Ransomware Attacks Survey: 1 in 5 companies fall victim
About Hornetsecurity’s ransomware attacks survey
As those who are familiar with it will undoubtedly attest, ransomware is a nasty business. A malicious program made for devices (mainly computers), its aim is to lock data for the user – data which can only be unlocked, as the name suggests, if the user pays a ransom.
In our Knowledge Base, we’ve dedicated various sections to discussing every aspect of ransomware: what qualifies as ransomware, the sources of ransomware attacks, the best methods of ransomware protection, and much more.
The only thing left was to run a survey to find out whether companies truly understand the gravity of the threat posed by ransomware, and whether they are adequately protecting themselves from it. We also wanted to find out how often the average company falls victim to ransomware attacks, and how they resolve the situation. So, we organised a survey in which we asked these questions, along with a handful of others, and distributed it to hundreds of IT professionals around the world.
We received more than 820 survey responses, and the results have been eye-opening.
Below, we’ve prepared a breakdown of what we consider the most significant takeaways from the survey, and if you’d like to delve even deeper, you can find the full results of the ransomware survey here. With that out of the way, let’s get started.
Over 1 in every 5 companies falls victim to ransomware attacks
A staggering 21% of respondents answered ‘Yes’ to the question ‘Has your organisation been the victim of a ransomware attack to date?’ While this may seem high, it is consistent with data collected in our previous survey about email security, where we found that 1 in every 4 companies had suffered an email security breach. The findings confirm the high incidence of ransomware, making it one of the most common – and most effective – forms of cybercrime.
Being a victim of ransomware can be devastating. The average downtime a company experiences after a ransomware attack is 21 days, and while the cost of that downtime alone can be fatal for many companies, that is without taking into consideration the cost of data recovery, the payment of the ransom, and long-term brand damage. And the cost of the ransom is certainly not insignificant, with the average amount that companies were forced to pay in 2020 coming in at $170,404.
The next obvious question is, of these ransomware victims, how many ended up paying the ransom to recover their data and begin operating again?
Nearly 1 in 10 companies forced to pay ransom to recover data after ransomware attack
According to the survey, 9.2% of those companies that fell victim to a ransomware attack were left with no choice but to pay the ransom to recover their data. This statistic reveals that with the right awareness and protective measures, paying the ransom need not be the only option.
