What Is a Cyber Attack?

In many cases, hacking attacks are made possible due to human errors or vulnerabilities in software systems. An example of such an error is the recent discovery by security company Vectra about Microsoft Teams. According to Vectra, Microsoft Teams stored authentication tokens in unencrypted plaintext mode. This flaw could potentially allow attackers to gain control over communications within an organization.
IT security is a crucial factor to protect your infrastructure from cyber attacks.
What Is a Cyber Attack?

What Happens During a Cyber Attack
What Happens During a Cyber Attack
Malware attacks
Back in the days when we used to discuss cybersecurity attacks, we would often mention viruses, spyware, trojans, backdoors, and so on. These are all distinct types of malware that aim to gain unauthorized access to systems, hardware, and data to infect them.
In the year 2000, the ILOVEYOU worm, rapidly infects millions of Windows machines shortly after its release, spreading quickly like wildfire. The ILOVEYOU worm was not the first-ever malware attack developed, but it is one that remains memorable to many.
Did it start with ILOVEYOU worm? It didn’t. Malicious people began creating scripts that could alter program behavior long before the advent of the ILOVEYOU worm, with the first program.
There are different types of malware attacks, including viruses, worms, Trojans, ransomware, spyware, adware, botnets, keyloggers, rootkits, and backdoors. Ransomware is one of the most popular and destructive malware. You can read more details here What is ransomware? How can you protect against Ransomware?
According to our research, 20% of all reported Ransomware Attacks occurred in the last year, the survey finds. Find our takeaways in our article Ransomware Attacks Survey 2022.
There are different ways to protect your machines, including running antivirus software with real-time protection, host-based firewalls, a fully patched operating system, and secure hardware and applications.
One of the most important aspects in addition to these measures is security awareness training for employees or end users. Read more here Forgetting Curve according to Dr Ebbinghaus: Why cyber awareness training is an ongoing process.
We cover you with 7 reasons why security awareness is critical for employees. You can read more here 7 Reasons Why Security Awareness Is Critical for Employees.
Phishing Attacks
Phishing attacks are one of the most common types of attacks that we receive on a daily basis via email. These are the emails that ask you to verify your Facebook or LinkedIn account, change your banking credentials, and others.
One of the common ways to deliver a phishing attack is via email. However, they can also be delivered via SMS, voice, website, spear, and other methods.
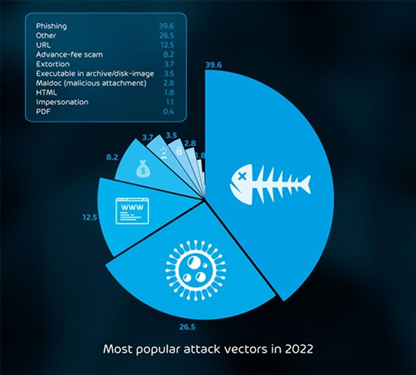
According to our Cyber Security Report 2023, phishing ranked the number one email attack technique, at 39.6% of detected attacks.
You can prevent this kind of attack by educating your employees about what to open and what not to open. Additionally, having phishing detection tools is a must-have.
Did you hear about QR code phishing? We did write and article and produced video to give you insight what QS scam is and how to stay protected. You can read it here All You Need to Know About QR Code Scams.
If you would like to explore more about phishing, read it here Phishing – The danger of malicious phishing mails.
Distributed Denial of Service (DDoS)

