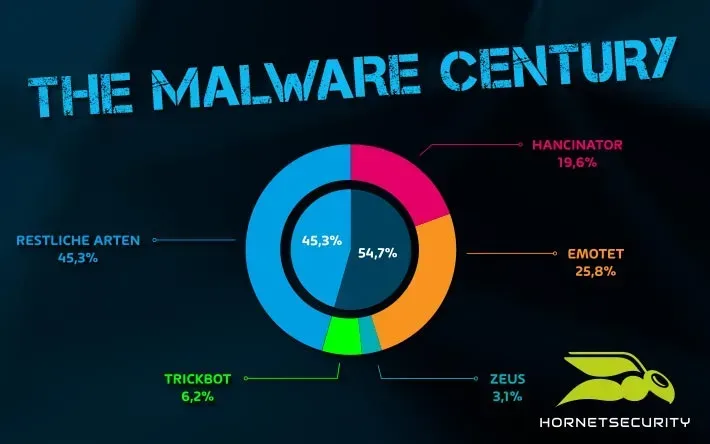
Emotet
WAS IST EMOTET? UND WIE KANN ICH MICH SCHÜTZEN?
Maßnahmen zum Schutz vor der gefährlichsten Schadsoftware der Welt
WAS IST EMOTET?
Ist Emotet ein Virus? Nein. Das erste Mal tauchte Emotet als Banking-Trojaner im Jahr 2014 auf. Die Attacke zielte darauf ab, Online-Zugangsdaten von deutschen und österreichischen Bankkunden abzufangen. Mittlerweile kann Emotet jedoch eine Vielzahl weiterer Module mit anderen Schadfunktionen nachladen und ausführen. Emotet schlägt vor allem mittels Spam-E-Mail zu und trifft sowohl private Anwender als auch Unternehmen, Krankenhäuser, staatliche Einrichtungen und Kritische Infrastrukturen.
Dabei werden Methoden hochprofessioneller Advanced Persistent Threat-Angriffe adaptiert und automatisiert. Cyberkriminelle gehen sehr zielgerichtet und mit großem Aufwand vor, um möglichst lange im befallenen System handlungsfähig zu bleiben. Es ist deshalb nicht leicht, Emotet zu entfernen.
Ein Aspekt macht Emotet besonders gefährlich: Seit Ende 2018 ist die Malware in der Lage mittels sogenanntem Outlook-Harvesting die Kontaktbeziehungen und E-Mail-Inhalte aus den Postfächern infizierter Systeme auszulesen, um auf dieser Basis weitere Angriffe zu starten. Die Verbreitung erfolgt dadurch besonders schnell. Weitere Empfänger erhalten dann ebenso authentisch wirkende E-Mails von Personen, mit denen sie erst kürzlich im Kontakt standen. Schadhafte Dateianhänge oder in der Nachricht enthaltende URLs werden unbedacht geöffnet.
Neben diesem Spam-Modul kann Emotet auch ein Wurm-Modul laden, mit dem es sich selbstständig im Firmennetzwerk verbreitet. So kann es sich auf weiteren Rechnern einnisten, ohne dass Nutzer einen Anhang anklicken und aktivieren müssen. In diesem Rahmen unternimmt Emotet auch Brute-Force-Angriffe mit dem Ziel Passwörter zu knacken. Dies kann schwerwiegende Konsequenzen haben. Ist der Computer erst infiziert, lädt Emotet je nach Ziel weitere Schadsoftware über C&C Server nach. Es drohen Datendiebstahl, Kontrollverlust über Systeme, der Ausfall der kompletten IT-Infrastruktur und Einschränkungen von kritischen Geschäftsprozessen. In Extremfällen müssen ganze Unternehmensnetzwerke nach einer Infektion neu aufgebaut werden. Die Schäden liegen oft in Millionenhöhe.