Over 90% of our respondents said that although they were attacked, they were able to recover their data from backup. That said, a few noted that while they were able to recover their data without having to pay the ransom, they still ended up losing files in the process, so they did not quite escape unscathed. This further highlights an essential point when it comes to ransomware protection – prevention is better (and significantly cheaper) than cure.
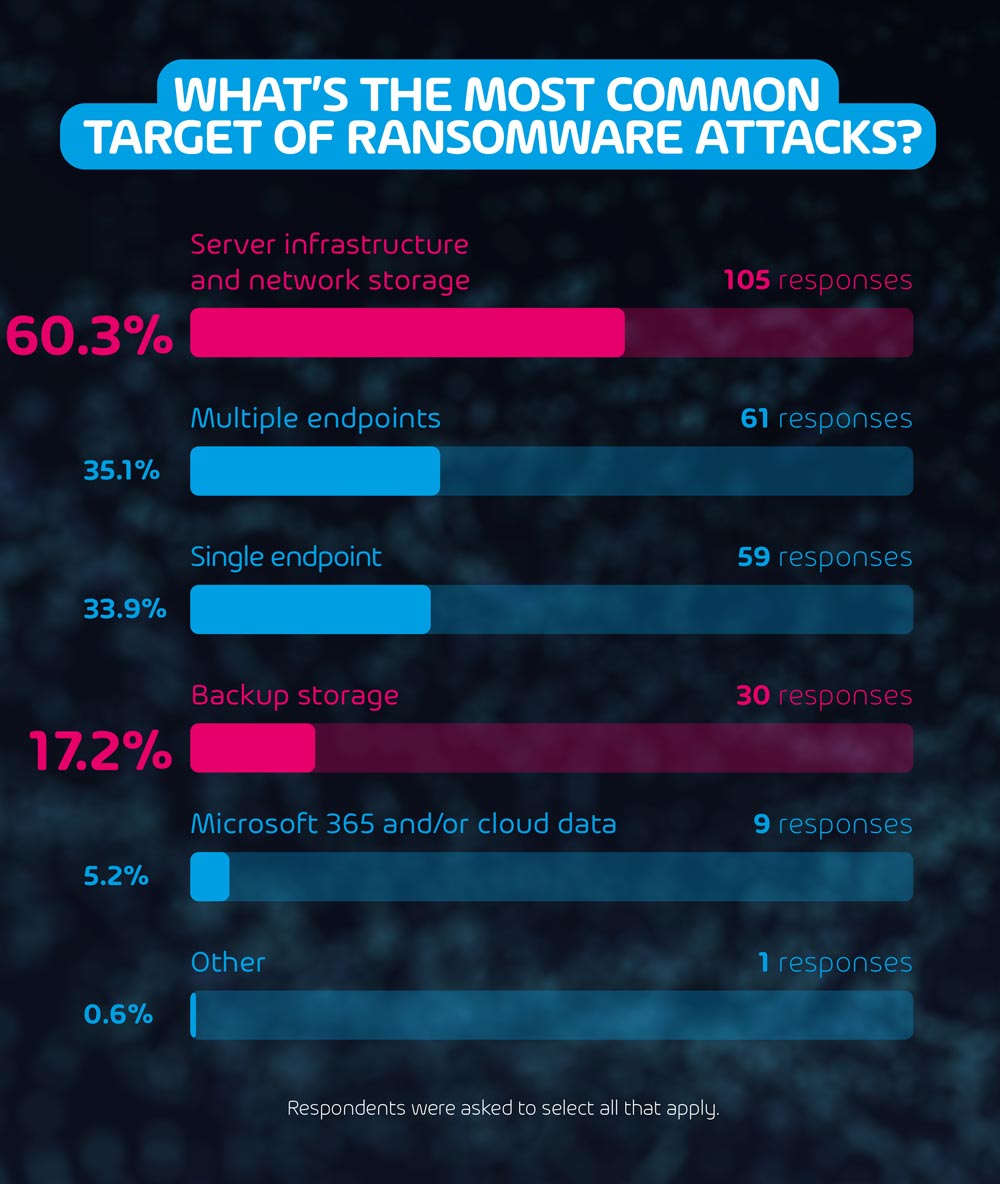
What’s the most common target of ransomware attacks?
The main aim of most ransomware attacks is to encrypt essential data that makes it impossible for a company to operate. Our survey findings support this. We found that 60.3% of reported ransomware attacks affected server infrastructure and network storage.
Network storage is normally used to store sensitive data which can be shared between multiple users simultaneously, and is utilised in nearly every company. Without access to this shared data, many organizations can be left stranded and unable to operate. It is therefore clear that having malware protection present at all levels of the organization is essential, particularly on end-points that have easy access to servers and network storage. This is especially true for companies with employees who work remotely and rely on access to network storage via VPN, as local storage is not an option.
15.2% of companies do not protect backups from ransomware
Backups are the lifeblood of any anti-ransomware strategy. If a shared drive is encrypted by malware, an IT team can recover the data from a recent backup without much data loss. That said, our survey found that over 17.2% of ransomware attacks on our respondents targeted backup data, revealing a loophole that scammers can exploit. If a company’s backup data is also encrypted, it becomes useless as a ransomware protection method.
The fact that over 15% of companies do not make an effort to protect their backups from ransomware is concerning. While taking regular backups protects from other potentially disastrous situations such as hardware failures, ransomware protection should also be one of its key functions. Most, if not all, ransomware attacks can be thwarted as long as a redundant backup schedule is maintained.
15.9% do not have a disaster recovery plan in place
IT disaster recovery plans (IT DRPs) are another essential component of protecting company data from unexpected threats. Being able to ensure business continuity in the event of a tech failure is essential. In this regard, our survey showed that a similar percentage of respondents that do not protect their backups also do not have a disaster recovery plan in place.
Furthermore, having an updated IT Disaster Recovery Plan protects you from more than just ransomware attacks. Human error, hardware failure, natural disasters – these are all reasons to have a strong recovery plan in place that you can deploy at a moment’s notice to minimize damage.
