

Spear Phishing
Was ist ein Spear-Phishing-Angriff?
In diesem Artikel erfahren Sie, was Spear-Phishing ist, wie es sich von normalem Phishing unterscheidet und warum es eine wachsende Bedrohung für Unternehmen darstellt. Wir schauen uns an, wie diese Angriffe funktionieren, welche Techniken häufig verwendet werden und auf welche Warnzeichen Sie achten sollten.
Was ist Spear Phishing?
Spear Phishing ist eine Form des Social Engineering, bei der häufig die Identität einer Person missbraucht wird, um den Empfänger dazu zu verleiten, eine gewünschte Handlung auszuführen, die in der Regel finanzieller Natur ist. Oft gibt sich ein Hacker als jemand aus, den das Opfer kennt, beispielsweise als Kollege, Vorgesetzter, Kunde oder Lieferant.
Im Gegensatz zu herkömmlichen Phishing-E-Mails richten sich Spear-Phishing-E-Mails tatsächlich an Personen, die gefälschte E-Mails normalerweise mit einer gesunden Skepsis behandeln würden. Das bedeutet, dass Spear-Phishing-E-Mails viel effektiver beim Aufbau von Vertrauen sind. Insbesondere nutzt es die Gutgläubigkeit des Empfängers aus, indem es ihm das Gefühl gibt, sicher zu sein – beispielsweise aufgrund von scheinbar vertrauten Absenderadressen oder dem Ruf des in der E-Mail genannten Unternehmens.
Mit dieser erfolgreichen Täuschung kann der Cyberkriminelle nun die Spear-Phishing-Attacke auf die nächste Stufe heben. Das ahnungslose Opfer entdeckt die Täuschung erst viel später, wenn es in der Regel zu spät ist, um noch zu reagieren.
So funktioniert ein Spear-Phishing-Angriff in der Praxis
Sobald das Opfer eine betrügerische E-Mail erhalten hat, kann es dazu verleitet werden, einen Link herunterzuladen, über den sorgfältig versteckte Malware installiert wird. Alternativ kann ein Link das Opfer auf eine gefälschte Website führen, auf der ein Formular ausgefüllt wird, um persönliche Daten zu sammeln.
In den letzten Jahren hat sich zunehmend gezeigt, dass Spear-Phishing nicht mehr auf die E-Mail-Kommunikation beschränkt ist. Auch soziale Netzwerke werden für diese Art von Angriffen genutzt. Sobald der Link oder die Malware auf dem Computer des potenziellen Opfers platziert wurde, kann sich der Cyberkriminelle zurücklehnen und abwarten.
Spear-Phishing vs. Phishing
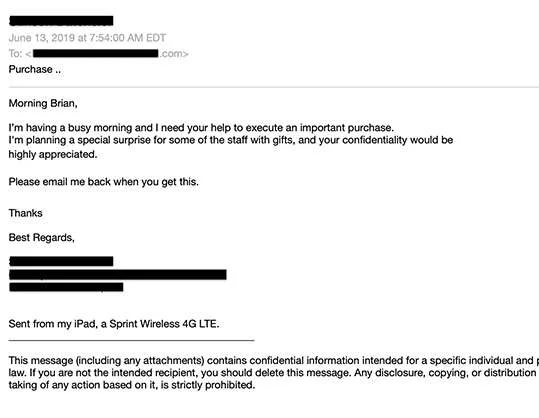
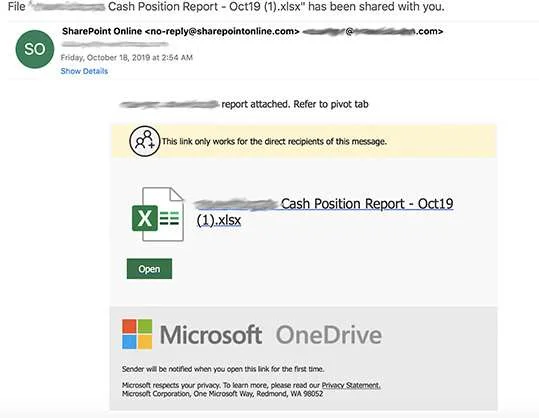
Sowohl Spear-Phishing- als auch Phishing-Angriffe nutzen Identitätsdiebstahl, um Betrug zu begehen. Der Unterschied zwischen den beiden besteht darin, dass Spear-Phishing-E-Mails sich als Personen ausgeben, während Phishing-E-Mails sich als Marken ausgeben. Im Gegensatz zu Phishing zielt Spear-Phishing auf eine einzelne Person ab, enthält keine Links oder Anhänge in der E-Mail und enthält in der Regel eine Aufforderung zu einer Überweisung, Geschenkkarten oder Änderungen der Direktüberweisung anstelle von Kontoinformationen. Nachfolgend finden Sie zwei Beispiele für eine Phishing-E-Mail im Vergleich zu einer Spear-Phishing-E-Mail:
Die Ziele von Spear-Phishing
Angreifer informieren sich in der Regel vorab über ihr Ziel. Vorname, Nachname, Geburtsdatum, Wohnort, Straße, Hobbys und Informationen über Familienmitglieder, Freunde und Geschäftspartner sind im Internet leicht zu finden. Es gibt unzählige öffentlich zugängliche Datenbanken. In den meisten Fällen sind es die Nutzer selbst, die dafür sorgen, dass ihre Profilinformationen für Dritte frei einsehbar sind. Dies gilt insbesondere für soziale Medien.
