Join the cyber defense all-stars!
Face off against cyber threats with the ultimate defender for your Microsoft 365 environment. Try our Permission Manager free trial – because in the game of cybersecurity, you’re the MVP!
Pour le français, cliquez ici
Ready to dominate the cyber arena? Join the Hornetsecurity League.
Just like a skilled hockey player navigates the rink, our Microsoft 365 Permission Manager glides through the complexities of permission management. It’s time to take control of your data, ensuring only the right players get access.
Power Play Features:
Impeccable Defence
Guard your data like a goalie protecting the net. Permission Manager ensures only authorized players make it past the blue line.
Effortless Control
Maneuver through permissions with ease. Our user-friendly interface lets you call the shots, making permission management a breeze.
Penalty Box
Send cyber threats to the penalty box. Permission Manager blocks unauthorized access, keeping your digital playing field secure.
Cloud-based Control Centre
Manage permissions from anywhere, just like a coach strategizing from the sidelines.
Real-time Alerts
Get instant alerts for any suspicious activity, ensuring you’re always one step ahead of the opposing team. Just like Don Cherry, Hornetsecurity ensures that you’re notified of every assist.
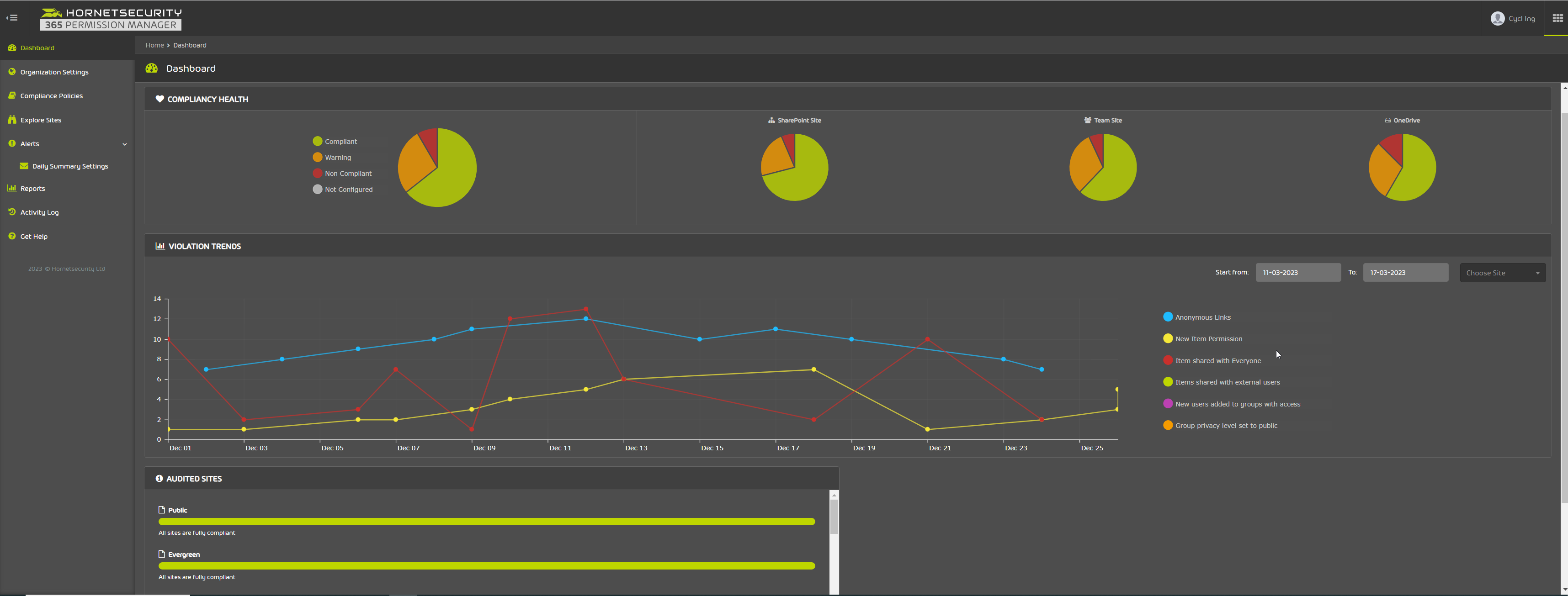
Champion Your Compliance
Win at compliance with easy-to-use tools. Permission Manager keeps your organization in top form, meeting regulations effortlessly.
Ready to dominate the cyber arena? Join the Hornetsecurity League.
The Permission Manager play-by-play
The Permission Manager Advantages
Simplify Managing Permissions at Scale
Get a full overview and understanding of your organization’s M365 permissions across SharePoint, OneDrive, and Microsoft Teams. Use advanced filtering to quickly check which items are accessible by anonymous external users or guests, or which have broken permissions. Break down nested groups to get a transparent view of users’ effective access rights.
Take Back Control with Compliance Policies
Use our GRC service if you need to maintain a compliant SharePoint, Teams, and OneDrive data infrastructure and prevent users from sharing sensitive information. With 365 Permission Manager, you can either assign out-of-the-box best practice policies or create custom compliance policies for SharePoint sites, Teams or OneDrive accounts. If a user shares a site or a file against your compliance policy, site owners receive immediate notification about the violation so they can intervene.
