FULL SUITE FOR MICROSOFT 365: SECURITY, RISK, GOVERNANCE, COMPLIANCE & BACKUP
REQUEST YOUR FREE TRIAL!
FUTURE-PROOF YOUR BUSINESS OPerations with ai-powered m365 security, data protection, compliance & SECURITY AWARENESS.

Your choice for a secure, compliant, and controlled M365.
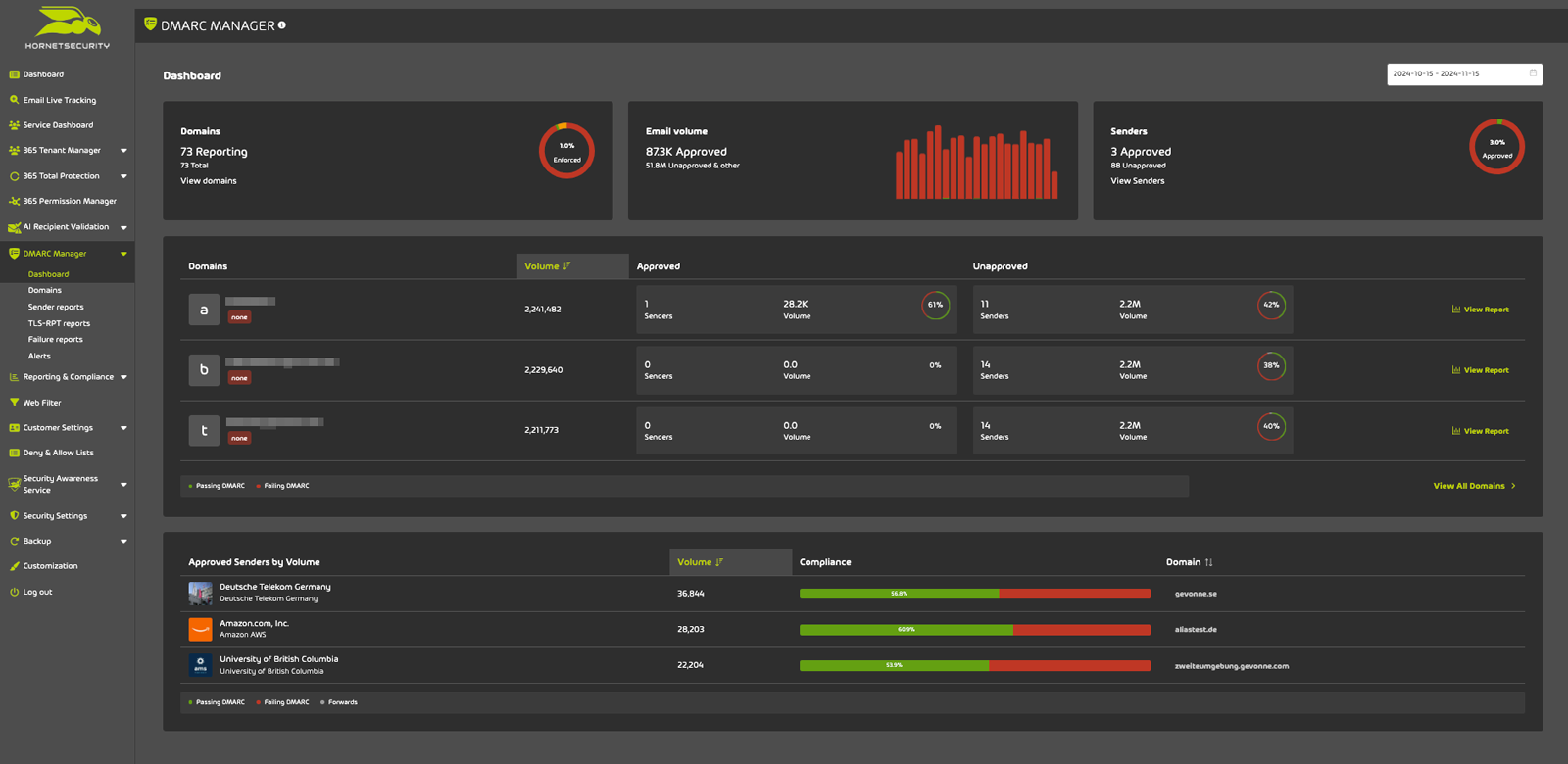
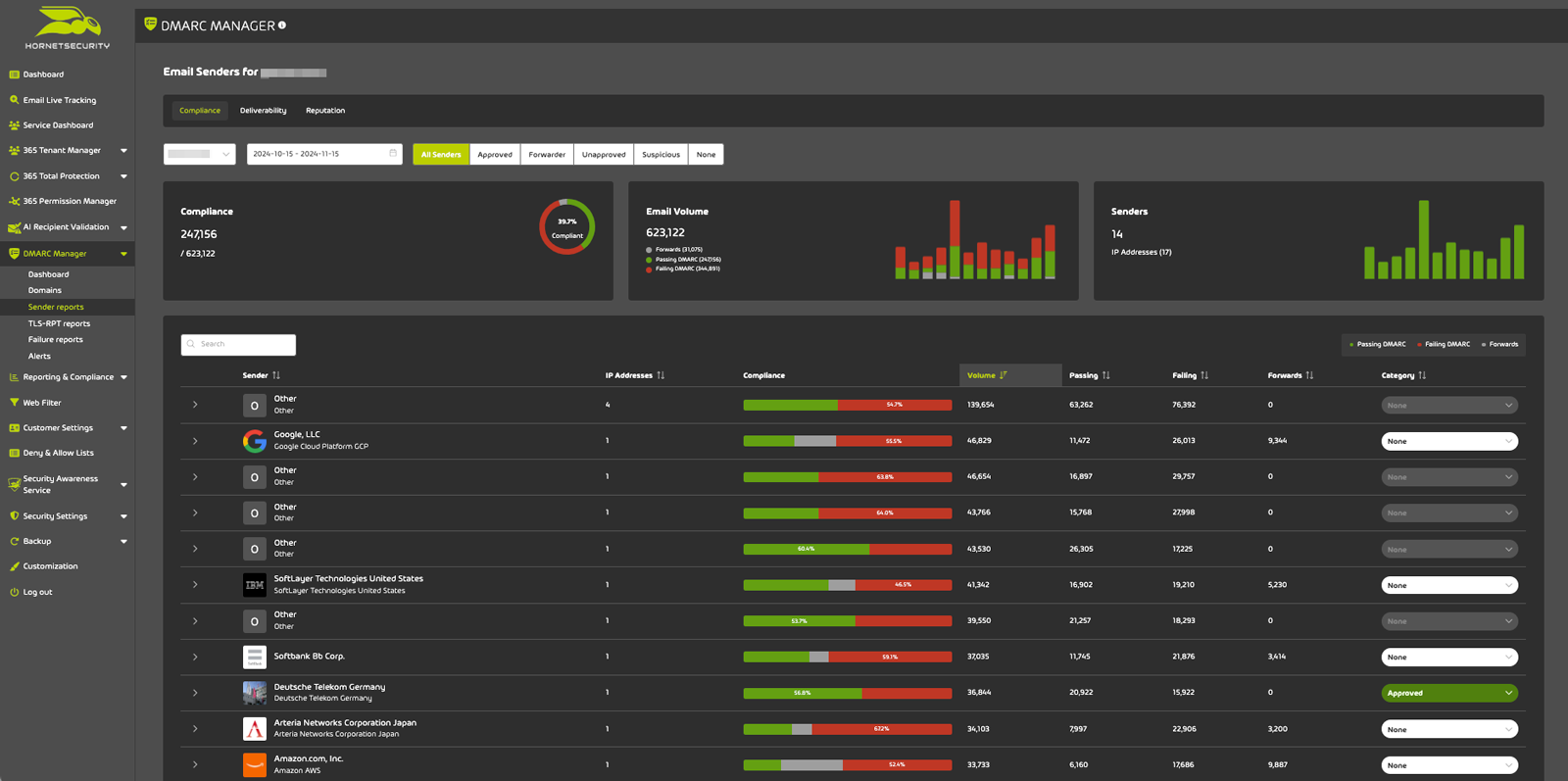
All in one package: email security, backup, security awareness, access & permission control and domain fraud protection.