Der Angreifer erfährt auch Informationen wie die Vorlieben und Gewohnheiten des Opfers, indem er beispielsweise sieht, welche Online-Käufe es zu welcher Zeit bei eBay oder Amazon getätigt hat. Selbst das Verfolgen von Bewegungsmustern ist für Cyberkriminelle keine große Herausforderung mehr. Mit GPS können viele Nutzer sogenannter Tracking-Dienste einem Angreifer sogar dabei helfen, genau herauszufinden, wo sich ein Nutzer befindet, wann er dort ist und wie lange.
Phishing/Social Engineering machte 2018 52 % der Cyberangriffe auf KMUs aus – Keeper/Ponemon
Arten von E-Mail-Spoofing
Um Empfänger dazu zu verleiten, zu glauben, dass sie eine E-Mail von einem vertrauenswürdigen Absender lesen, verwenden Spear-Phisher eine Technik namens „Spoofing“, mit der sie sich als legitimer Absender und E-Mail-Adresse ausgeben können. Es gibt drei Hauptmethoden des E-Mail-Spoofings :
Display Name Spoofing
Bei der Anzeige-Namensfälschung wird der Name des Absenders gefälscht, nicht jedoch die E-Mail-Adresse. Dies ist effektiv, da viele Benutzer dem Absender sofort vertrauen, wenn sie den Namen sehen. Es ist auch deshalb effektiv, weil viele E-Mail-Clients, insbesondere auf Mobiltelefonen, nur den Namen des Absenders und nicht die E-Mail-Adresse anzeigen.
Domain spoofing
Diese Methode ist ausgefeilter als das Spoofing des Anzeigenamens, aber auch leichter durch SPF (Secure Policy Framework), DMARC (Domain Message Authentication Reporting) und DKIM (Domain Keys Identified Email) zu erkennen. Beim Domain-Spoofing kann ein Spear-Phisher die E-Mail-Adresse angeben, die er spoofen möchte. Wenn eine E-Mail-Adresse eine exakte Kopie eines vertrauenswürdigen Absenders ist, ist es unwahrscheinlich, dass Benutzer erkennen, dass die E-Mail gefälscht ist.
Cousin Domains
Eine „Close Cousin“-E-Mail-Adresse ist fast identisch mit einer legitimen Adresse, mit nur einer geringfügigen Änderung. In der Vergangenheit waren „Close Cousin“-Spoofing-Versuche offensichtlicher, wie beispielsweise mIcrosoft.com anstelle von microsoft.com. Heute sind die Versuche ausgefeilter und schwerer zu erkennen, wie beispielsweise [email protected] anstelle von [email protected]. Diese subtilen Änderungen können für vielbeschäftigte Mitarbeiter, die E-Mails schnell lesen und beantworten, äußerst schwer zu erkennen sein, insbesondere wenn es sich um dringende Angelegenheiten handelt. Darüber hinaus sind DMARC und SPF gegen „Close Cousins” unwirksam, da sie nur exakte Domains schützen.
Beispiele für Spear-Phishing
There is no shortage of ways to trick people into giving up sensitive data and credentials. However, there are some well-honed attacks that spear phishers turn to time and again.
