


EMAIL ENCRYPTION
Fully automated, secure and effective email encryption
Send a request now!
WHAT happens in email should stay in email
Cybercriminals are always seeking to tap into business emails containing sensitive and confidential information, whether to use them for spying or a successful cyberattack. With Hornetsecurity’s Email Encryption, you can rely on all-round encryption exchanges for secure email communication.
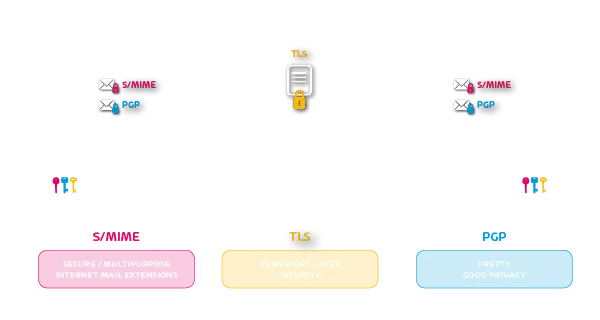
HORNETSECURITY’S EMAIL ENCRYPTION SUPPORTS ALL STANDARD ENCRYPTION TECHNOLOGIES
Overview of all Hornetsecurity
email encryption features
Testing option for encryption suitability
Automatic digital signing & encryption of outgoing emails via S/MIME and PGP
Automatic certificate management & key storage
Individual setup and definition of encryption policies
Personal email certificates
Confidential communication via Websafe
BUSINESS EMAIL ENCRYPTION FROM HORNETSECURITY: MINIMAL ADMINISTRATIVE WORK FOR IT ADMINISTRATORS
Handling of user certificates
The Hornetsecurity’s Control Panel can be used to request, renew or permanently obtain new certificates for users (Subscription function: A certificate subscription may incur additional costs in accordance with the price list).
Adaptable scalability
Because Hornetsecurity’s Email Encryption is based on cloud technology, it is always possible to adjust the number of encrypted email users to customer needs.
Individual adaptation of encryption guidelines
Administrators typically set identical encryption policies for an organization. Exceptions to this standard can be defined at domain, group and user level. This ranges from different encryption technologies through to deactivation of encryption.
Automatic updates
This cloud-based encryption service ensures that customers are always using the latest version of the service. Administrators do not need to worry about software and hardware updates.
LEARN HOW YOU CAN BENEFIT
FREE DOWNLOADS
For more product details, take a look at our Fact Sheets.
Email Encryption >
365 Total Protection >
Security Awareness Service >
EDUCATIONAL CONTENT
We have some well researched content pieces for you! Watch our Webinars, read our eBooks and listen to our Podcast!