Man-in-the-Middle (MitM)
Password attacks
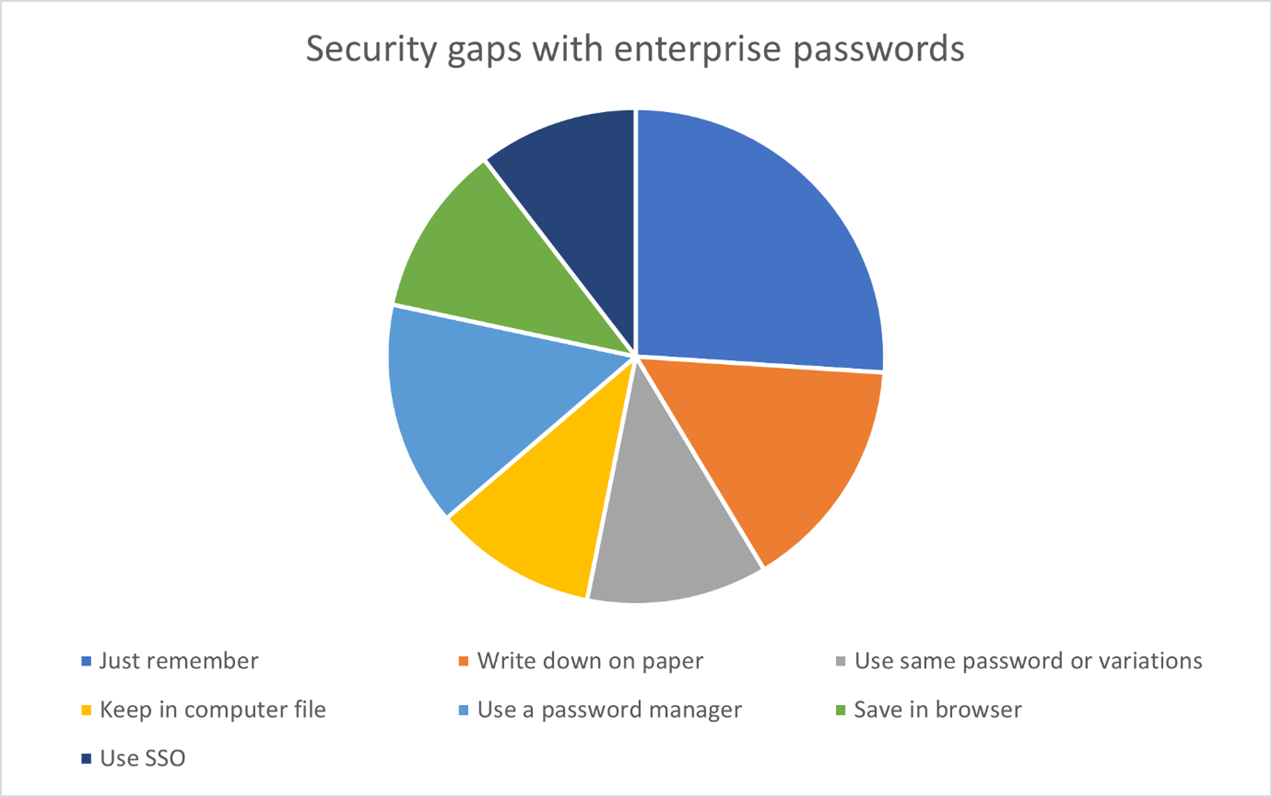
- 93% of the passwords used in brute force attacks include 8 or more characters.
- 54% of organizations do not have a tool to manage work passwords.
- 68% of passwords used in real attacks include at least two-character types.
- 48% of organizations do not have user verification in place for calls to the IT service desk.
- 42% of seasonal passwords contained the word “summer”.
SQL Injection
DNS Spoofing
Cross-Site Scripting (XSS)
Zero-Day Exploits
Social Engineering
Other Types of Cyber Attacks
Before we call it a day
To properly protect your cyber environment, use Hornetsecurity Security Awareness Service and Advanced Threat Protection to secure your critical data.
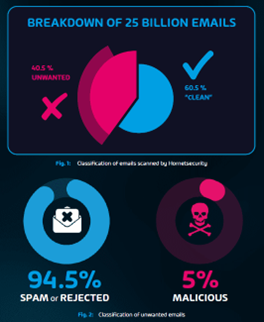
We work hard perpetually to give our customers confidence in their Spam & Malware Protection, Email Encryption, and Email Archiving strategies.
To keep up to date with the latest articles and practices, pay a visit to our Hornetsecurity blog now.