- Änderungen bei der direkten Einzahlung
In einer Variante dieses Betrugs gibt sich ein Hacker als Mitarbeiter aus und sendet eine E-Mail an einen Personalassistenten, in der er darum bittet, das Bankkonto für die direkte Einzahlung des Gehalts zu ändern. In einer anderen Variante gibt sich ein Hacker als Lieferant aus und sendet eine E-Mail an einen Mitarbeiter der Buchhaltung, in der er mitteilt, dass sich das Bankkonto und die Bankleitzahl des Unternehmens geändert haben und zukünftige Zahlungen auf das neue Konto überwiesen werden sollen. - Geschenkkartenanfragen
Ein Hacker gibt sich als Führungskraft aus und fordert einen Mitarbeiter auf, mehrere Geschenkkarten zu kaufen und ihm die Codes auf der Rückseite der Karten zuzusenden. Oft gibt ein Hacker vor, in einer Besprechung oder nicht im Büro zu sein. Dies erhöht die Glaubwürdigkeit einer E-Mail, die von einer persönlichen E-Mail-Adresse wie Gmail oder Yahoo stammt. - W-2 Spear Phishing
Ein Spear-Phisher, der sich als Führungskraft ausgibt, sendet eine E-Mail an einen Mitarbeiter der Personalabteilung und fordert die W-2-Formulare der Mitarbeiter an, ein US-Steuerformular, das die Einkünfte und Steuerabzüge der Mitarbeiter ausweist. Die Steuerzeit ist für die Buchhaltungs- und Personalabteilungen besonders stressig, und der Druck sowie die zeitlichen Zwänge machen sie anfällig für Fehler, sodass sie auf diese Art von Angriff hereinfallen können. - Mehrphasige Angriffe
Mehrphasige Angriffe sind eine gängige Methode, um sich in Microsoft 365 zu hacken. Sie beginnen mit Phishing und entwickeln sich zu Spear-Phishing weiter. Ein Hacker sendet eine Phishing-E-Mail an einen Mitarbeiter und gibt sich dabei als Microsoft aus. Das Opfer gibt unwissentlich seine Anmeldedaten für Microsoft 365 auf einer Phishing-Seite preis. Mit dem Benutzernamen und dem Passwort des Opfers verschafft sich der Hacker Zugang zum Office 365-Ökosystem des Unternehmens, wo er Spear-Phishing-Angriffe mit legitimen Microsoft 365-E-Mail-Adressen startet. - Überweisungsanfragen
Diese Variante des Spear-Phishing, auch bekannt als Business Email Compromise (BEC), ist eine der kostspieligsten. Ein Hacker, der sich als leitender Angestellter ausgibt, fordert Geld in Form einer Überweisung an. In vielen hochkarätigen Fällen waren sich die Unternehmen überhaupt nicht bewusst, dass Millionen von Dollar auf betrügerische Bankkonten überwiesen worden waren.
Spear-Phishing-Techniken, auf die Sie achten sollten
Eine einmalige Spear-Phishing-E-Mail, die nur aus Text besteht, mag auf den ersten Blick wenig raffiniert wirken, aber dahinter verbergen sich Social-Engineering-Techniken, die ein hohes Maß an psychologischer Manipulation offenbaren. Nachfolgend finden Sie einige Beispiele:
- Vorwand nutzen
Spear-Phisher bereiten ihre Opfer vor, indem sie ihnen zunächst eine freundliche E-Mail senden und Small Talk betreiben, z. B. „Wie war Ihr Urlaub?“ oder „Herzlichen Glückwunsch zur Beförderung“. Dadurch wird die Wachsamkeit des Opfers verringert und es wird auf die spätere Anfrage des Spear-Phishers vorbereitet, die möglicherweise erst nach mehreren weiteren E-Mails erfolgt. - Dringende Anfragen stellen
Oft überzeugen Spear-Phisher ihre Opfer davon, dass sie nur Stunden – oder sogar Minuten – Zeit haben, um eine Überweisung zu tätigen, ihre Bankkontodaten zu ändern oder Geschenkkarten für Kunden zu kaufen. - Versenden von E-Mails über Mobilgeräte
Spear-Phisher, die sich als Führungskräfte ausgeben, behaupten oft, dass sie nicht im Büro oder sogar im Ausland sind und dringend die Hilfe des Opfers benötigen. Der Zusatz „Gesendet von meinem iPad, iPhone oder Android-Gerät“ erhöht die Glaubwürdigkeit einer solchen Behauptung und entschuldigt auch Fehler in der E-Mail, wie z. B. Tippfehler. Außerdem schafft er eine Ausrede für die Verwendung einer nicht-firmeneigenen E-Mail-Adresse wie Gmail.
(Digitale) Quellen für Spear-Phishing
Angreifer suchen häufig nach Bewertungen auf Reiseportalseiten. Online-Hotelgästebücher können einen sehr detaillierten Überblick über die finanzielle Situation einer Person geben. Auf diese Weise lassen sich schnell konkrete Rückschlüsse auf die Zusammenhänge zwischen geschäftlichen und privaten Bereichen ziehen. Allerdings handelt es sich hierbei nur um eine digitale Informationssuche.
