| DHL | 11.8 |
| Amazon | 11.3 |
| 1&1 | 4.6 |
| Postbank | 4.1 |
| Microsoft | 3.8 |
| UPS | 3.8 |
| Volks- und Raiffeisenbank | 3.3 |
| 2.9 | |
| DocuSign | 2.7 |
| Other | 34.4 |
The following histogram shows the email volume for brands and organizations detected in impersonation attacks per hour.
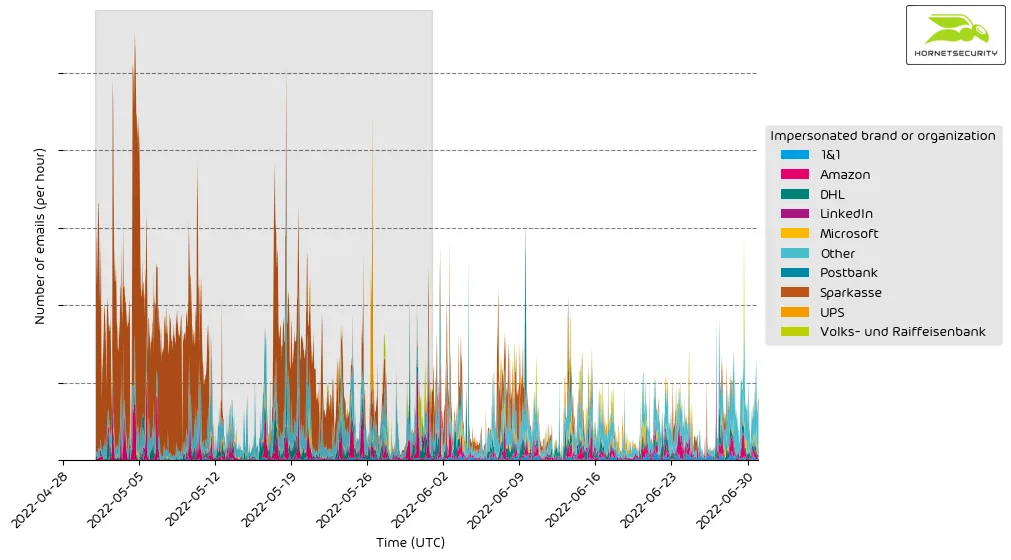
It’s a constant stream of phishing and other attacks impersonating big brands and organizations to entice recipients to open the emails.