EMOTET INFEKTIONSKETTE
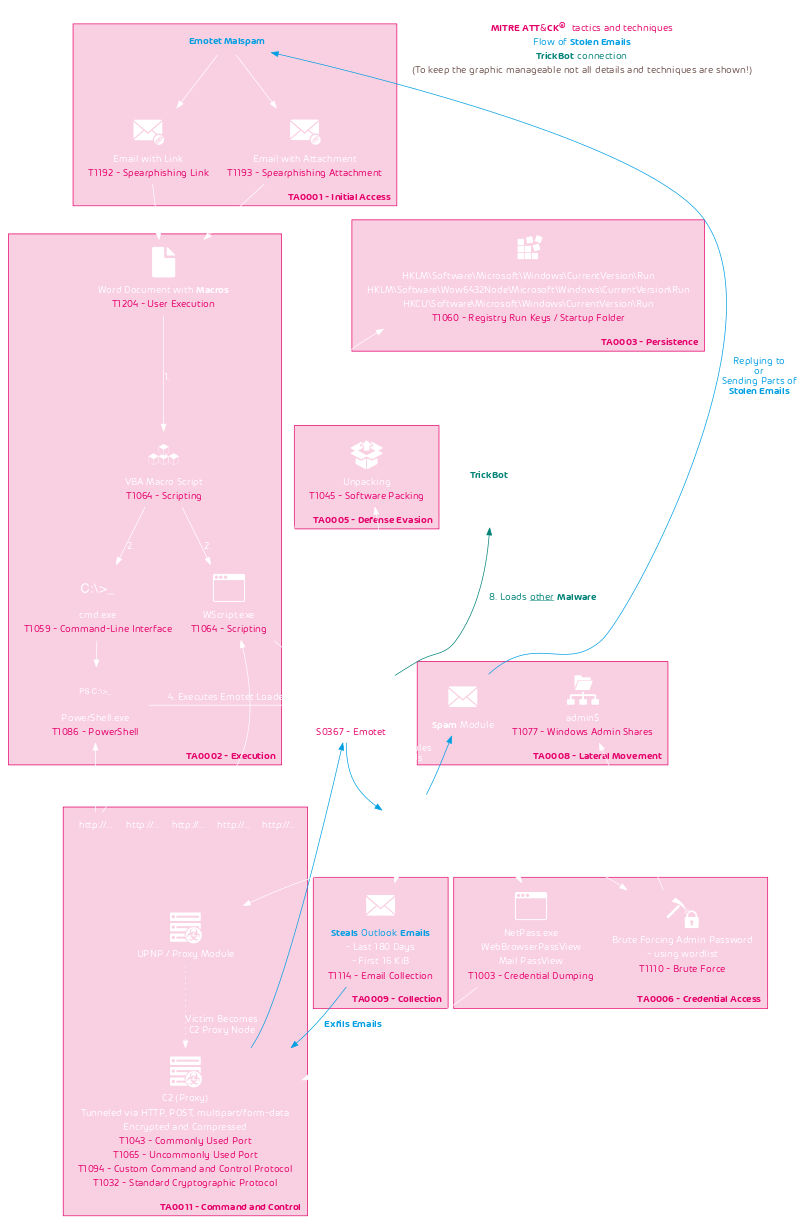
Zumindest der anfängliche Teil der Emotet-Infektionskette und die angewandten Taktiken und Techniken, wie sie im MITRE ATT&CK Framework definiert sind, werden im folgenden Flussdiagramm dargestellt:
Hervorzuheben ist, dass Emotet E-Mails von Opfern stiehlt und sie als Vorlagen für neuen Malspam verwendet. Es nutzt das sogenannte Email-Thread-Hijacking, bei dem es auf alte E-Mail-Konversationen mit einer schädlichen E-Mail antwortet. Die Wahrscheinlichkeit ist groß, dass E-Mails von bekannten Gesprächspartnern in bestehenden Konversationen geöffnet werden. Infolgedessen sind die Distributionskampagnen von Emotet sehr erfolgreich. Diese Art von Angriffen ist einer der Hauptgründe dafür, warum IT-Sicherheitsverantwortliche in Security-Awareness-Trainings investieren müssen, um ein Bewusstsein für diese Gefahr zu schaffen.
Emotet ist außerdem so gefährlich, weil es zusätzlich zu seinen eigenen Modulen zum Diebstahl von E-Mails und zum Missbrauch von Computern, als C2- und Spam-Server auch andere Malware wie TrickBot ausliefert, was letztlich zu einer Infektion mit der Ransomware Ryuk führen kann. Selbst wenn man versucht die Emotet-Infektion zu bereinigen, kann bereits zusätzliche Malware auf dem System laufen.
Wenn ein System mit Emotet infiziert wird, wird es Teil des Emotet Botnet.