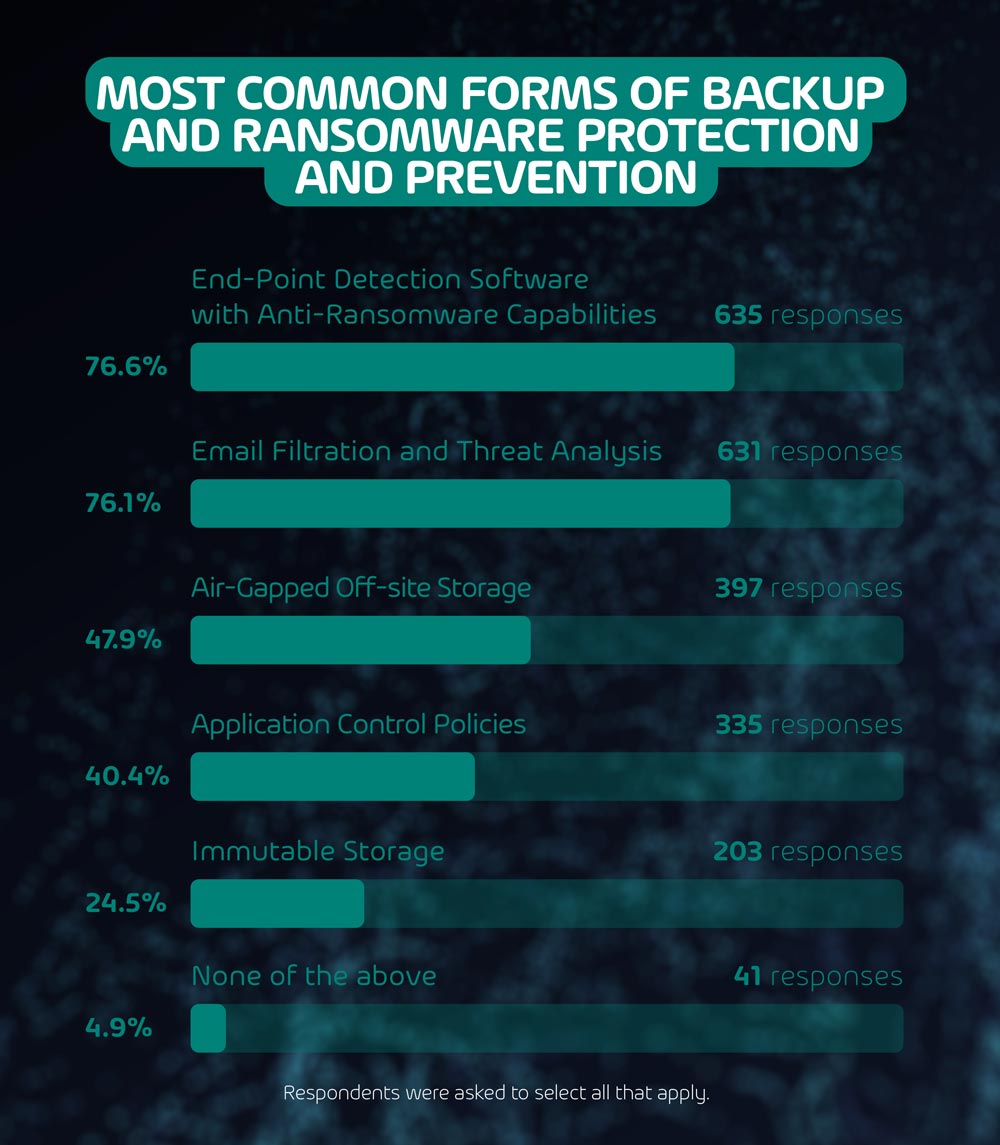
Most common forms of backup and ransomware protection and prevention
Many of our respondents understand the imminent threat that ransomware attacks pose. In fact, our survey shows that the threat of ransomware has changed the way 71.3% of companies backup their data.
The two most common forms of protection employed by our respondents, the survey revealed, are end-point detection software with anti-ransomware capabilities and email filtration and threat analysis. Both methods are used by 3 out of every 4 respondents (75.6% and 76.1% respectively). The former scans and analyses end-points (laptops, computers, mobile phones, tablets, etc.) for potential ransomware threats – raising the alarm if anything suspicious is found. Meanwhile, the latter performs the same function, but concentrates specifically on one of the most common sources of malware – email.
