
IT Pro Tuesday
FREE TOOLS & ADVICE EVERY WEEK
JOIN THOUSANDS OF IT PROS AND GET 5+ NEW FREE TOOLS, TIPS, HIGH-QUALITY ARTICLES, AND OTHER HAND-PICKED CONTENT TO YOUR INBOX EVERY TUESDAY
Welcome back to IT Pro Tuesday!
We’re looking for your favorite tips and tools we can share with the community… those that help you do your job better and more easily. Please share your suggestions on the IT Pro Tuesday subreddit, and we’ll be featuring them in the coming weeks.
Now on to this week’s list!
Top 5 IT Tools as of July 15th
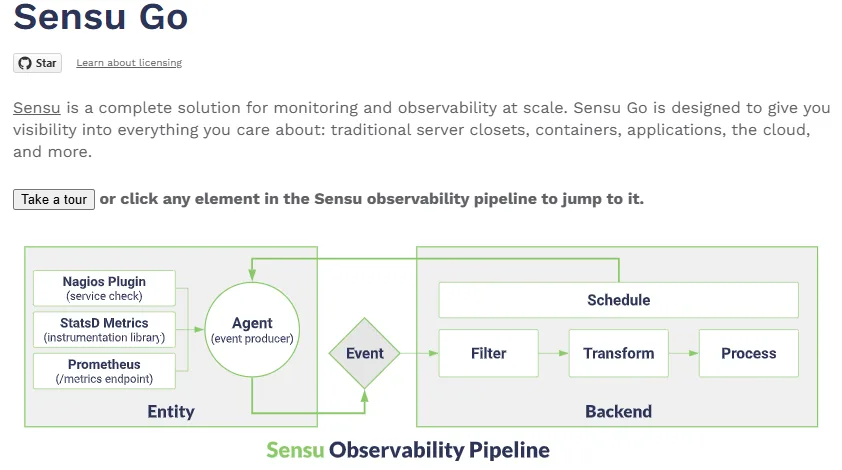
Agent-Based Observability Tool
Starting this edition with an essential tool for sysadmins that provides comprehensive monitoring and observability across diverse environments, ensuring visibility into infrastructure and applications, along with easy integration with existing tools. Yes, that’s Sensu Go.
UDP Echo Tester
UDPing helps sysadmins measure network performance by accurately determining latency and packet loss, enabling them to optimize links and troubleshoot connectivity issues more effectively.
Restricted Shell Backup Enforcement
In order to take control of your security, rbash enhances system security for sysadmins by limiting user access and capabilities, protecting critical system components, and maintaining controlled environments without sacrificing functionality.
Linux Power Consumption Profiler
PowerTOP is a vital tool for sysadmins focused on energy efficiency, allowing them to identify power-hungry processes and implement optimizations for more sustainable system operations.
Essential Tech Insights for Sysadmins
You can find a wealth of resources on YouTube, and Raid Owl stands out as one of the best. This channel offers valuable insights for sysadmins passionate about technology, sharing tips and resources that enhance their expertise and foster a community of like-minded individuals.
P.S. Bonus Free TOOLS/RESOURCES
Mailcow is an exceptional open-source suite for effortlessly running a self-hosted mail server. It integrates a powerful collection of applications like SOGo, Postfix, and Dovecot, all managed through an intuitive web interface for seamless account management. It’s completely free, dockerized, and includes rspamd, along with a fantastic web GUI, making upgrades as simple as a single command.
Samplicator is an effective tool designed for receiving UDP datagrams on a specified port and efficiently resending them to multiple receivers. It’s perfect for exporting NetFlow traffic to more than one NetFlow collector. With its advanced configuration options, you can precisely set a unique sampling divisor N for each receiver, ensuring that they receive only one in N of the received packets. This capability makes Samplicator an essential solution for managing your network traffic.
Dear IT-Professional,
The world of technology changes quickly. Staying ahead means having the right tools, insights, and strategies at your fingertips. That’s where IT Pro Tuesday comes in.
Every Tuesday, we deliver a curated selection of free resources, expert advice, must-read articles, and essential updates – all designed to help you work smarter, solve problems faster, and stay at the top of your game.
Whether you’re a seasoned IT professional or just looking to sharpen your skills, this newsletter ensures you never miss out on game-changing tools and insights.
Sign up now – it’s free, and it could be your smartest move this week!
Access to exclusive content
In addition to the free tools, you will also receive links to high-quality cybersecurity content, providing crucial insights to help you defend against the latest cyber threats. This includes free access to valuable resources such as articles, eBooks, detailed analyses, actionable recommendations, case studies, white papers, webinars, videos and more.
JOIN THOUSANDS OF IT PROS AND SIGN UP TODAY
Sign up now!
"*" indicates required fields
Access to exclusive content
In addition to the free tools, you will also receive links to high-quality cybersecurity content, providing crucial insights to help you defend against the latest cyber threats. This includes free access to valuable resources such as articles, eBooks, detailed analyses, actionable recommendations, case studies, white papers, webinars, videos and more.
Curious how the newsletter looks like? Have a sneak peek what to expect:
Note: we have no affiliation with any of the third-party tools or resources shared unless explicitly stated. We scour popular forums and online groups to identify the most highly recommended and rated resources from the IT community and from our own highly skilled team.
More about Hornetsecurity
What you can expect
As an expert in cloud security, we regularly inform our subscribers about the latest changes in IT security. This includes current blog posts, press releases, technical papers and other relevant security information.
Tracking and Transparency
We always strive to provide our website visitors and subscribers personalized information. We constantly improve our offerings and knowledge base, so that you have the best user experience possible while browsing our website.
Double-Opt-In / Opt-Out
After you register, we will send you a confirmation email. This notification includes a link to confirm receipt of Hornet News (Double-Opt-In). In addition, subscribers have the opportunity to cancel their free subscription at any time. At the end of each email you will find an unsubscribe link (Opt-Out).
Privacy Policy
Detailed information on the collection, storage, processing of information and the possibility of withdrawal can be found in our privacy policy.