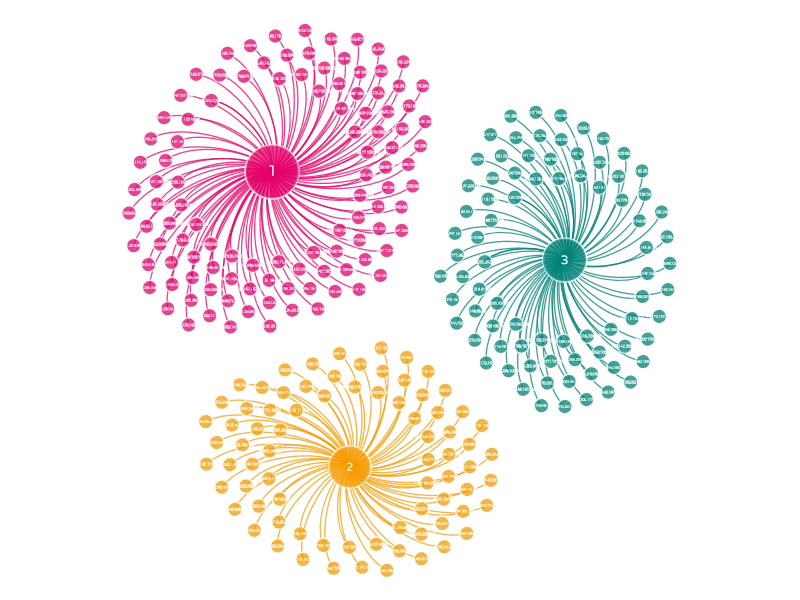
EMOTET BOTNET
Das Emotet Botnet ist in mehrere Botnets aufgeteilt. Forscher nannten sie Epoche 1 und 2, weil sie Payload Updates zu unterschiedlichen Zeiten erhielten. Jede Epoche hat ihren eigenen einzigartigen RSA-Schlüssel, der für die C2-Kommunikation verwendet wird. Am 17.09.2019 wurde ein Teil des Epoche 1 Botnets in das Epoche 3 Botnet abgespalten.
Jedes Botnet verbindet sich mit den C2-Servern seiner Epoche. Wenn ein Empfänger durch ein Emotet-Dokument infiziert wird, das zu Epoche 1 gehört, lädt das Dokument den Emotet Loader von der Epoche 1-Infrastruktur herunter und wird anschließend Teil von Epoche 1.
Die aktuelle Struktur des Tier-1-C2-Servers des Emotet Botnets sieht folgendermaßen aus:
Änderungen werden zuerst im E2-Botnet implementiert. Es ist möglich, dass dies als Test durchgeführt wurde, um sicherzustellen, dass im Falle von eingeführten Änderungen, die nicht funktionieren, nur ein Teil des gesamten Botnets verloren geht.
MEISTER DER TARNUNG: WARUM EMOTET SO SCHWIERIG ZU BEKÄMPFEN IST
Emotet ist nicht einfach zu identifizieren und abzufangen, da es herkömmliche Antivirenprodukte täuscht: Als polymorpher Virus verändert sich der Code bei jedem neuen Abruf leicht, um der Erkennung durch signaturbasierte Virenscanner zu entgehen. Darüber hinaus erkennt der Virus, wenn er in einer virtuellen Maschine ausgeführt wird. Sobald eine Sandkastenumgebung registriert wird, fällt das Programm in eine Art Stand-By-Modus und führt in diesem Moment keine schadhaften Aktionen aus.
Emotet, TrickBot und die Ransomware Ryuk
Wie bereits erwähnt, lädt Emotet nach einer erfolgreichen Infektion weitere Schadprogramme nach. Eine besonders gefährliche Allianz entsteht im Zusammenspiel mit TrickBot und Ryuk: Getarnt in einem Word-Dokument dringt Emotet beim Ausführen der Datei in ein Unternehmensnetzwerk ein und kundschaftet dieses aus. Als „Türöffner“ lädt er den Banking-Trojaner TrickBot nach, der unter anderem Kontozugangsdaten kopiert. Diese Information gibt er an die Ransomware Ryuk weiter, die schließlich als letztes nachgeladen wird. Ryuk verschlüsselt nun alle im System befindlichen Dateien, die TrickBot und Emotet zuvor als sensibel bzw. wichtig eingestuft haben.
WIE KANN MAN SICH VOR EMOTET SCHÜTZEN
Um sich effektiv vor Emotet zu schützen, muss man sich vor allem auf das Haupteinfallstor des Schadprogramms konzentrieren: Der E-Mail-Kommunikation. Hornetsecurity Advanced Threat Protection erkennt in E-Mails Emotet und Ryuk mühelos und stellt beide Malware-Programme unter Quarantäne. Bereits in der ersten Analyse-Instanz wird der Emotet-Trojaner identifiziert. Die nachgelagerten Trojaner Ryuk und TrickBot können mithilfe der dynamischen Verhaltensanalyse in der ATP Sandbox entlarvt werden. E-Mails, die die perfiden Schadprogramme enthalten, werden den Empfängern nicht zugestellt.