Both techniques are great examples of ransomware prevention, so what happens when a ransomware attack attempt gets through? That’s where air-gapped off-site storage comes in, which nearly half of our respondents use (47.8%). These backups are stored away from the main production line, and exist disconnected from any active operation. In this way, they ensure that, in the event of a natural disaster or ransomware attack, an uncompromised backup is always available.
In addition, 40.3% of our respondents mentioned that they use Application Control Policies as another way of preventing ransomware (or other malware) from taking hold at user end-points. These policies dictate which applications or programs may be launched on company devices, preventing an end-user from unknowingly launching malware on their device.
Nearly 1 in every 4 companies also indicated that they use immutable storage to protect themselves from ransomware attacks (24.5%). This form of storage is a backup service provided by specialized IT security companies, through which the data stored remains exactly as it is for the entirety of its existence. It cannot be modified, deleted, moved or otherwise tampered with at any time, by anyone. This makes it extremely effective at protecting data from nearly any threat.
28.7% of companies do not provide training to end-users on how to recognize and flag potential ransomware attacks
As found in our last survey on email security, end-users represent one of the most prominent threats to their own organizations. According to our findings, 62% of all email security breaches occurred due to user-compromised passwords and successful phishing attacks.
Social engineering, such as phishing or whaling, often yields excellent results for cybercriminals. These methods are designed to manipulate end-users into opening malicious files, giving access to or sending sensitive data, making payments, etc. To protect your company against this, providing training to end-users to recognize and flag potential threats can be one of the most effective ransomware prevention techniques. This said, less than 30% of surveyed companies make the effort to educate their employees on the subject, which would make all the difference.
Should you buy insurance that covers ransomware attacks?