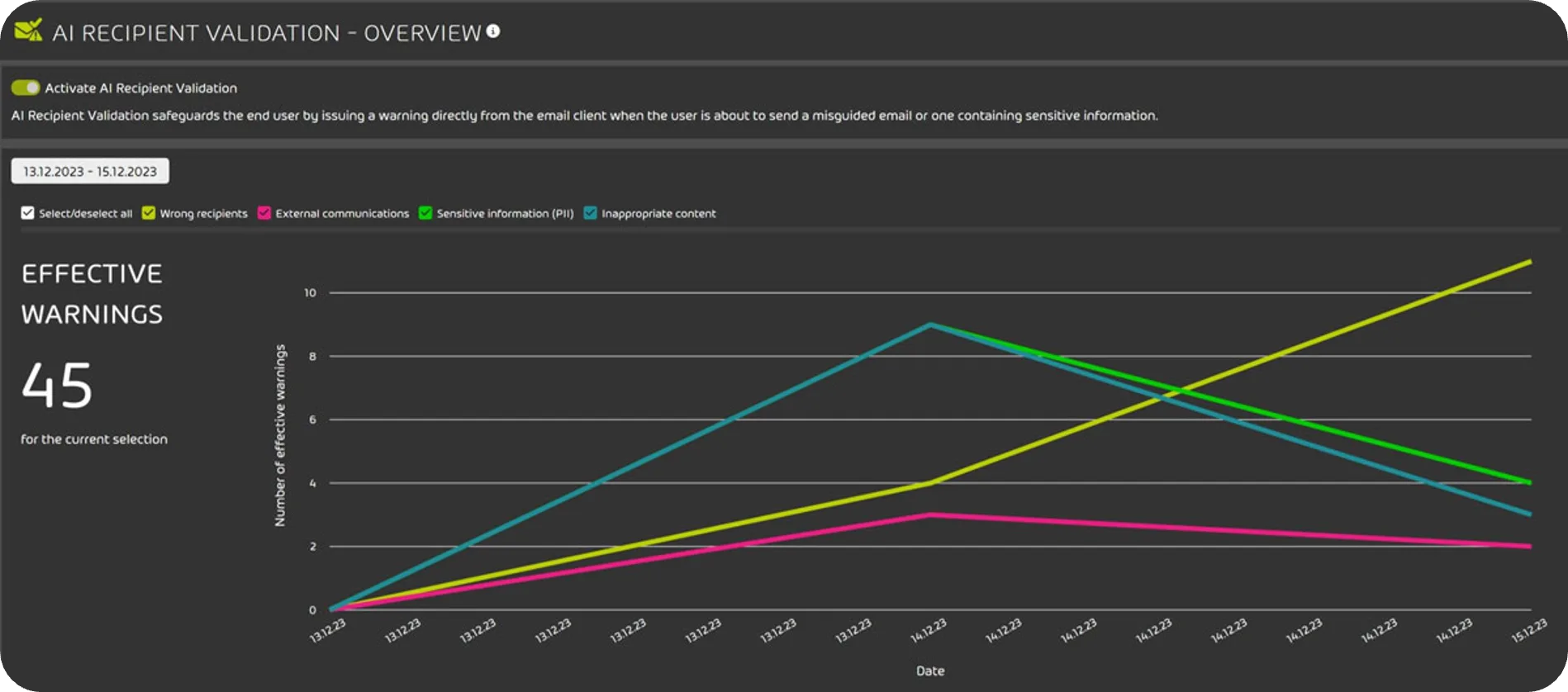
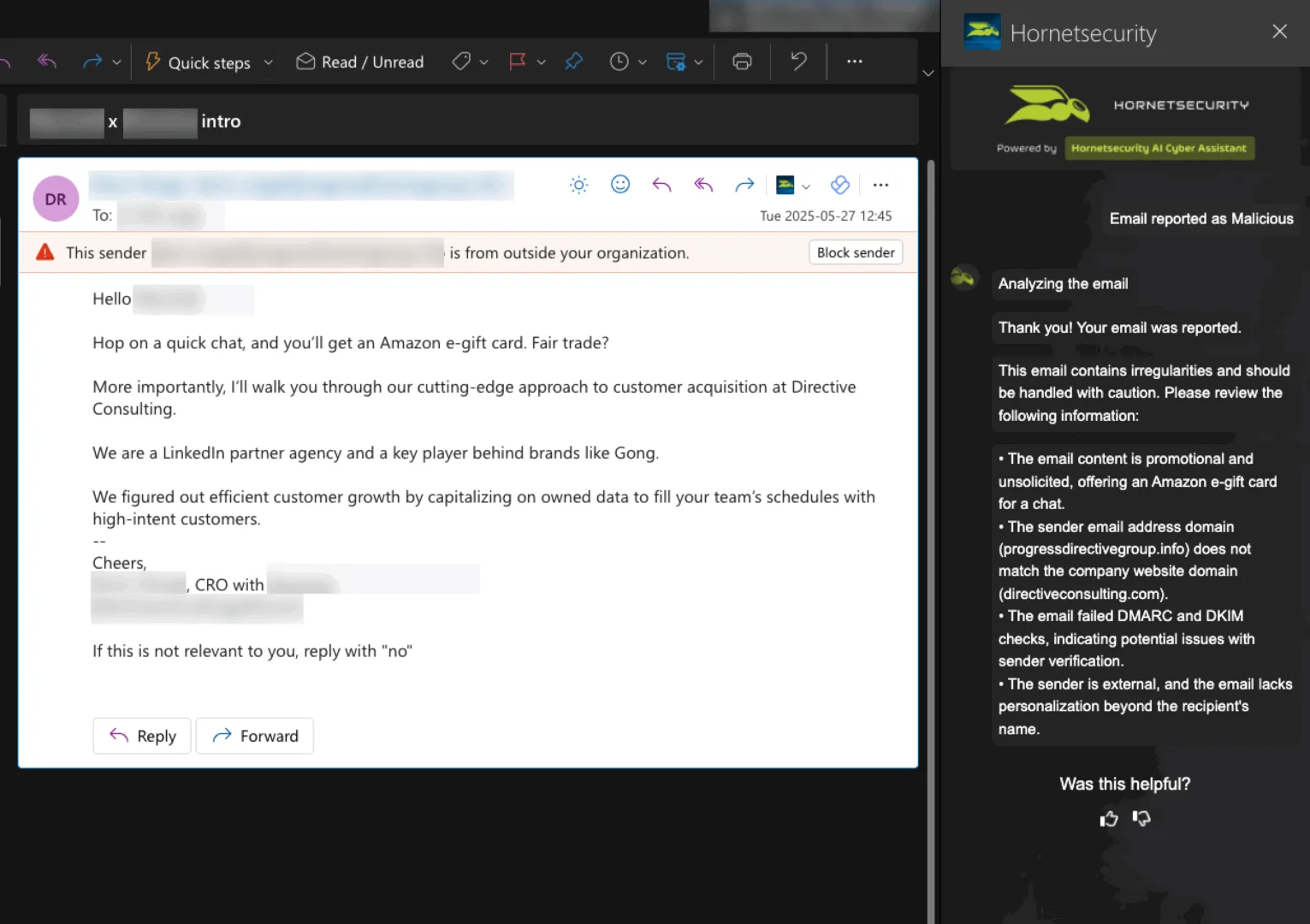
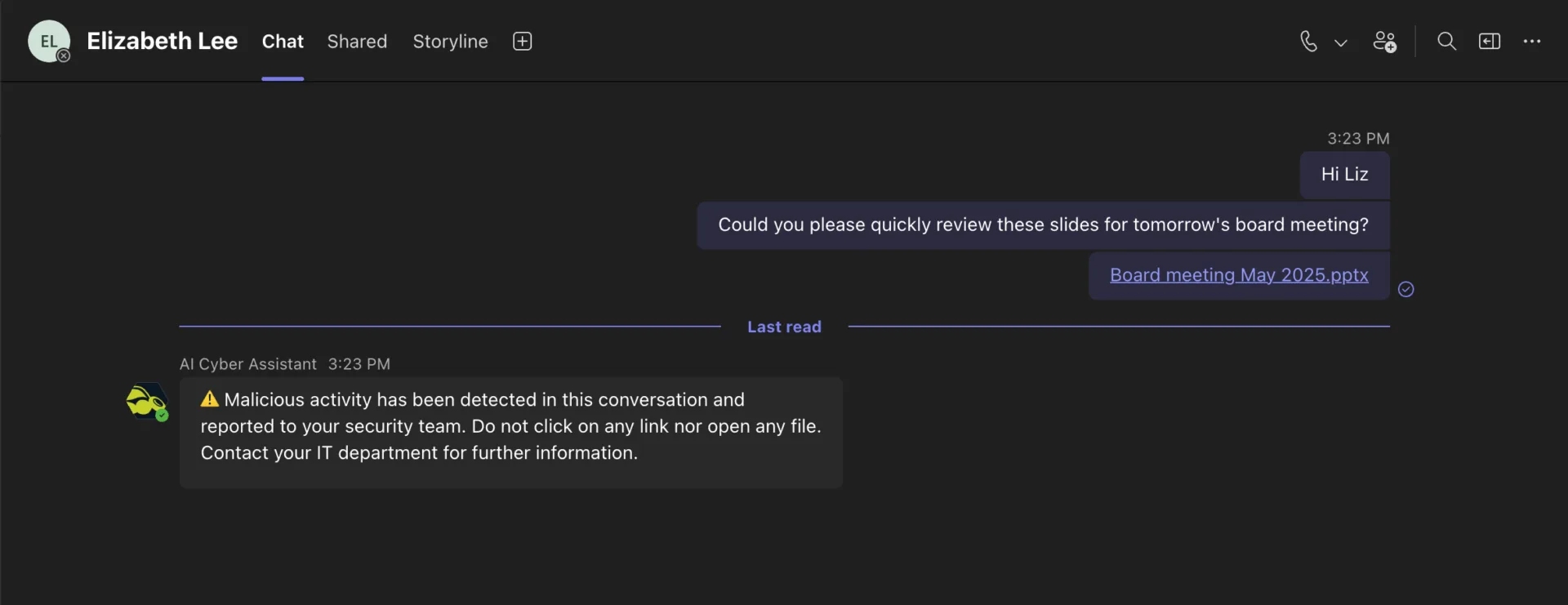
Benefit from our AI Cyber Assistant-powered trio