In jedem Fall erhöhen Mitarbeiter, die personenbezogene Daten freiwillig preisgeben, das Risiko, Opfer eines Spear-Phishing-Angriffs zu werden. Denn diejenigen im Unternehmen, die sorglos mit ihren Daten umgehen, sind ideale Ziele, weshalb Spear-Phisher gezielt nach Mitarbeitern mit solchen Schwachstellen suchen.
Die unmittelbare Umgebung des Spear-Phishing-Opfers
Cyberkriminelle sind immer clever, wenn es darum geht, detailliertere Informationen zu finden. Aus diesem Grund zielen Spear-Phishing-Angriffe oft auf das unmittelbare Umfeld des potenziellen Opfers ab. Es ist nicht ungewöhnlich, dass sensible Dokumente direkt aus dem Aktenvernichter eines Unternehmens oder sogar aus der Wohnung eines Mitarbeiters abgefangen werden.
Sobald der Angreifer alle benötigten Informationen hat, führt er den Spear-Phishing-Angriff durch. In der nächsten Phase erhalten ein oder mehrere Mitarbeiter E-Mails, in denen sie aufgefordert werden, bestimmte Informationen zu bestätigen. In dieser Phase verschwimmt auch die Grenze zum CEO-Betrug, da die E-Mails in der Regel mit gefälschten Absenderadressen von Behörden versendet werden.
Anhänge, die in alltäglichen Geschäfts-E-Mails verwendet werden, dienen oft als Einfallstor. Eine Word-, Excel- oder PDF-Datei kann der Schlüssel zum gesamten Unternehmensnetzwerk sein. Die meisten Menschen, die diese Anhänge öffnen, sind sich der potenziellen Gefahr nicht bewusst.
Der Köder bei einem Spear-Phishing-Angriff
Das Design und die Tarnung des Köders sind entscheidende Elemente, um das Ziel einer Spear-Phishing-Attacke zu täuschen. Je überzeugender ein Angreifer den Köder tarnt, desto größer ist die Wahrscheinlichkeit eines Erfolgs.
Während Spear-Phishing-Attacken in der Vergangenheit oft auf E-Mails beschränkt waren, liegt der Fokus heute zunehmend auf sozialen Medien. Auch hier kann es vorkommen, dass Mitarbeiter eines Unternehmens unwissentlich auf persönlicher Ebene mit Spear-Phishern interagieren, was dazu führt, dass das Opfer direkt mit dem Angreifer kommuniziert. Auch dies ist eine Gelegenheit, die Opfer auszuspionieren.
Professionelle Spear-Phishing-Angriffe sind schwer zu erkennen. Der Inhalt ist in der Regel so zielgerichtet, dass er für Laien nur sehr schwer zu erkennen ist. Hier unterscheidet sich Spear-Phishing vom normalen Phishing, bei dem unzählige E-Mails wahllos in einer sogenannten „Schrotflinten-Taktik” verschickt werden.
Wie können sich Unternehmen vor Spear-Phishing-Angriffen schützen?
Spear-Phishing-Angriffe stellen eine besondere Herausforderung für IT-Sicherheitsbeauftragte in Unternehmen dar. Schließlich ist der einzelne Mitarbeiter die zentrale Schwachstelle. Links und Dateianhänge werden leichtfertig geöffnet, ohne den tatsächlichen Absender zu erkennen.
Das Gleiche gilt für falsche Freundschaftsanfragen, die über soziale Netzwerke eingehen. Die Psyche des Empfängers wird als Einfallstor genutzt, um seine angeborene Skepsis zu umgehen. Da diese Methode so effektiv ist, nimmt die Zahl der Spear-Phishing-Angriffe von Jahr zu Jahr zu. Daher ist es äußerst wichtig, über die Gefahren von Spear-Phishing aufzuklären und das Bewusstsein dafür zu schärfen.
Spear-Phishing-Angriffe aufdecken
Um sich vor Spear-Phishing zu schützen, sollten E-Mail-Benachrichtigungen, in denen die Angabe sensibler Daten verlangt wird, ignoriert werden.
Weder ein Finanzinstitut noch ein Dienstleister würde seine Kunden jemals auffordern, persönliche Daten per E-Mail preiszugeben.
Das Gleiche gilt für fragwürdige Nachrichten oder vermeintlich harmlose Links von angeblichen Bekannten aus sozialen Netzwerken – insbesondere für kryptische Adressen oder URLs. Beachten Sie jedoch, dass auch Links, die vertrauenswürdig erscheinen, problematisch sein können.
