What Is a Sandbox Environment? Exploring Their Definition and Range of Applications
The Purpose of a Sandbox
Sandbox is a controlled and isolated environment where security professionals analyze, observe, and execute suspicious or potentially malicious software, files, or code without harming their actual systems. Think of it as a digital quarantine zone for testing and assessing the behavior of unknown or untrusted programs.
Sandboxes are essential for looking into and finding malware, infections, and other online cyber threats, which then security teams have the freedom to examine the malware’s operations meticulously, ascertain its primary goal, and develop effective countermeasures to safeguard their environment after observing these potential threats, their interactions with the system, and their behavioral trends in a controlled virtual environment.
Below, we will explore how to utilize a sandbox in your environment, including its perks, functionality, limitations, and its role in safeguarding against cyber-attacks.
How Does a Sandbox Work?
Sandboxing is a critical cybersecurity technique that IT professionals often rely on. Untrusted code is isolated within a secure environment using techniques like virtualization or process separation, later executed and observed by monitoring its interactions with certain processes or files.
No matter how a sandbox is utilized, every environment runs on the same feature, isolation. Sandboxing involves isolating the code or application being tested or analyzed from the rest of the system. This isolation is achieved through various means, including:
Process Isolation
Virtualization
User Permissions
Browser Sandboxes
How to Create a Sandbox Environment
To choose the right sandbox environment, consider your purpose (malware analysis, testing, or browsing), operating system compatibility, isolation level needed, ease of use, and performance impact.
Security features, community support, and tool compatibility are crucial. Factor in resource requirements, costs (for commercial solutions), customization options, update frequency, and user feedback. Make a decision that aligns with your specific goals, ensuring it meets your needs while balancing security and usability.
Testing and experimenting with different sandboxes can help you find the best fit for your requirements.
Again, the specific steps to create a sandbox may vary depending on your needs and the tools available, but here are some general guidelines:
Choose a Sandbox Type
Software Sandboxes
These are virtualized environments that can be set up using software tools. Popular options include VirtualBox, VMware, Docker, and Kubernetes.
Hardware Sandboxes
These are physical devices or systems dedicated to sandboxing. They can be used for more stringent isolation but are often more resource-intensive.
Select the Purpose
Install Operating Systems
Isolate the Sandbox
Examples of Using a Sandbox Environment
Antivirus sandbox
Antivirus sandbox is used to assess suspicious files for possible threats. The antivirus program separates a file from the main system when a user downloads it and sets it in the sandbox.
In this controlled environment, the file is run while the antivirus software monitors it and searches for malicious behavior, including changing system files or establishing unwanted network connections.
Additionally, the sandbox checks the file’s signature against a database of known threats, where, based on these tests, the antivirus determines the file’s safety or malicious intent, protecting the user’s machine against infection.
Virtual machine (VM)
Setting up a Virtual machine (VM) as a sandbox turns a host computer into an isolated, virtual environment.
By emulating hardware components such as the CPU and storage, it establishes a safe environment for the execution of malicious files or untrusted applications and data. A VM sandbox may, for instance, open phishing mail attachments. The sandboxed program runs independently of the host system within the virtual machine.
This enables secure observation and analysis of its actions. The host cannot be affected, even if the attachment turns out to be malicious.
VM backup in a sandbox provides a safety net for recovery and rollback, and if a file in your sandbox becomes corrupted or causes harm to your system, you can quickly restore it to a previous state using the backup.
This cuts down on downtime and guarantees that testing and development may continue without being significantly interrupted.
Link verification
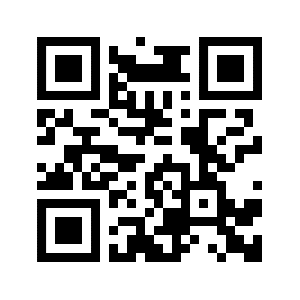
Link verification, QR code scams can point to URLs, and a sandbox can be used to verify the integrity of the destination website. It can assess whether the linked website contains known phishing or scam indicators, helping users avoid interacting with malicious sites.
Benefits of Using a Sandbox Environment
Sandboxing has several advantages, including:
Threat identification and analysis
Zero-day protection
Network traffic analysis
Malware analysis
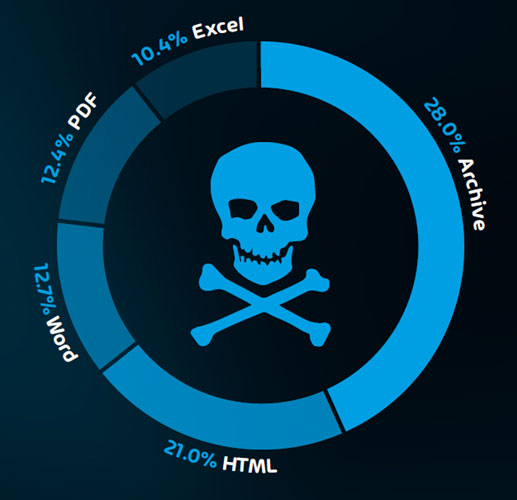
Sandboxing gives security researchers a secure, isolated environment to execute and examine malware samples, characterize their traits, and observe their behavior.
