

Social Engineering
Wie Hacker ohne Programmierkenntnisse
Mittels Social Engineering an Daten gelangen
„Es gibt heute keine Technologie, die nicht durch Social Engineering überwunden werden kann.“ (Kevin Mitnick, ehemaliger Hacker & Experte im Bereich Social Engineering)
Selbst mit den besten technischen Sicherheitsvorkehrungen besteht in jedem Unternehmen ein Risikofaktor, der nur schwer kontrolliert werden kann: der Mensch.
Um Zugriff auf wichtige Daten oder Zugänge zu erhalten, muss ein Hacker nicht nur Computer verstehen, sondern den Menschen an sich.
Was genau ist Social Engineering und wie kann man sich davor schützen? Im folgenden Beitrag klären wir die wichtigsten Fragen dazu.
Inhaltsverzeichnis
Was ist Social Engineering?
Beim Social Engineering geht es um die zwischenmenschliche Beeinflussung einer Person. Dabei versucht der Hacker das Vertrauen des Opfers zu gewinnen und ihn so zum Beispiel zur Preisgabe von vertraulichen Informationen oder zur Freigabe von Kreditkartendaten und Passwörtern zu bewegen.
Social Engineering findet nicht nur im Internet statt, sondern ist eine Betrugsmasche, die schon seit vielen Jahrzenten genutzt wird. Eine der bekanntesten Maschen ist der Enkel-Trick, bei der Trickbetrüger über einen Telefonanruf ältere Menschen davon überzeugen, dass sie ein Verwandter seien und dringend Geld benötigen (Polizeiliche Kriminalprävention, 2017).
Auch auf Online-Partnerbörsen wird Social Engineering von Kriminellen immer wieder angewandt, um sich finanziell zu bereichern. Eine vermeintlich junge, attraktive Frau kontaktiert einen Mann, der offensichtlich auf der Suche nach einer neuen Partnerin ist. Der Betrüger spielt seine Rolle als verliebte Single-Frau so gut, dass das Vertrauen des Opfers nach einem relativ kurzen Zeitraum gewonnen wird. Beispielsweise für eine Reise zum „neuen Partner“, bittet der Kriminelle schließlich um die finanzielle Unterstützung durch das Opfer. Danach wird der Kontakt häufig abgebrochen.
Social Engineering Attacken auf Unternehmen
Wenn der Social Hack im privaten Umfeld funktioniert, dann sind Unternehmen das nächst höhere Ziel für Kriminelle – vor allem weil hier oftmals höhere Geldbeträge zu erbeuten sind. Das Vorgehen der Hacker verläuft ähnlich wie bei Privatpersonen, wobei das Einholen der nötigen Informationen für einen professionellen Angriff beim Social Engineering wesentlich mehr Zeit in Anspruch nimmt. So sind hauptsächlich folgende Angaben für Cyberkriminelle relevant:
- Wer ist der Chef (CEO) des Unternehmens und welche Personen befinden sich in Führungspositionen?
- Wer ist befugt Überweisungen zu tätigen?
- Wann ist der Chef im Urlaub oder auf Geschäftsreise?
- Welche geschäftlichen Aktivitäten finden derzeit statt?
Mit einer gefälschten E-Mail-Adresse, ähnlich der des Vorgesetzten, wendet sich der Hacker mit dringenden Worten zumeist an einen Mitarbeiter, der befugt ist finanzielle Transaktionen durchzuführen.
Social Engineering Beispiele:
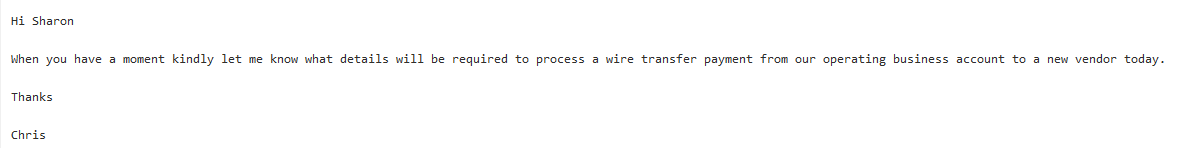
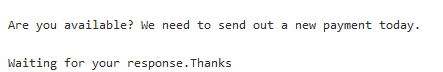
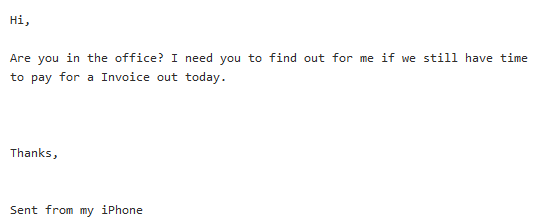
Durch die mutmaßliche Dringlichkeit des Anliegens befindet sich der Empfänger der E-Mail nun in der Situation, dem Auftrag des Vorgesetzten zügig nachzukommen, ohne eventuell große Rückfragen zu stellen. Sind die Daten erst einmal übermittelt, macht sich der Cyberkriminelle direkt ans Werk oder die Überweisung geht direkt auf das Konto der „Social-Hacker“. Große Unternehmen wie der österreichische Luftfahrtzulieferer FACC und der Nürnberger Kabelhersteller Leoni machten 2016 finanziell schwerwiegende Erfahrungen mit der Vorgehensweise des Social Engineerings und mussten einen Verlust von mehreren Millionen Euro erleiden.