Verwenden Sie soziale Medien mit Vorsicht
Vielleicht haben Sie schon einmal einen Beitrag auf Twitter oder Facebook gesehen, der personenbezogene Daten enthielt. Es gibt die seltsamsten Fälle – von der Veröffentlichung eines Führerscheins bis hin zur Offenlegung eines Kontoauszugs ist alles dabei. Sogar Leute, die ihre Kreditkarten präsentieren! Solche Leute laden geradezu zu Spear-Phishing-Angriffen ein.
Unter bestimmten Umständen können Daten auch mithilfe von Bildaufnahmen abgegriffen werden. Dies gilt insbesondere dann, wenn sensible Dokumente auf einem Schreibtisch liegen und als Foto in den sozialen Medien landen. Solche Fälle sind meist darauf zurückzuführen, dass ein Mitarbeiter unbedacht ein Bild seines Arbeitsplatzes veröffentlicht. Dieses Szenario ist in der Praxis häufig anzutreffen.
Verwendung herkömmlicher E-Mail-Sicherheit
Reputation
Die reputationsbasierte Bedrohungserkennung blockiert bekannte, bösartige E-Mail-Absender (IP-Adressen) und Phishing-URLs. Ein reputationsbasierter Filter blockiert bekannte bösartige Absender, lässt jedoch neue Bedrohungen unberücksichtigt.
Sichere E-Mail-Gateways (SEG)
Sichere E-Mail-Gateways (SEG) basieren auf Reputations- und signaturbasierter Erkennung. Ein SEG befindet sich außerhalb der Microsoft 365-Architektur, wodurch Exchange Online Protection (EOP) deaktiviert wird und Microsoft 365 ungeschützt gegen Insider-Angriffe bleibt.
Unterschriften (Fingerabdruck)
Die signaturbasierte Bedrohungserkennung blockiert Bedrohungen mit einer bekannten „Signatur“, wie beispielsweise Malware-Code.
Sandboxing
Sandboxing sendet verdächtige E-Mails zur Analyse an eine kontrollierte Umgebung. Es ist unwirksam gegen Spear-Phishing-E-Mails, die keine Anhänge oder Links enthalten.
Verteidigen Sie sich vorausschauend
Bei der prädiktiven Verteidigung arbeiten künstliche Intelligenz (KI), einschließlich einer Kombination aus überwachten und unüberwachten maschinellen Lernmodellen, zusammen, um die verräterischen und schwer zu erkennenden Anzeichen von Spear-Phishing zu identifizieren:
Überwachtes Lernen
Algorithmen werden mit bösartigen und legitimen E-Mails trainiert, um bestimmte Merkmale von Spear-Phishing-E-Mails zu erkennen, wie beispielsweise mobile Signaturen und E-Mail-Adressen aus öffentlichen Domänen.
Unüberwachtes Lernen
Natürliche Sprachverarbeitung und unbeaufsichtigte Anomalieerkennung erkennen missbräuchliche Muster in Spear-Phishing-E-Mails, darunter Dringlichkeit, Schlüsselwörter und E-Mail-Adressen, die nicht mit den Absendern im Unternehmensmodell übereinstimmen.
Unterschriften (Fingerabdruck)
Die signaturbasierte Bedrohungserkennung blockiert Bedrohungen mit einer bekannten „Signatur“, wie beispielsweise Malware-Code.
Benutzer-Feedback-Schleifen
Benutzer melden Spear-Phishing-E-Mails an das Security Operations Team (SOC), das die E-Mail analysiert und die Algorithmen verbessert.
Schützen Sie Ihr Unternehmen mit 365 Total Protection
Hornetsecurity für M365 blockiert komplexe Angriffe bereits bei der ersten E-Mail dank maschineller Lernmodelle, die eine Echtzeit-Verhaltensanalyse der gesamten Phishing-E-Mail durchführen, einschließlich aller URLs und Anhänge. Unsere KI-basierte Bedrohungserkennung stoppt Bedrohungen vor, während und sogar nach Phishing-Angriffen.
Mehr über HORNETSECURITYS SERVICES
Interessiert an verwandten Themen?
Hat Ihnen unser Beitrag zum Thema Spear Phishing gefallen? Dann könnten Sie auch andere Artikel in unserer Wissensdatenbank interessieren! Wir helfen Ihnen dabei, mehr über Cybersicherheitsthemen wie Emotet, Trojaner, IT-Sicherheit, Cryptolocker-Ransomware, Phishing, Cyber Kill Chain und Computerwürmer zu erfahren.