35.7% of companies reported having purchased specific insurance cover for ransomware attacks. Doing so is likely not a bad idea in theory, however, it may not necessarily be feasible for many organizations. Covering ransomware cases involves accounting for the entire operation of the company, and may require certain preventative measures to be taken to qualify for the insurance. So, while it’s always a good idea to cover all your bases, we don’t suggest sacrificing a potential upgrade to your internal IT and backup security in favour of purchasing ransomware insurance.
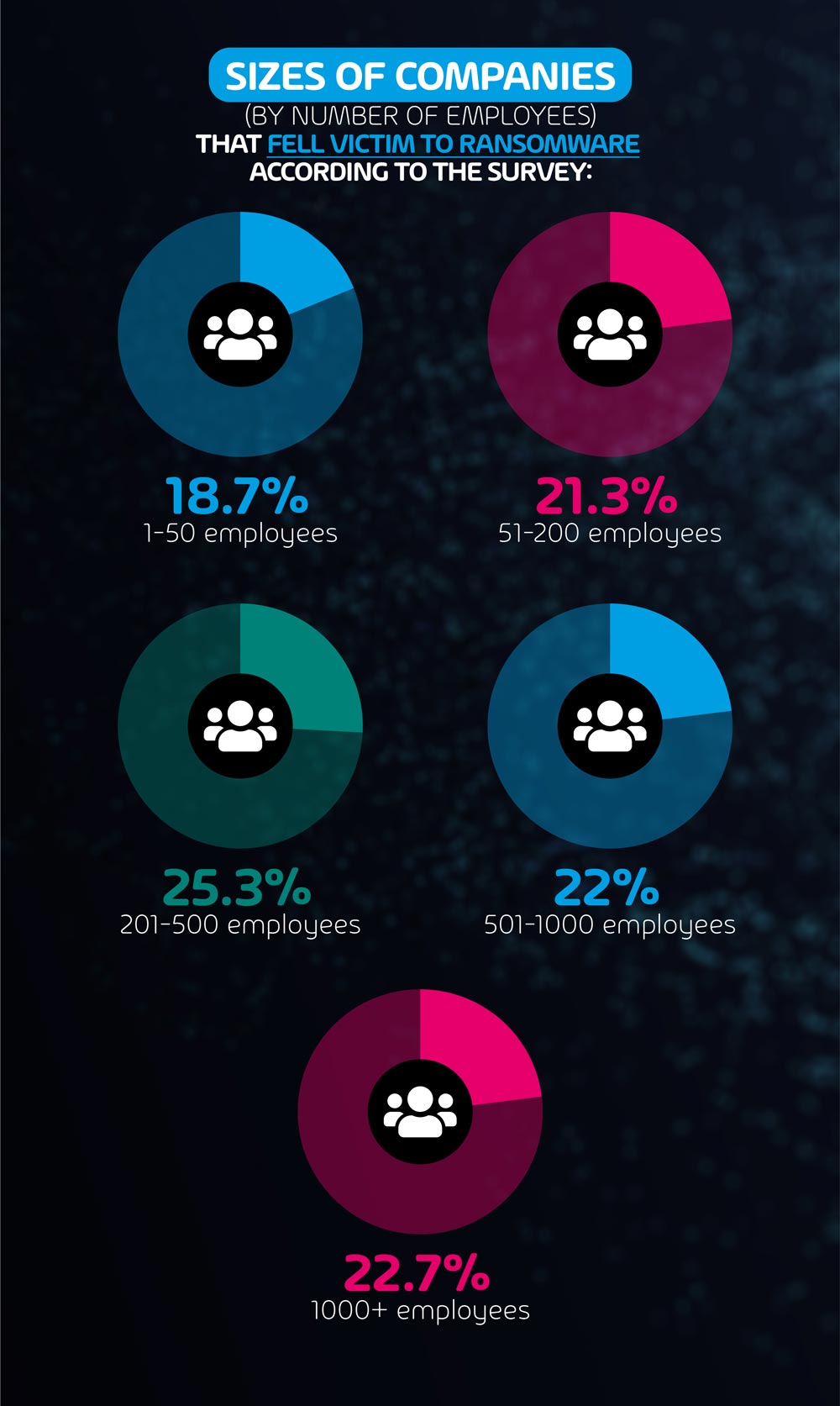
What size of company is most likely to suffer a ransomware attack?
A note to those companies that think they are too small to be targeted by malware: think again. Our survey data makes it clear that while companies with 1-50 employees are the least common target for ransomware attacks, almost 1 in every 5 of these organizations have fallen victim to an attack. Small companies don’t tend to prioritize IT security, even if they’re a high revenue organization, until something bad happens, making them an easy target for ransomware attacks.
The most vulnerable business size is that with 201-500 employees, with just over 1 in every 4 being the victim of an attack (25.3%). Organizations of this size are most likely at a stage where having a dedicated IT team is a no-brainer, but tight cybersecurity might not be a perceived priority just yet.
A final interesting observation is that companies with 1,000+ employees are more likely to be attacked by ransomware than those with 501-1,000 employees. This is likely due to the fact that while the largest organizations normally have the most stringent security measures, they also represent the largest potential pay-outs to cybercriminals.
Are leadership teams aware of the threat of ransomware attacks?
86.9% of companies claim that yes, their senior leadership team is aware of ransomware and the impact it can have. In fact, almost 40% of respondents indicated that their leadership is ‘actively involved in conversations and decision-making to help prepare the organization’.
This is not surprising, considering the increasing incidence of ransomware across most industries. Meanwhile, another 43.9% of respondents claim that while their leadership is aware of the threat, they are not quite as hands-on, leaving it to be dealt with by their IT departments.