Aber Achtung, denn nicht nur Personen aus der Buchhaltung und Geschäftsführer sind gefährdet:
„Hey, hier ist Felix aus der IT-Abteilung. Mir sind bei deinem Account in unserem System ein paar Unregelmäßigkeiten aufgefallen, kannst du mir einmal deine Zugangsdaten geben, damit ich das einmal überprüfen kann?
Gruß Felix“
Wie würden Sie auf solch eine Nachricht reagieren? Würden Sie antworten? Sie kennen zwar nicht alle IT-Mitarbeiter, aber Felix ist scheinbar ein Kollege und möchte Ihnen helfen, die Sicherheit der internen IT zu gewährleisten.
Insbesondere in großen Unternehmen kennen die Mehrzahl der Mitarbeiter nicht alle IT-Mitarbeiter. Wer solch einer E-Mail vertraut, ermöglicht den Diebstahl sensibler Daten und gefährdet neben der IT-Sicherheit auch viele weitere Bereiche eines Unternehmens immens.
Der Ursprung des Social Engineerings
Eine weniger aufwendige Art des Social Engineerings ist die klassische Phishing E-Mail. Meist handelt es sich dabei um gefälschte PayPal E-Mails mit hinterlegtem Link zu einer nachgebildeten Website, der Originalen so ähnlich, dass ein Betrug kaum auffällt. In der E-Mail wird darum gebeten, auf dieser Website seine Login-Informationen zu aktualisieren oder Zugangsdaten zu verifizieren. Jedoch gelangen die Daten so direkt in die Hände der Betrüger.
Anstelle einer persönlichen E-Mail sind diese Nachrichten sehr generisch. Hintergrund der klassischen Phishing E-Mail ist das einfache und weniger aufwendige Verfahren. So werden ganze Massen an E-Mails versendet. Selbst wenn nur ein Bruchteil der Empfänger auf den Trick hereinfällt, hat sich die Social Engineering Attacke für den Hacker gelohnt.
Hier können Sie alles wichtige über Phishing-Angriffe erfahren.
Social Engineering erfordert keine Programmierkenntnisse
Allein durch das Anwenden psychologischer Tricks werden technische Hürden überwunden. Der Hacker nutzt den Menschen als das schwächste Glied der IT-Sicherheits-Kette. Selbst der sicherste Tresor der Welt kann geöffnet werden, wenn die Zugangsdaten an unbefugte Personen weitergegeben werden. So spart sich der Kriminelle einen großen technischen Aufwand und das Risiko durch die IT-Sicherheitsvorkehrungen entdeckt zu werden.
Wenn Sie auf die obige E-Mail von Felix geantwortet hätten, wäre der Hacker innerhalb von wenigen Minuten in das Unternehmensnetzwerk eingedrungen. Ohne Aufwand, ohne Programmierkenntnisse, ohne großes Risiko. Kriminelle nutzen das Grundvertrauen und die Neugier der Mitarbeiter, um Daten oder Geld stehlen zu können.
Schutz vor Social Engineering: wie schütze ich mein Unternehmen?
Organisieren Sie regelmäßig präventive Schulungen, in denen Sie sich und Ihre Mitarbeiter für die Gefahren durch gefälschte E-Mails sensibilisieren. Ebenso können reguläre Info E-Mails helfen Aufmerksamkeit für das Thema zu schaffen.