User and data protection
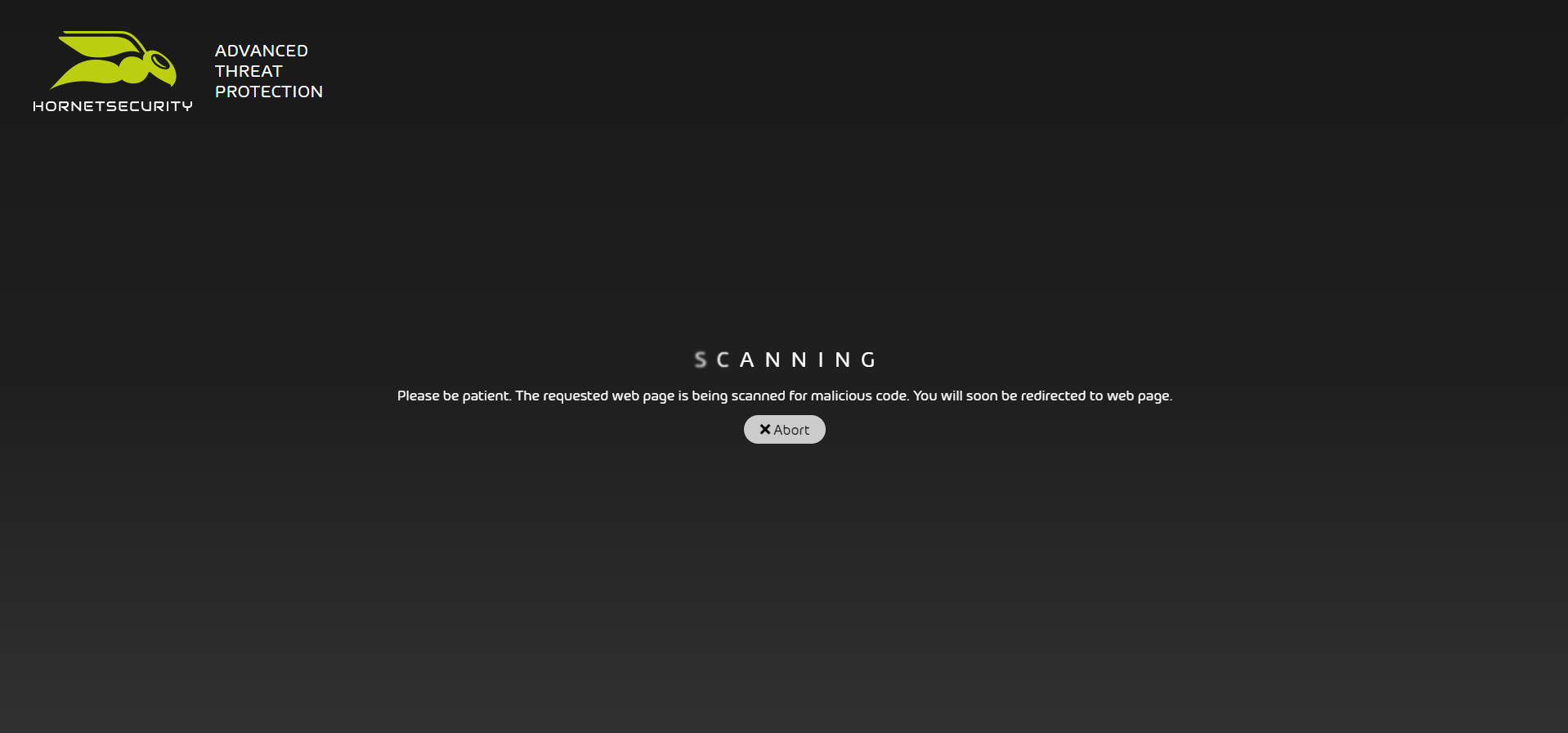
By preventing malicious code from executing on user devices or servers, sandboxing helps protect sensitive data and user privacy, for example, by receiving email files for analysis before the recipient can open it
Organizations must take into account the following sandboxing obstacles:
False positives: Sandboxing may produce false positives when harmless files or programs are mistakenly classified as harmful.
Resource requirements: The amount of processing power, memory, and storage needed for sandbox environments is large, which can have an effect on performance and scalability.
To properly protect your cyber environment and minimize the risk it is important to educate your employees with Security Awareness Service, and Advanced Threat Protection to secure your critical data.
To keep up to date with the latest articles and practices, pay a visit to our Hornetsecurity blog now.
Conclusion
In today’s digital world, every click, every share and every bite of data we transmit tells a good story about us. People trust this world, often more than they should, secrets, memories, finances – their very lives – into it.
And yet many are oblivious to the fragility of this trust, where the lines between right or wrong often blur. Mitigating those risks by employing a safe, controlled sandbox environment to detect, prevent and analyze the online threats is only a fraction of the security controls that organizations need to employ.
FAQ
What is a sandbox environment in development?
A sandbox environment in development is a controlled and isolated space where software developers can test, experiment, and deploy applications without affecting the production environment. By isolating development and testing from production systems, resources are used more efficiently, and downtime is minimized.
What is the difference between a sandbox and a test environment?
A sandbox is an isolated space for experimentation and small-scale testing, often with simplified data, while a test environment replicates the production setup closely for comprehensive testing. Sandboxes are for development, learning and helping with safe analyzing potential threats, whereas test environments ensure software reliability and accuracy before deployment in production.
What is the difference between a virtual environment and a sandbox?
Sandbox and virtual environment share similar characteristics to make them easily confused.
Technically virtual environment can act like a safe isolated space for the execution of bad code, whereas a sandbox environment is a controlled area for testing, experimentation, and security isolation. While both provide isolation, they serve different purposes, with virtual environments focusing on dependency management and sandboxes on broader software testing and security.