Des Weiteren gilt es grundlegende, sicherheitsrelevante Verhaltensweisen zu beachten:
- Da sich Emotet häufig in Microsoft Office-Dateien versteckt und Makros benötigt, um Schadprogramme installieren zu können, ist es sinnvoll diese nicht zuzulassen. Im privaten sowie in den meisten geschäftlichen Bereichen werden diese auch nicht benötigt. Sollte dennoch nicht darauf verzichtet werden können, ist es möglich nur signierte Makros zu erlauben.
- Bereitgestellte Sicherheitsupdates müssen umgehend für Betriebssysteme, Antivren-Programme, Web-Browser, E-Mail-Clients und Office-Programme installiert werden.
- Regelmäßige Daten-Backups sind empfehlenswert.
- Wachsamkeit ist oberstes Gebot: Auch bei vermeintlich bekannten Absendern sollte man bei Dateianhängen von E-Mails, insbesondere bei Office-Dokumenten und enthaltenen Links, vorsichtig sein. Im Zweifelsfalle ist es ratsam bei einer verdächtigen E-Mail den direkten Kontakt zum Absender zu suchen und die Glaubhaftigkeit des Inhaltes zu überprüfen.
- Zugriffe im unternehmenseigenen Netzwerk sollten kontinuierlich überwacht werden, denn so kann rechtzeitig festgestellt werden, ob eine Emotet-Infektion stattgefunden hat.
Steigende Bedrohung durch Ransomware
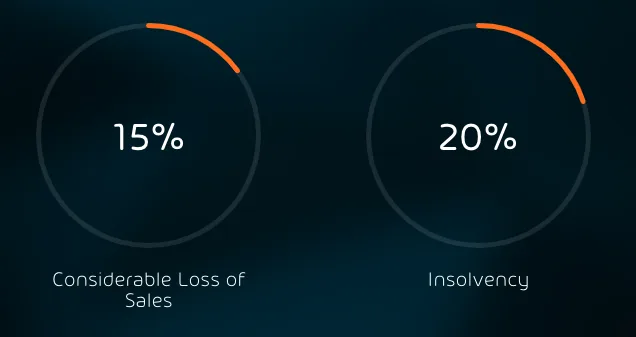
Ransomware gehört zu den beliebtesten cyberkriminellen Methoden, um große Gewinne einzufahren aber auch um immense (finanzielle) Schäden bei den Opfern anzurichten. Gelangt die Erpressersoftware ins System eines Unternehmens, werden sämtliche sensible und unternehmensvertrauliche Dateien verschlüsselt und nur gegen ein Lösegeld in Form von Bitcoins wieder freigegeben. Ob nach einer Zahlung eine Freigabe der Dateien tatsächlich erfolgt ist jedoch nicht immer klar.
Begehrte Ziele für Hacker sind vor allem große Unternehmen und staatliche Einrichtungen sowie Kritische Infrastrukturen. Im schlimmsten Fall droht nach einem Angriff die Insolvenz. Aber auch erhebliche Umsatzeinbußen gehören zu den möglichen Auswirkungen.
VIDEO: SO ZERLEGT EMOTET EIN UNTERNEHMEN
MEHR ZU EMOTET
Alle Infos zusammengefasst
Das Infopaper fasst die Empfehlungen der Hornetsecurity Experten rund um das Thema Emotet anschaulich zusammen. Jetzt herunterladen und herausfinden, was Emotet ist, was genau die Schadsoftware so gefährlich macht und wie sich Nutzer vor Emotet schützen können.
Mehr zum Thema Emotet
Mehr Informationen zu Emotet sind in den Blogbeiträgen Der unheimliche Pakt zwischen Emotet, TrickBot und der Ransomware Ryuk und Emotet: Comeback im neuen Gewand zu finden. Als zuverlässigen Schutz vor Emotet empfiehlt Hornetsecurity Advanced Threat Protection.
Mehr über HORNETSECURITYS SERVICES
Interessiert an verwandten Themen?
Hat Ihnen unser Beitrag zum Thema Phishing gefallen? Dann könnten Sie auch andere Artikel in unserer Wissensdatenbank interessieren! Wir helfen Ihnen dabei, mehr über Cybersicherheitsthemen wie Emotet, Trojaner, IT-Sicherheit, Cryptolocker-Ransomware, Phishing, Cyber Kill Chain und Computerwürmer zu erfahren.