for even stronger security and greater awareness: AI Recipient Validation, Teams Protection, and AI Email Security Analyst.
LEARN HOW YOU CAN BENEFIT
Dive into our resources to learn more about how you can benefit, and discover the best ways to protect your business.
FREE DOWNLOADS
For more product details, take a look at our Fact Sheets.
365 Total Protection >
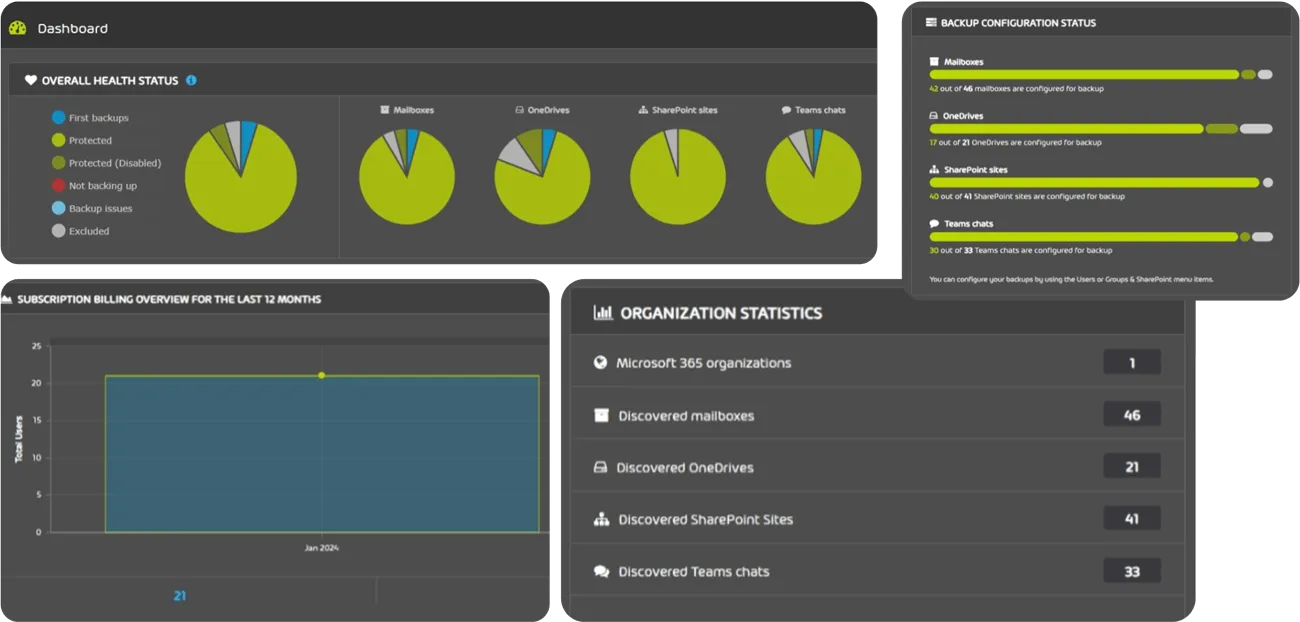
365 Total Backup >
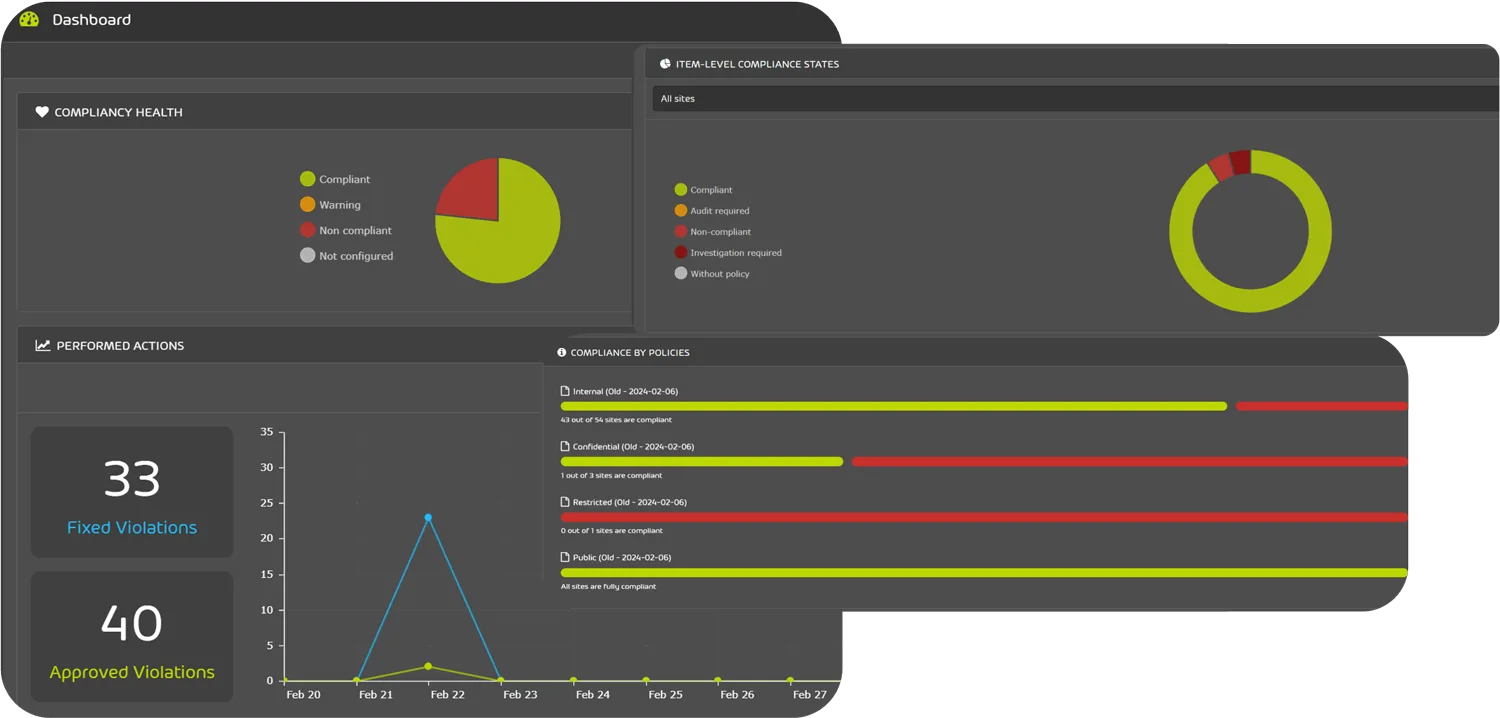
365 Permission Manager >
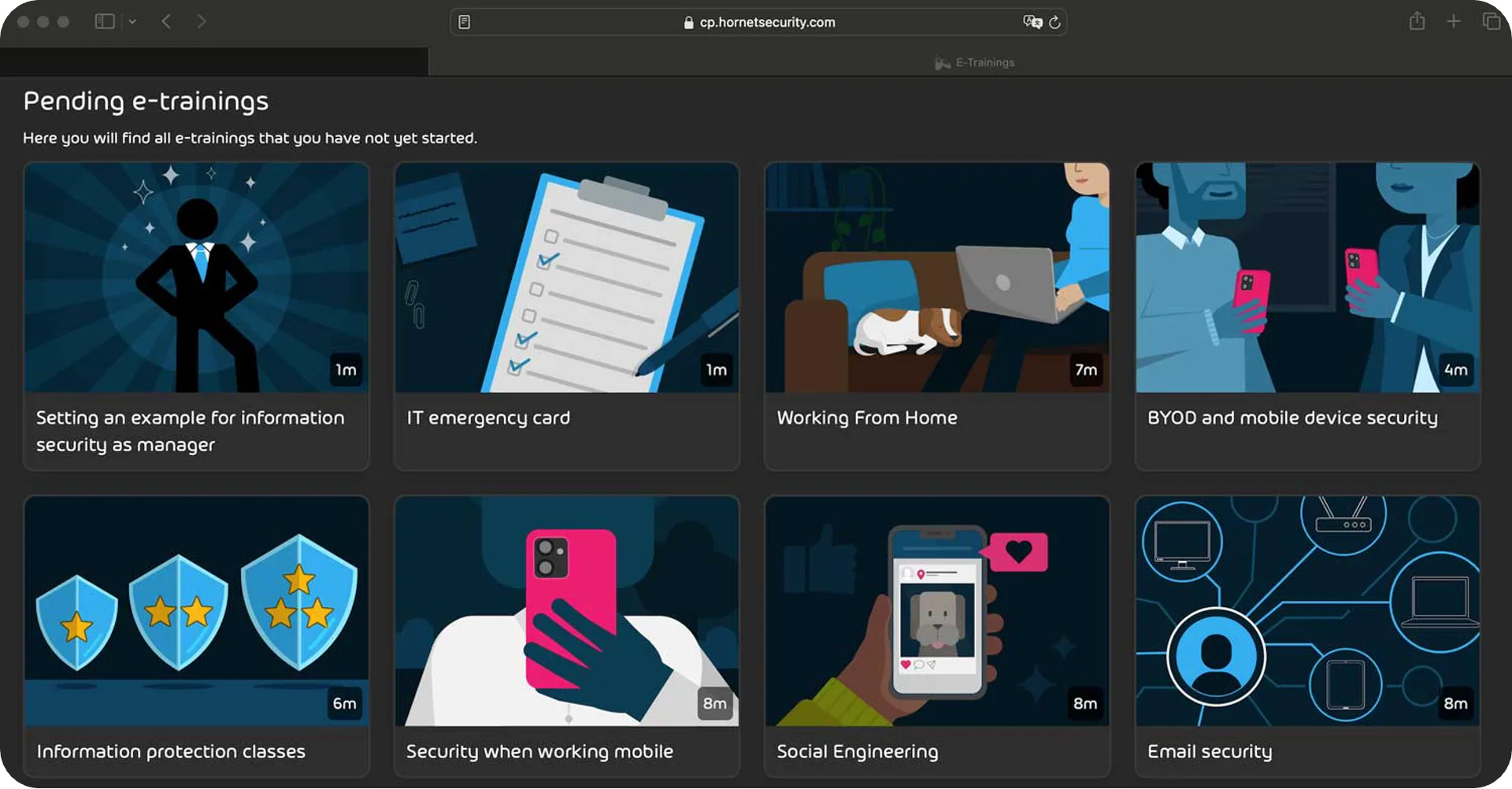
Security Awareness Service >
EDUCATIONAL CONTENT
We have some well-researched content pieces for you! Watch our webinars, read our ebooks and listen to our podcast!