Solange der Kriminelle sich keinen Zugang zum E-Mail Account eines Mitarbeiters oder des Geschäftsführers verschafft hat, gibt es verschiedene Möglichkeiten gefälschte E-Mails zu erkennen:
- Absender-Adresse prüfen: Prüfen Sie die Absender-Adresse sorgfältig. Ist die E-Mail-Adresse wirklich korrekt? Wurden vielleicht Buchstaben vertauscht? Oder ein kleines L mit einem großen I vertauscht? Häufig steht hinter der E-Mail-Adresse noch eine weitere, automatisch generierte und nicht nachvollziehbare. Sollten Sie misstrauisch gegenüber einer E-Mail sein, können Sie sich den Header genauer ansehen. Im Header einer E-Mail stehen alle Informationen, wie der tatsächliche Absender und der Server, von dem die Nachricht versendet wurde. In den meisten Fällen ist der Absender das eindeutigste Kriterium, an dem eine Fraud Attacke erkannt werden kann.
- Persönlich nachfragen: Kontaktieren Sie Ihre Kollegen persönlich, wenn Sie sich unsicher sind. Rufen Sie an oder sprechen Sie Face-to-Face mit der entsprechenden Person.
- Rhetorik: Gerade bei CEO-Fraud Attacken ist es wichtig, sich nicht einschüchtern zu lassen. Hinterfragen Sie, ob der Chef wirklich ohne das Wissen Anderer 20.000 € auf ein unbekanntes Konto überweisen will. Oder überlegen Sie sich, ob der IT-Kollege Felix tatsächlich „ungewöhnliche Aktivitäten“ feststellen konnte und warum er dazu überhaupt Ihre Zugänge benötigt. Auch als Privatperson hilft ein kurzer Anruf beim Support des Unternehmens, bei dem Sie Kunde sind, sollte eine erhaltene E-Mail bei Ihnen für Verwunderung sorgen.
- Auf Rechtschreibfehler achten: Gerade in Phishing E-Mails finden sich viele Rechtschreibfehler. Angefangen bei der falschen Schreibweise des Namens, bis hin zu einer unsauberen Sprache, die darauf schließen lässt, dass der Text nicht von einem Muttersprachler verfasst, sondern beispielsweise von einem automatischen Sprachprogramm übersetzt wurde.
- Nicht direkt auf Links klicken: Sollte Sie der Inhalt einer E-Mail verunsichern, klicken Sie am besten nicht auf einen Link in der E-Mail, sondern rufen Sie die jeweilige Website direkt über den Browser auf. Fordert Sie beispielsweise Amazon auf Ihre Daten zu aktualisieren, gehen Sie am besten direkt auf Amazon.com und suchen dort nach einer entsprechenden Meldung. Ist dort nichts zu finden, handelt es sich wahrscheinlich um eine Phishing E-Mail.
- Über einen Link hovern: Bevor Sie einen Link öffnen, gehen Sie mit der Maus über den Link. In den meisten Browsern wird unten links ein kleines Fenster geöffnet. Dies ist die URL, die mit einem Klick auf den Link aufgerufen wird. Eine Kontrolle der URL gibt Aufschluss über das tatsächliche Ziel der angezeigten Web-Adresse.
Phishing Quiz von Google: Der kostenlose Awareness-Check
Vor wenigen Wochen hat Google auf das starke Wachstum von Phishing Angriffen mit einem Security Quiz reagiert. In diesem Quiz müssen Sie versuchen eine Phishing E-Mail zu erkennen. Durchschauen Sie jeden Social Engineering Angriff? Finden Sie es hier heraus.
Zusätzlicher Schutz mit Advanced Threat Protection von Hornetsecurity
Klassische Phishing E-Mails werden in aller Regel von einem guten Spamfilter erkannt und direkt aussortiert. Ein personalisierter Social Engineering Angriff unterscheidet sich aber nicht groß von einer ganz normalen E-Mail. So landen, trotz Spamfilter, die ungewollten E-Mails im eigenen Postfach.
Advanced Threat Protection geht einen Schritt weiter: Verschiedene tiefgreifende Filter und heuristische Erkennungsmechanismen enttarnen fast jede gefälschte E-Mail. Mit der Unterstützung von AI lernt der Filter mit jedem Angriff dazu und steigert so täglich seine Erkennungsrate. Advanced Threat Protection übernimmt viele der oben genannten Punkte vollständig automatisiert.
Am Ende gilt aber immer, jede E-Mail zu hinterfragen und bei der Weitergabe von Daten mit Bedacht vorzugehen.
Mehr über HORNETSECURITYS SERVICES
Interessiert an verwandten Themen?
Hat Ihnen unser Beitrag zum Thema DDoS-Angriffe gefallen? Dann könnten Sie auch andere Artikel in unserer Wissensdatenbank interessieren! Wir helfen Ihnen dabei, mehr über Cybersicherheitsthemen wie Emotet, Trojaner, IT-Sicherheit, Cryptolocker-Ransomware, Phishing, Cyber Kill Chain und Computerwürmer zu erfahren.