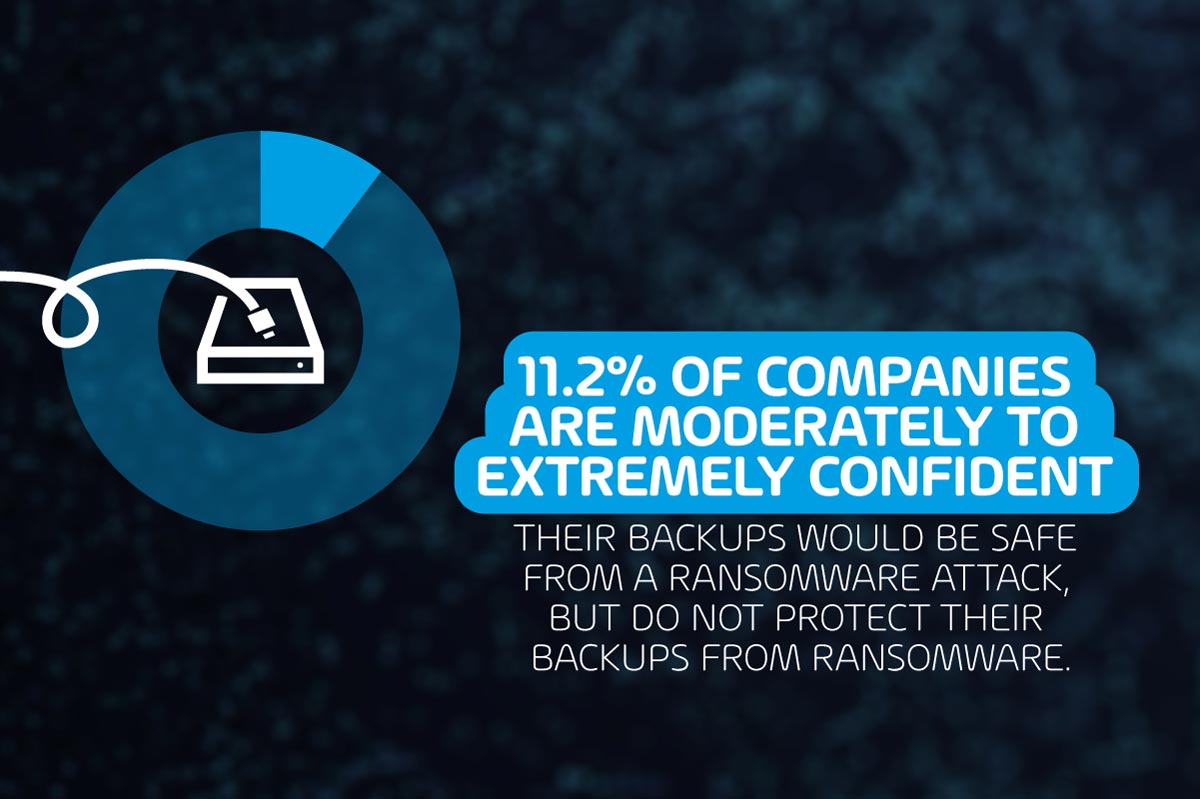
Over 1 in 10 companies claims to be confident that their backups would be safe from a ransomware attack, but do not protect their backups from ransomware
You read that right. More than 1 in every 10 companies (11.2%) represent the false sense of security that cybercriminals rely on to successfully perform their malicious operations. In fact, what is clear from these survey results is that any company, of any size, can be the victim of a ransomware attack. And while it may feel unlikely that it will happen to your company, the cost of recovery if unprepared is significantly higher than the cost of prevention.
Over 22% of companies think that Microsoft 365 data cannot be impacted by ransomware attacks, or do not know if it can be impacted
Many are under the impression that as long as data is stored in the cloud, it isn’t possible for ransomware attackers to target it. Over 1 in every 5 of our respondents either are not sure if Microsoft 365 data is vulnerable, or don’t think it is. The answer? While it’s not quite as simple for attackers to get hold of this data, it is certainly possible.
In fact, 5.1% of our respondents that reported being victims of a ransomware attack said that their Microsoft 365 and/or cloud data was affected in the attack.
In our previous survey on email security and Microsoft 365, we found that 68% of our respondents expected Microsoft 365 to keep them safe from email security breaches. In reality, as can also be seen here, third-party security solutions are an essential part of any cybersecurity protection plan.
So, what is the best form of ransomware protection?
While there is no silver bullet solution to completely rid your organisation of the threat of ransomware, there are multiple solutions that can work together to mitigate the threat. So, the best form of ransomware protection is definitely a holistic one. Here’s a list of precautions that your company can take:
Employee training
The level of training and awareness your end-users have could make or break a ransomware attack. Having employees who are capable of recognizing a potential ransomware threat and reporting it to the right people can be just as valuable as any piece of cybersecurity software.
An effective spam filter
Methods of concealing malicious files in emails are becoming more effective and difficult to detect, with some scammers successfully hiding them within PDFs and JPEGs. Therefore, having software capable of scanning email attachments and discarding malicious ones, such as Hornetsecurity Advanced Threat Protection (ATP) is an effective way of keeping scammers at bay.
Protect your backups
Most organizations understand that having backups for your most important data is a no-brainer. Protecting those backups, however, is just as important. As seen in the findings above, there are multiple tried and tested methods of back-up protection that can increase your company’s chances of escaping any ransomware threats unscathed.
For more on back-up protection, ransomware, or anything cybersecurity, visit our Knowledge Base.