Receive Alerts for Critical Shares
Receive a daily summary of critical permission changes happening across your M365 tenant. Alerts will notify you which sites, files, and folders have newly shared items with “Everyone” or anonymous users or guests outside your organization.
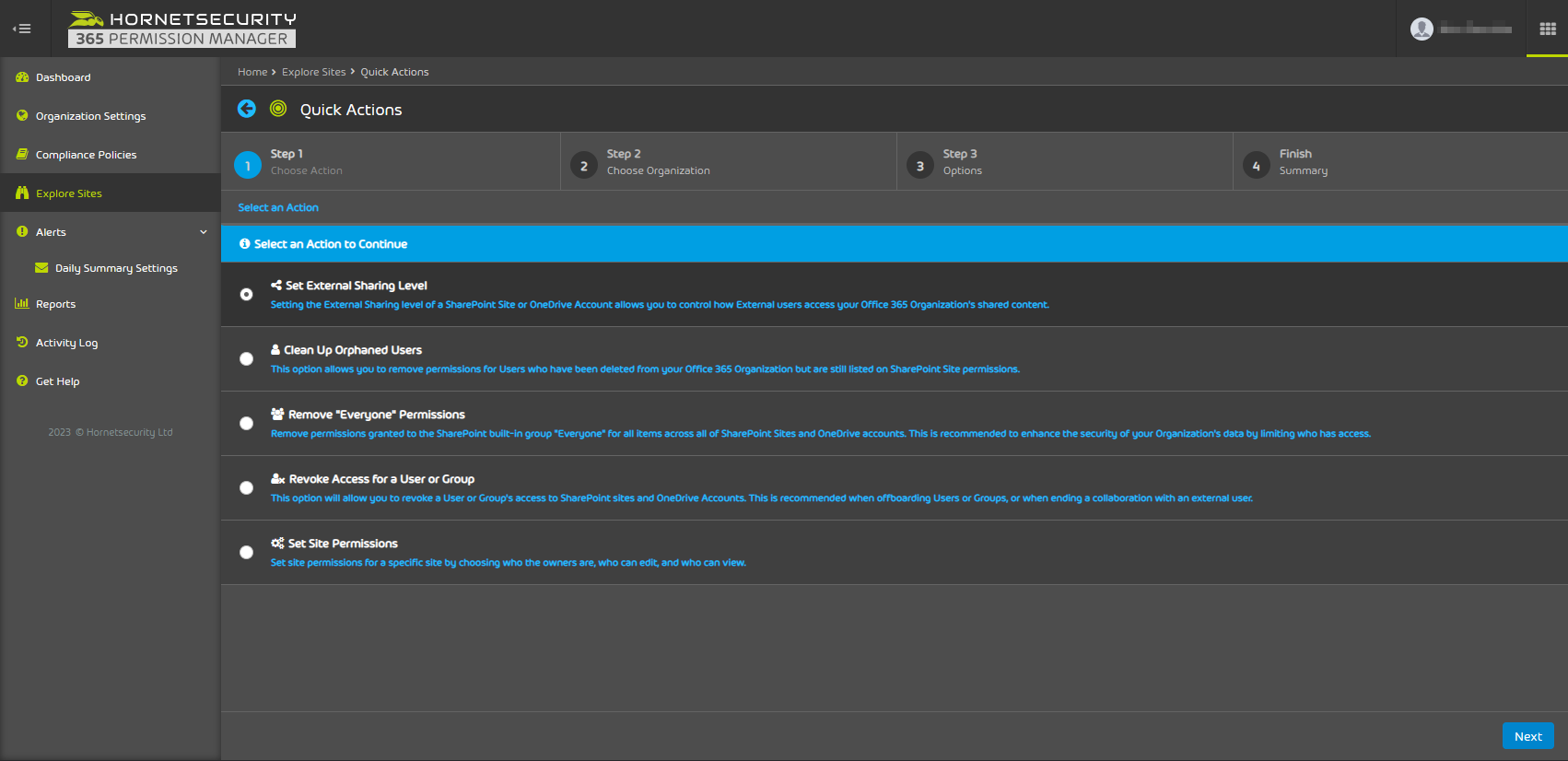
Take Quick Actions
Use Quick Actions to fix permissions on multiple sites at once or to set appropriate external sharing access level or to identify and remove access for groups providing indirect company wide access (e.g., “Everyone”). Quick Actions also lets you find and remove orphaned user permissions with a push of button.
Achieve Effective Compliance With Our GRC Service
If a user violates compliance rules, the Audit function gives you the option to approve or reject the violation by reverting the site settings according to the sites assigned compliance policy, or to remove access given to users and groups.
Receive Comprehensive Reporting
365 Permission Manager generates reports containing permission meta-data for documentation and compliance purposes. It shows which files are externally accessible to anonymous users or which are shared with guests. It also allows to select a particular group or user to get a full list on any site, file, or folder they have access to.